A security researcher has shown that sensitive details could be exfiltrated from air-gapped pcs by using a novel method that leverages Wi-Fi alerts as a covert channel—surprisingly, with no requiring the existence of Wi-Fi hardware on the qualified devices.
Dubbed “AIR-FI,” the attack hinges on deploying a specially made malware in a compromised system that exploits “DDR SDRAM buses to deliver electromagnetic emissions in the 2.4 GHz Wi-Fi bands” and transmitting data atop these frequencies that can then be intercepted and decoded by close by Wi-Fi able devices these types of as smartphones, laptops, and IoT units prior to sending the information to distant servers controlled by an attacker.
The findings have been posted currently in a paper titled “AIR-FI: Generating Covert Wi-Fi Alerts from Air-Gapped Desktops” by Dr. Mordechai Guri, the head of R&D at Ben-Gurion College of the Negev’s Cyber-Security Research Centre, Israel.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
“The AIR-FI attack […] does not involve Wi-Fi relevant components in the air-gapped computers,” Dr. Guri outlined.
“Instead, an attacker can exploit the DDR SDRAM buses to make electromagnetic emissions in the 2.4 GHz Wi-Fi bands and encode binary info on top rated of it.”
Guri, previously this May perhaps, also demonstrated Ability-SUPPLaY, a different system that enables the malware to exploit a computer’s electrical power source unit (PSU) to engage in sounds and use it as an out-of-band, secondary speaker to leak data.
Air-gapped personal computers — machines with no network interfaces — are regarded as a requirement in environments where by sensitive details is associated in an try to decrease the risk of info leakage.
So in purchase to have out attacks from these units, it is often necessary that the transmitting and receiving equipment be positioned in close physical proximity to one particular one more and that they are infected with the correct malware to build the conversation connection.
Be AIR-FI is special in that the system neither depends on a Wi-Fi transmitter to produce indicators nor involves kernel motorists, special privileges these as root, or obtain to components methods to transmit the facts.
What is more, the covert channel is effective even from within just an isolated digital equipment and has an endless record of Wi-Fi enabled units that can be hacked by an attacker to act as a potential receiver.
The kill chain in by itself consists of an air-gapped computer onto which the malware is deployed by using social engineering lures, self-propagating worms such as Agent.BTZ, tampered USB flash drives, or even with the enable of destructive insiders.
It also necessitates infecting Wi-Fi able units co-found in the air-gapped network by compromising the firmware of the Wi-Fi chips to put in malware able of detecting and decoding the AIR-FI transmission and exfiltrating the information above the Internet.
With this set up in place, the malware on the concentrate on procedure collects the suitable knowledge (e.g., private files, credentials, encryption keys), which is then encoded and transmitted in the Wi-Fi band at 2.4 GHz frequency applying the electromagnetic emissions generated from the DDR SDRAM buses made use of to exchange data involving the CPU and the memory, as a result defeating air-gap isolation.
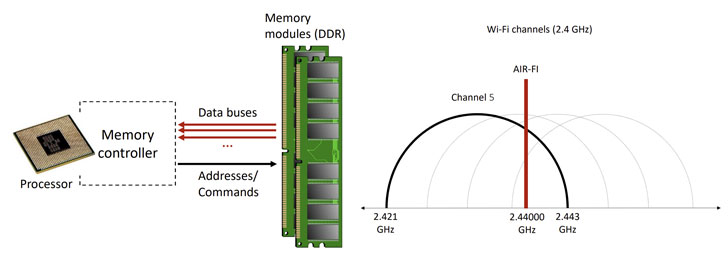
To crank out the Wi-Fi alerts, the attack would make use of the knowledge bus (or memory bus) to emit electromagnetic radiation at a frequency correlated to the DDR memory module and the memory read/produce operations executed by procedures at this time running in the procedure.
AIR-FI was evaluated using 4 varieties of workstations with unique RAM and hardware configurations as very well as utilizing application-described radio (SDR) and a USB Wi-Fi network adapter as receivers, obtaining that the covert channel can be efficiently managed at distances up to several meters from air-gapped pcs and attaining bit prices ranging from 1 to 100 little bit/sec, depending on the form and method of receiver made use of.
If something, the new investigation is nonetheless one more reminder that electromagnetic, acoustic, thermal, and optical parts keep on to be beneficial vectors to mount complex exfiltration attacks towards air-gapped services.
As a countermeasure, Dr. Guri proposes zone protections to safeguard towards electromagnetic attacks, enabling intrusion detection methods to keep an eye on and examine for procedures that conduct intensive memory transfer functions, jamming the signals, and applying Faraday shields to block the covert channel.
The AIR-FI malware exhibits “how attackers can exfiltrate knowledge from air-gapped computers to a nearby Wi-Fi receiver via Wi-Fi signals,” he additional.
“Modern day IT environments are equipped with many forms of Wi-Fi able gadgets: smartphones, laptops, IoT products, sensors, embedded systems, and good watches, and other wearables products. The attacker can potentially hack this kind of equipment to get the AIR-FI transmissions from air-gapped computers.”
Uncovered this article fascinating? Comply with THN on Fb, Twitter and LinkedIn to read through additional distinctive content material we put up.
Some parts of this report are sourced from:
thehackernews.com


 Spotify notifies customers of breach, files under CCPA
Spotify notifies customers of breach, files under CCPA