Cybersecurity scientists on Tuesday launched new findings that reveal a yr-lengthy cellular espionage marketing campaign versus the Kurdish ethnic team to deploy two Android backdoors that masquerade as respectable apps.
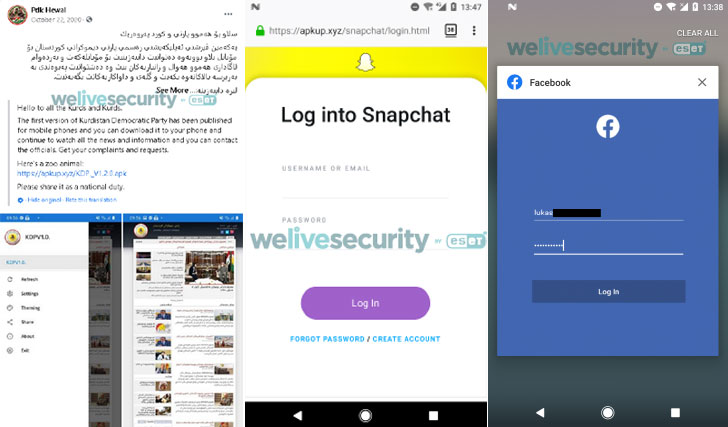
Active due to the fact at the very least March 2020, the attacks leveraged as quite a few as six devoted Fb profiles that claimed to offer news, two of which were being aimed at Android buyers although the other four shared pro-Kurd material, only to share spying apps on Fb general public groups. All six profiles have considering the fact that been taken down.
“It targeted the Kurdish ethnic team by way of at minimum 28 destructive Fb posts that would direct opportunity victims to down load Android 888 RAT or SpyNote,” ESET researcher Lukas Stefanko stated. “Most of the malicious Facebook posts led to downloads of the industrial, multi-system 888 RAT, which has been out there on the black industry given that 2018.”

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
The Slovakian cybersecurity agency attributed the attacks to a team it refers to as BladeHawk.
In one particular occasion, the operators shared a Fb publish urging users to download a “new snapchat” application which is made to seize Snapchat credentials via a phishing website. A overall of 28 rogue Fb posts have been identified as component of the newest operation, total with bogus application descriptions and back links to download the Android application, from which 17 exceptional APK samples have been received. The spying applications had been downloaded 1,481 situations from July 20, 2020, until eventually June 28, 2021.
888 RAT, initially conceived as a Windows remote access trojan (RAT) costing $80, has considering the fact that created new abilities for the destructive software package to focus on Android and Linux systems at an additional expense of $150 (Pro) and $200 (Intense), respectively.
The industrial RAT runs the common adware gamut in that it really is equipped to run 42 instructions obtained from its command-and-regulate (C&C) server. Some of its well known capabilities involve the means to steal and delete information from a unit, just take screenshots, amass machine place, swipe Fb credentials, get a list of mounted applications, get user photographs, get images, record surrounding audio and phone phone calls, make phone calls, steal SMS messages and get hold of lists, and mail text messages.
In accordance to ESET, India, Ukraine, and the U.K. account for the most bacterial infections around the three-year time period setting up from August 18, 2018, with Romania, The Netherlands, Pakistan, Iraq, Russia, Ethiopia, and Mexico rounding off the major 10 places.
The espionage action has been joined instantly to two other incidents that came to gentle in 2020, counting a general public disclosure from Chinese cybersecurity services organization QiAnXin that thorough a BladeHawk attack with the exact same modus operandi, with overlaps in the use of C&C servers, 888 RAT, and the reliance on Facebook for distributing malware.
Furthermore, the Android 888 RAT has been linked to two far more structured strategies — 1 that involved adware disguised as TikTok and an details-collecting procedure undertaken by the Kasablanca Team.
Identified this write-up attention-grabbing? Follow THN on Fb, Twitter and LinkedIn to read additional special articles we write-up.
Some components of this short article are sourced from:
thehackernews.com


![[ebook] the guide for speeding time to response for lean](https://thecybersecurity.news/data/2021/09/Ebook-The-Guide-for-Speeding-Time-to-Response-for-Lean-80x80.jpg) [Ebook] The Guide for Speeding Time to Response for Lean IT Security Teams
[Ebook] The Guide for Speeding Time to Response for Lean IT Security Teams