A nascent info-thieving malware bought and distributed on underground Russian underground community forums has been written in Rust, signalling a new pattern where by risk actors are more and more adopting unique programming languages to bypass security protections, evade investigation, and hamper reverse engineering endeavours.
Dubbed “Ficker Stealer,” it can be notable for being propagated by using Trojanized web hyperlinks and compromised web-sites, luring in victims to fraud landing internet pages purportedly providing absolutely free downloads of legit paid companies like Spotify New music, YouTube Top quality, and other Microsoft Retail outlet purposes.


Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
“Ficker is marketed and distributed as Malware-as-a-Company (MaaS), by way of underground Russian on-line boards,” BlackBerry’s analysis and intelligence team stated in a report printed these days. “Its creator, whose alias is @ficker, features a number of paid packages, with unique amounts of membership costs to use their destructive application.”
Very first viewed in the wild in August 2020, the Windows-centered malware is applied to steal delicate facts, which include login qualifications, credit history card information and facts, cryptocurrency wallets, and browser info, in addition to functioning as a instrument to grab sensitive documents from the compromised machine, and act as a downloader to obtain and execute further next-stage malware.
Additionally, Ficker is identified to be shipped via spam strategies, which include sending focused phishing e-mails with weaponized macro-based Excel document attachments that, when opened, drops the Hancitor loader, which then injects the closing payload using a system known as system hollowing to keep away from detection and mask its things to do.
In the months that adopted since its discovery, the digital menace has been identified leveraging DocuSign-themed lures to put in a Windows binary from an attacker-controlled server. CyberArk, in an evaluation of the Ficker malware past month, famous its heavily obfuscated mother nature and Rust roots, earning the examination extra difficult, if not prohibitive.

“As soon as the pretend DocuSign doc is opened and its malicious macro code is allowed to operate, Hancitor will usually attain out to its command-and-command (C2) infrastructure to acquire a malicious URL containing a sample of Ficker to down load,” BlackBerry scientists stated.
Apart from relying on obfuscation tactics, the malware also incorporates other anti-investigation checks that prevent it from working on virtualized environments and on victim machines located in Armenia, Azerbaijan, Belarus, Kazakhstan, Russia, and Uzbekistan. Also deserving of specific observe is that, unlike classic info stealers, Ficker is created to execute the commands and exfiltrate the details directly to the operators as a substitute of creating the stolen facts to disk.
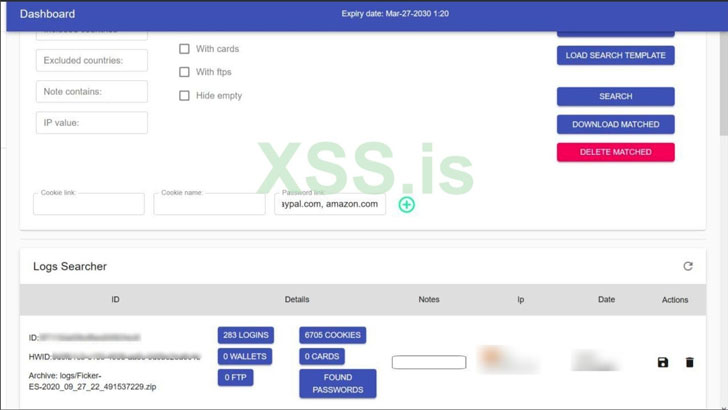
“The malware also has monitor-capturing abilities, which let the malware’s operator to remotely seize an picture of the victim’s monitor. The malware also permits file-grabbing and extra downloading abilities after relationship to its C2 is proven,” the scientists claimed. “When info is despatched back again to Ficker’s C2, the malware operator can accessibility and research for all exfiltrated info.”
Located this write-up appealing? Abide by THN on Fb, Twitter and LinkedIn to browse a lot more exceptional written content we post.
Some areas of this posting are sourced from:
thehackernews.com

 Palo Alto Networks’ Prisma Access achieves FedRAMP authorization
Palo Alto Networks’ Prisma Access achieves FedRAMP authorization