Scientists on Tuesday exposed particulars of a new banking trojan focusing on company end users in Brazil at minimum due to the fact 2019 throughout many sectors these kinds of as engineering, healthcare, retail, production, finance, transportation, and federal government.
Dubbed “Janeleiro” by Slovak cybersecurity organization ESET, the malware aims to disguise its real intent by using lookalike pop-up windows that are built to resemble the web sites of some of the most significant banking companies in the region, such as Itaú Unibanco, Santander, Banco do Brasil, Caixa Econômica Federal, and Banco Bradesco.
“These pop-ups incorporate faux kinds, aiming to trick the malware’s victims into moving into their banking credentials and individual details that the malware captures and exfiltrates to its [command-and-control] servers,” ESET researchers Facundo Muñoz and Matías Porolli reported in a produce-up.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
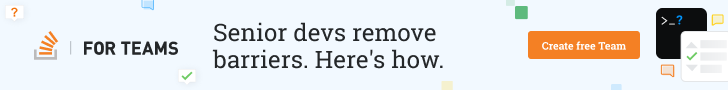
This modus operandi is not new to banking trojans. In August 2020, ESET uncovered a Latin American (LATAM) banking trojan known as Mekotio that displayed identical pretend pop-up windows to its victims in an try to entice them into divulging sensitive facts.
But Janeleiro stands out for a variety of good reasons. A person, the malware is composed in Visible Simple .NET, which the scientists say is a “big deviation” from the Delphi programming language that is usually most popular by the menace actors in the location. It also will not rely on custom encryption algorithms or more layers of obfuscation and even reuses code taken from NjRAT, a rarity amid LATAM banking trojans.
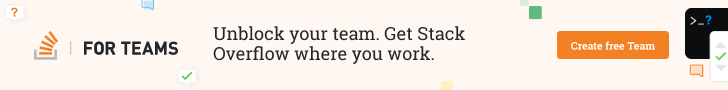
The attack commences with a phishing email that purports to be an unpaid invoice, which has a connection that, when clicked, downloads a ZIP file. The archive arrives with an MSI installer that loads the key trojan DLL, which subsequently fetches the IP addresses of the command-and-regulate (C2) servers from a GitHub page evidently created by the malware authors. The final website link in the infection chain includes ready for instructions from the C2 server.
Hence in the party, a user visits the internet site of a banking entity of curiosity, Janeleiro connects to the C2 server and dynamically displays the fraudulent pop-up windows, and captures the keystrokes and other details entered in the fake sorts.
ESET reported it learned four versions of Janeleiro among September 2019 to March 2021.
This is not the first time banking trojans have been noticed in the wild that have singled out Brazilian buyers. Final year, Kaspersky in depth at the very least 4 malware households — Guildma, Javali, Melcoz, and Grandoreiro — which had been identified to target financial establishments in Brazil, Latin The us, and Europe.
Then earlier this January, ESET disclosed a new Delphi-centered banking trojan named “Vadokrist” that was identified to concentrate on Brazil solely whilst sharing similarities with other malware families like Amavaldo, Casbaneiro, Grandoreiro, and Mekotio.
“Janeleiro follows the one of a kind blueprint for the core implementation of the faux pop-up windows as several LATAM banking trojans, this does not seem to be to be a coincidence or inspiration: this actor employs and distributes Janeleiro sharing the similar infrastructure as some of the most prominent of these energetic malware families,” the scientists concluded.
Uncovered this report appealing? Follow THN on Fb, Twitter and LinkedIn to study far more exclusive content we put up.
Some pieces of this short article are sourced from:
thehackernews.com

 Bug allows attackers to hijack Windows time sync software used to track security incidents
Bug allows attackers to hijack Windows time sync software used to track security incidents