Cybersecurity scientists took the wraps off an ongoing surveillance campaign directed towards Colombian authorities establishments and non-public corporations in the energy and metallurgical industries.
In a report revealed by ESET on Tuesday, the Slovak internet security enterprise stated the attacks — dubbed “Procedure Spalax” — started in 2020, with the modus operandi sharing some similarities to an APT group targeting the place because at the very least April 2018, but also diverse in other techniques.
The overlaps appear in the kind of phishing e-mail, which have equivalent topics and fake to arrive from some of the same entities that were applied in a February 2019 procedure disclosed by QiAnXin researchers, and subdomain names employed for command-and-control (C2) servers.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
Nevertheless, the two campaigns diverge in the attachments made use of for phishing emails, the remote entry trojans (RATs) deployed, and the C2 infrastructure used to fetch the malware dropped.
The attack chain commences with the targets acquiring phishing email messages that lead to the obtain of malicious documents, which are RAR archives hosted on OneDrive or MediaFire that contains many droppers liable for decrypting and functioning RATs these as Remcos, njRAT, and AsyncRAT on a victimized personal computer.
The phishing emails address a extensive vary of subject areas, including those about driving infractions, show up at courtroom hearings, and acquire required COVID-19 tests, consequently increasing the chance that unsuspecting end users will open the messages.
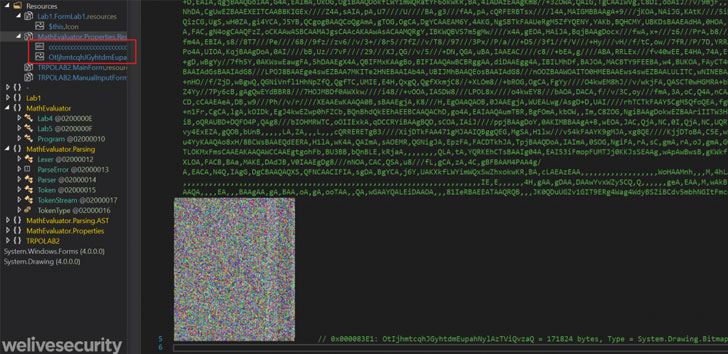
In an alternate situation noticed by ESET, the attackers were being also identified to use closely obfuscated AutoIt droppers that employed shellcode to decrypt the payload and one more to inject it into an currently operating procedure.
The RATs not only arrive with capabilities for remote control but also to spy on targets by capturing keystrokes, recording screenshots, thieving clipboard information, exfiltrating delicate files, and even downloading and executing other malware.
ESET’s analysis also exposed a scalable C2 architecture operated using a Dynamic DNS support that allowed them to dynamically assign a area title to an IP tackle from a pool of 70 unique domain names and 24 IP addresses in the second 50 % of 2020 on your own.
“Focused malware attacks from Colombian entities have been scaled up considering the fact that the strategies that had been explained past yr,” the scientists concluded. “The landscape has improved from a campaign that experienced a handful of C2 servers and area names to a marketing campaign with very significant and quickly-modifying infrastructure with hundreds of area names utilized given that 2019.”
Uncovered this short article exciting? Abide by THN on Fb, Twitter and LinkedIn to browse extra distinctive articles we post.
Some pieces of this article are sourced from:
thehackernews.com


 Google: Attacker ‘likely’ had access to Android zero-day vulnerabilities
Google: Attacker ‘likely’ had access to Android zero-day vulnerabilities