Cybersecurity scientists on Monday disclosed a new Android trojan that hijacks users’ qualifications and SMS messages to facilitate fraudulent pursuits in opposition to banking companies in Spain, Germany, Italy, Belgium, and the Netherlands.
Known as “TeaBot” (or Anatsa), the malware is stated to be in its early levels of enhancement, with malicious attacks focusing on money apps commencing in late March 2021, adopted by a rash of infections in the very first week of Could in opposition to Belgium and the Netherlands banking companies. The first indicators of TeaBot exercise transpired in January.


Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
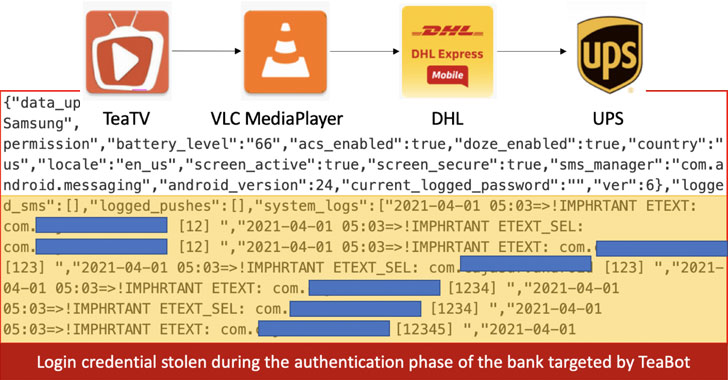
“The key target of TeaBot is stealing victim’s qualifications and SMS messages for enabling frauds eventualities versus a predefined listing of banking companies,” Italian cybersecurity, and online fraud prevention business Cleafy reported in a Monday compose-up. “Once TeaBot is effectively installed in the victim’s gadget, attackers can attain a stay streaming of the machine monitor (on demand from customers) and also interact with it via Accessibility Solutions.”
The rogue Android software, which masquerades as media and bundle delivery expert services like TeaTV, VLC Media Player, DHL, and UPS, functions as a dropper that not only loads a second-phase payload but also forces the target into granting it accessibility support permissions.
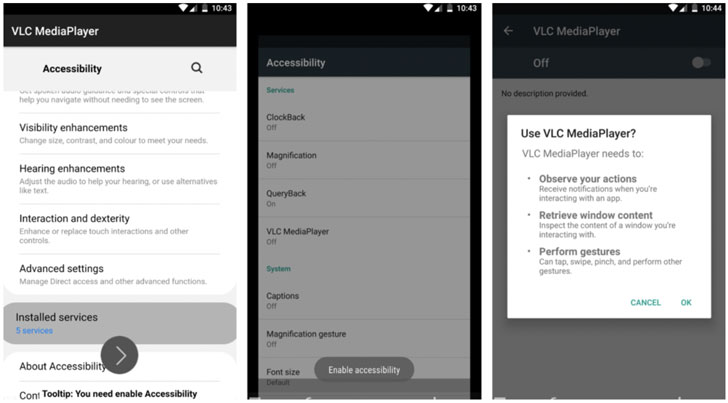
In the last connection of the attack chain, TeaBot exploits the accessibility to realize genuine-time interaction with the compromised product, enabling the adversary to history keystrokes, in addition to using screenshots and injecting malicious overlays on major of login screens of banking applications to steal qualifications and credit card info.
Other abilities of TeaBot include disabling Google Perform Secure, intercepting SMS messages, and accessing Google Authenticator 2FA codes. The gathered facts is then exfiltrated each 10 seconds to a remote server controlled by the attacker.
Android malware abusing accessibility products and services as a stepping stone for perpetrating knowledge theft has witnessed a surge in latest months. Due to the fact the start off of the calendar year, at least three various malware households — Oscorp, BRATA, and FluBot — have banked on the feature to acquire complete command of the contaminated gadgets.
Curiously, the point that TeaBot employs the identical decoy as that of Flubot by posing as innocuous shipment apps could be an try to mislead attribution and continue to be beneath the radar. The heightened FluBot infections prompted Germany and the U.K. to issue alerts last thirty day period warning of ongoing attacks through fraudulent SMS messages that trick customers into putting in “spy ware that steals passwords and other sensitive facts.”
Discovered this posting fascinating? Comply with THN on Facebook, Twitter and LinkedIn to read much more unique written content we put up.
Some components of this report are sourced from:
thehackernews.com

 Japanese Manufacturer Yamabiko Targeted by Babuk Ransomware
Japanese Manufacturer Yamabiko Targeted by Babuk Ransomware