As a lot of as 75 applications on Google Perform and 10 on Apple App Retail outlet have been identified engaging in advert fraud as section of an ongoing marketing campaign that commenced in 2019.
The most recent iteration, dubbed Scylla by On-line fraud-prevention organization HUMAN Security, follows related attack waves in August 2019 and late 2020 that go by the codename Poseidon and Charybdis, respectively.
Prior to their elimination from the app storefronts, the apps experienced been collectively installed extra than 13 million situations.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code

The first Poseidon operation comprised more than 40 Android applications that ended up intended to exhibit ads out of context or hidden from the look at of the machine user.
Charybdis, on the other hand, was an enhancement about the previous by generating use of code obfuscation ways to goal advertising platforms.
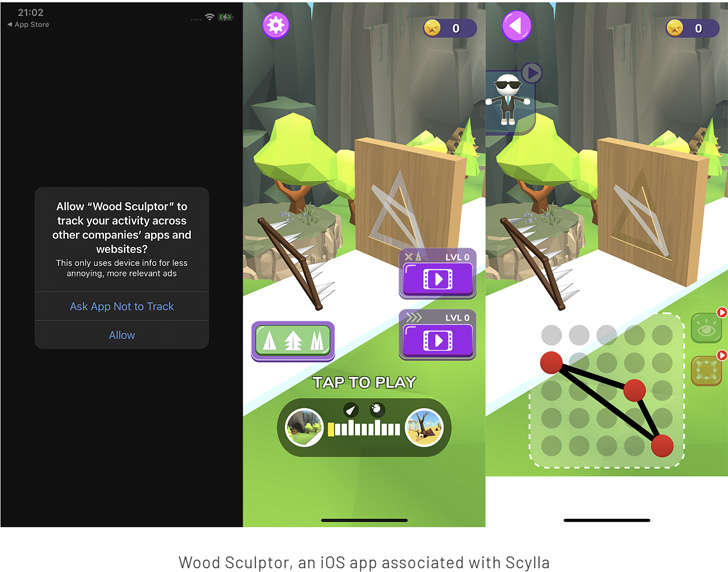
Scylla presents the newest adaption of the plan in that it expands further than Android to make a foray into the iOS ecosystem for the first time, together with relying on extra levels of code roundabout working with the Allatori device.
These applications, when set up, are engineered to commit distinctive varieties of ad fraud, marking a substantial move up in sophistication from past variants.

These include spoofing well known applications this sort of as streaming expert services to trick advertising SDKs into positioning advertisements, serving out-of-context and “concealed” adverts via off-screen WebViews, and creating fraudulent ad clicks to earnings off ads.
“In layman’s conditions, the danger actors code their apps to pretend to be other applications for promoting reasons, normally since the application they’re pretending to be is really worth a lot more to an advertiser than the application would be by itself,” the firm claimed.
As always, customers are advised to scrutinize apps prior to downloading them, and steer clear of third-party app shops on the web that could harbor malicious apps.
Observed this article attention-grabbing? Adhere to THN on Facebook, Twitter and LinkedIn to read extra exclusive material we post.
Some components of this write-up are sourced from:
thehackernews.com


 Why Continuous Security Testing is a Must for Organizations Today
Why Continuous Security Testing is a Must for Organizations Today