The clearnet and dark web payment portals operated by the Conti ransomware group have absent down in what appears to be an endeavor to change to new infrastructure soon after information about the gang’s internal workings and its users were being built general public.
In accordance to MalwareHunterTeam, “whilst the two the clearweb and Tor domains of the leak web site of the Conti ransomware gang is on the internet and doing the job, both equally their clearweb and Tor domains for the payment internet site (which is clearly additional significant than the leak) is down.”
It is not crystal clear what prompted the shutdown, but the enhancement will come as Swiss cybersecurity firm PRODAFT available an unprecedented look into the group’s ransomware-as-a-support (RaaS) model, wherein the developers offer or lease their ransomware technology to affiliates employed from darknet message boards, who then carry out attacks on their behalf when also netting about 70% of each individual ransom payment extorted from the victims.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount

The consequence? 3 users of the Conti workforce have been recognized so considerably, every single playing the roles of admin (“Tokyo”), assistant (“it_work_support@xmpp[.]jp”), and recruiter (“IT_Get the job done”) to draw in new affiliate marketers into their network.
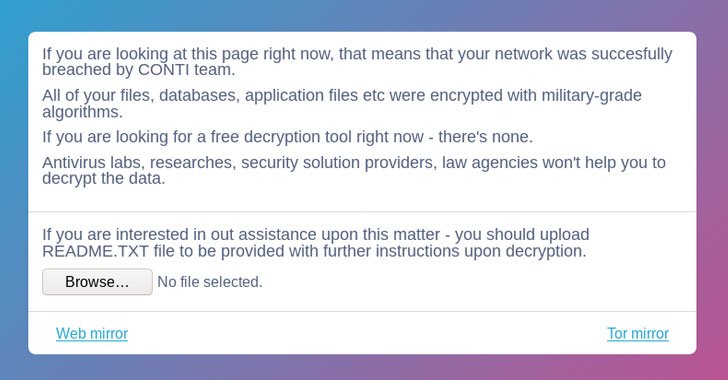
Even though ransomware attacks work by encrypting the victims’ delicate info and rendering it inaccessible, danger actors have significantly latched on to a two-pronged method identified as double extortion to demand from customers a ransom payment for decrypting the data and threaten to publicly publish the stolen data if the payment is not been given inside a certain deadline.
“Conti consumers – affiliate danger actors – use [a digital] administration panel to develop new ransomware samples, regulate their victims, and collect details on their attacks,” pointed out the scientists, detailing the syndicate’s attack kill chain leveraging PrintNightmare (CVE-2021-1675, CVE-2021-34527, and CVE-2021-36958) and FortiGate (CVE-2018-13374 and CVE-2018-13379) vulnerabilities to compromise unpatched devices.
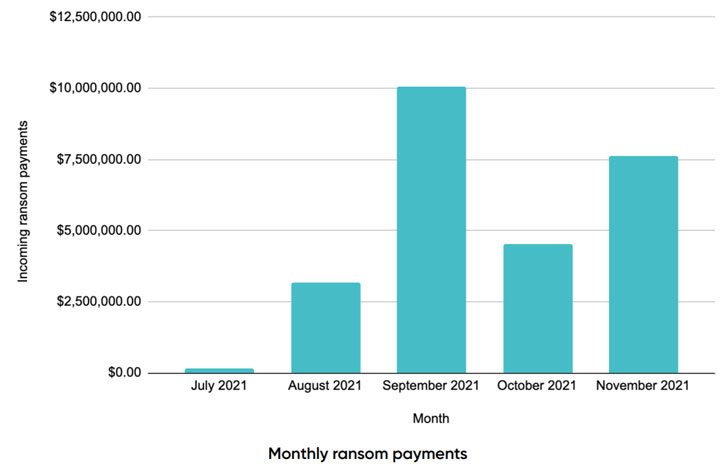
Emerging on the cybercrime landscape in October 2019, Conti is considered to be the work of a Russia-dependent threat team called Wizard Spider, which is also the operator of the infamous TrickBot banking malware. Due to the fact then, at least 567 various organizations have had their small business-critical details exposed on the target shaming site, with the ransomware cartel receiving more than 500 bitcoin ($25.5 million) in payments given that July 2021.

What is actually more, an assessment of ransomware samples and the bitcoin wallet addresses used for obtaining the payments has uncovered a link among Conti and Ryuk, with both of those families closely banking on TrickBot, Emotet, and BazarLoader for in fact providing the file-encrypting payloads onto victim’s networks by way of email phishing and other social engineering techniques.
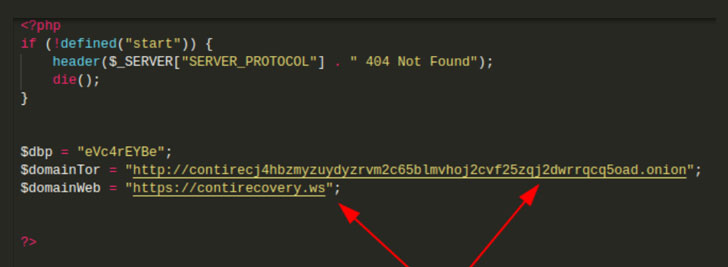
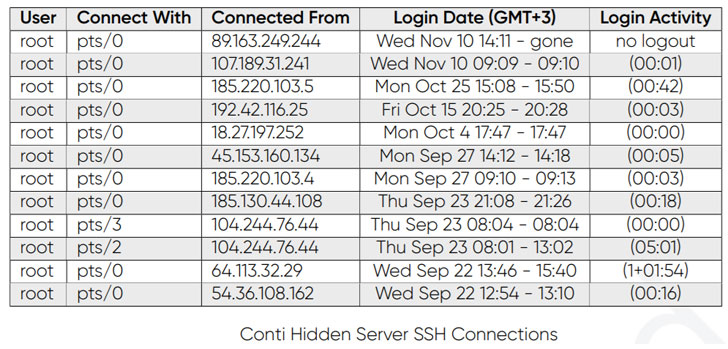
PRODAFT mentioned it was also equipped to obtain obtain to the group’s restoration service and an admin administration panel hosted as a Tor concealed service on an Onion domain, revealing in depth information of a clearnet web page identified as “[contirecovery[.]ws]” that incorporates guidelines for getting decryption keys from the affiliate marketers. Interestingly, an investigation into Conti’s ransomware negotiation approach published by Staff Cymru past thirty day period highlighted a similar open up web URL named “contirecovery[.]facts.”
“In order to tackle the complicated challenge of disrupting cybercriminal organizations, public and non-public forces will need to perform collaboratively with just one a different to greater comprehend and mitigate the broader lawful and business effect of the risk,” the researchers reported.
Discovered this short article intriguing? Follow THN on Fb, Twitter and LinkedIn to go through more exceptional material we submit.
Some elements of this post are sourced from:
thehackernews.com

 New Side Channel Attacks Re-Enable Serious DNS Cache Poisoning Attacks
New Side Channel Attacks Re-Enable Serious DNS Cache Poisoning Attacks