A Chinese cyber espionage team has been joined to a string of intrusion functions concentrating on Israeli govt establishments, IT providers, and telecommunications companies at least due to the fact 2019.
FireEye’s Mandiant threat intelligence arm attributed the marketing campaign to an operator it tracks as “UNC215”, a Chinese espionage operation that’s believed to have singled out companies about the environment dating back again as considerably as 2014, linking the team with “minimal confidence” to an advanced persistent risk (APT) greatly recognized as APT27, Emissary Panda, or Iron Tiger.
“UNC215 has compromised businesses in the government, technology, telecommunications, protection, finance, amusement, and health and fitness treatment sectors,” FireEye’s Israel and U.S. risk intel teams explained in a report posted currently.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code

“The team targets details and corporations which are of wonderful fascination to Beijing’s money, diplomatic, and strategic goals,” the results reflecting a relentless appetite for defense-connected tricks amid hacking groups.
Early attacks perpetrated by the collective is claimed to have exploited a Microsoft SharePoint vulnerability (CVE-2019-0604) as a stepping stone toward infiltrating authorities and educational networks to deploy web shells and FOCUSFJORD payloads at targets in the Center East and Central Asia. Initial described by the NCC Team in 2018, FOCUSFJORD, also termed HyperSSL and Sysupdate, is a backdoor which is part of an arsenal of instruments put to use by the Emissary Panda actor.
On gaining an original foothold, the adversary follows an recognized sample of conducting credential harvesting and internal reconnaissance to identify crucial programs inside of the goal network, ahead of carrying out lateral motion functions to put in a custom implant named HyperBro that arrives with abilities these types of as monitor capture and keylogging.
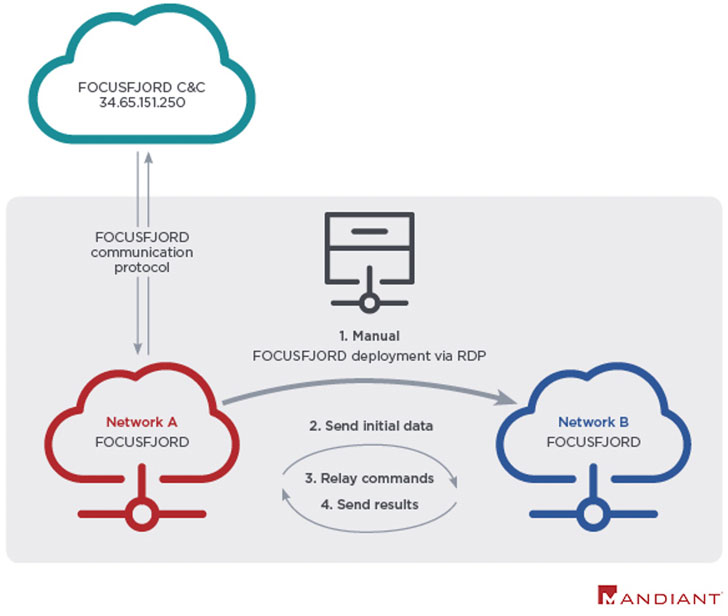
Each and every period of the attack is marked by noteworthy efforts undertaken to hinder detection by eradicating any traces of residual forensic artifacts from compromised devices, when concurrently strengthening the FOCUSFJORD backdoor in reaction to security vendor reports, concealing command-and-control (C2) infrastructure by employing other sufferer networks to proxy their C2 instructions, and even incorporating bogus flags these types of as deploying a web shell termed SEASHARPEE that is involved with Iranian APT teams in an endeavor to mislead attribution.

What is far more, in a 2019 procedure versus an Israeli federal government network, UNC215 acquired obtain to the main goal by means of remote desktop protocol (RDP) connections from a dependable 3rd-party making use of stolen qualifications, abusing it to deploy and remotely execute the FOCUSFJORD malware, the cybersecurity organization famous.
“The activity […] demonstrates China’s constant strategic curiosity in the Center East,” the scientists concluded. “This cyber espionage exercise is occurring versus the backdrop of China’s multi-billion-greenback investments related to the Belt and Road Initiative (BRI) and its curiosity in Israeli’s strong technology sector.”
“China has carried out a lot of intrusion strategies alongside the BRI route to monitor potential obstructions—political, financial, and security—and we anticipate that UNC215 will keep on targeting governments and organizations involved in these critical infrastructure projects in Israel and the broader Center East in the around- and mid-term,” the groups added.
Observed this write-up appealing? Adhere to THN on Facebook, Twitter and LinkedIn to read a lot more distinctive content we put up.
Some areas of this post are sourced from:
thehackernews.com


 NCSC taps security startups to help defend the UK from cyber threats
NCSC taps security startups to help defend the UK from cyber threats