An evaluation of two ransomware attacks has discovered overlaps in the practices, tactics, and methods (TTPs) involving BlackCat and BlackMatter, indicating a robust link between the two groups.
Though it truly is regular of ransomware groups to rebrand their functions in reaction to improved visibility into their attacks, BlackCat (aka Alphv) marks a new frontier in that the cyber criminal offense cartel is constructed out of affiliates of other ransomware-as-a-service (RaaS) operations.
BlackCat very first emerged in November 2021 and has since targeted a number of organizations around the world above the previous few months. It has been referred to as out for being similar to BlackMatter, a limited-lived ransomware loved ones that originated from DarkSide, which attracted notoriety for its superior-profile attack on Colonial Pipeline in May 2021.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code

In an interview with Recorded Future’s The Record previous month, a BlackCat agent dismissed rumors that it’s a rebranding of BlackMatter, even though noting that it truly is created up of affiliates related with other RaaS teams.
“In part, we are all related to gandrevil [GandCrab / REvil], blackside [BlackMatter / DarkSide], mazegreggor [Maze / Egregor], lockbit, and so forth., since we are adverts (aka affiliates),” the unnamed consultant was quoted as indicating. “We borrowed their advantages and eliminated their shortcomings.”
“BlackCat appears to be to be a circumstance of vertical enterprise expansion,” Cisco Talos scientists Tiago Pereira and Caitlin Huey stated. “In essence, it is really a way to manage the upstream provide chain by producing a service that is important to their enterprise (the RaaS operator) superior suited for their demands and introducing a different source of income.”
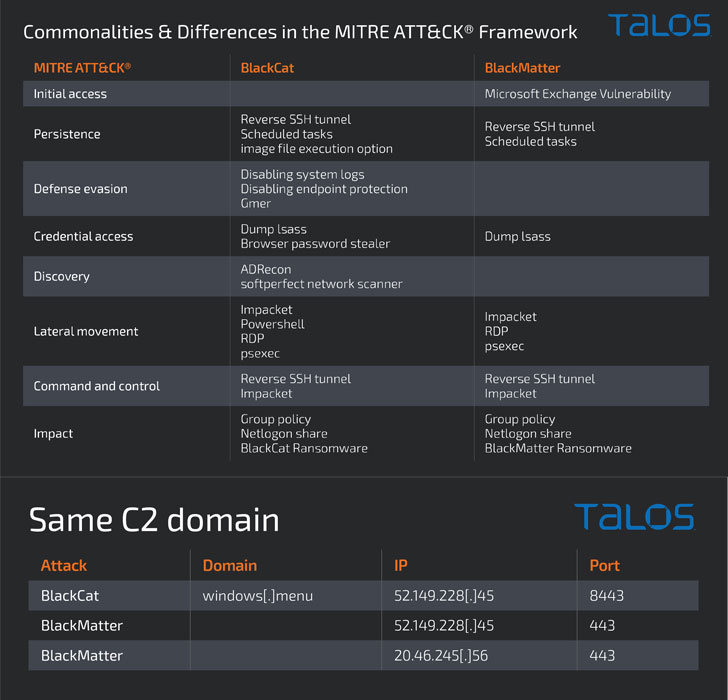
What is a lot more, the cybersecurity company said it noticed a variety of commonalities involving a BlackMatter attack in September 2021 and that of a BlackCat attack from December 2021, including the applications and the file names utilized as perfectly as a area employed to preserve persistent accessibility to the goal network.
This overlapping use of the same command-and-management tackle has elevated the likelihood that the affiliate that applied BlackMatter was possible one particular of the early adopters of BlackCat, with each the attacks having much more than 15 times to arrive at the encryption stage.
“As we have observed a number of periods in advance of, RaaS services come and go. Their affiliate marketers, even so, are most likely to just move on to a new support. And with them, a lot of of the TTPs are very likely to persist,” the scientists reported.
The conclusions occur as BlackBerry detailed a new .NET-primarily based ransomware spouse and children termed LokiLocker that not only encrypts the information but also incorporates an optional wiper operation which is made to erase all non-program files and overwrite the master boot history (MBR) ought to a victim refuse to fork out up inside a specified timeframe.
“LokiLocker will work as a limited-accessibility ransomware-as-a-support scheme that appears to be offered to a fairly small quantity of meticulously vetted affiliates guiding shut doorways,” the researchers said. Active due to the fact at the very least August 2021, a bulk of victims detected so considerably are concentrated in Eastern Europe and Asia.
Uncovered this report intriguing? Observe THN on Facebook, Twitter and LinkedIn to browse additional special information we put up.
Some parts of this posting are sourced from:
thehackernews.com




 IT Pro News In Review: Job losses at Arm, warnings over Kaspersky software, Microsoft using ads
IT Pro News In Review: Job losses at Arm, warnings over Kaspersky software, Microsoft using ads