Fb on Wednesday said it took techniques to dismantle destructive things to do perpetrated by two state-sponsored hacking teams functioning out of Palestine that abused its system to distribute malware.
The social media huge attributed the attacks to a network connected to the Preventive Security Company (PSS), the security equipment of the State of Palestine, and an additional danger actor is recognized as Arid Viper (aka Desert Falcon and APT-C-23), the latter of which is alleged to be connected to the cyber arm of Hamas.
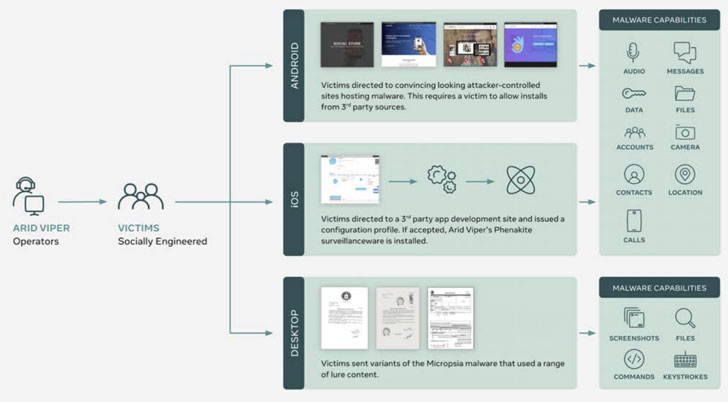
The two digital espionage campaigns, active in 2019 and 2020, exploited a selection of gadgets and platforms, these kinds of as Android, iOS, and Windows, with the PSS cluster principally focusing on domestic audiences in Palestine. The other established of attacks went just after buyers in the Palestinian territories and Syria and, to a lesser extent Turkey, Iraq, Lebanon, and Libya.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code

Both equally the teams appear to have leveraged the platform as a springboard to launch a wide range of social engineering attacks in an try to entice men and women into clicking on destructive hyperlinks and installing malware on their products. To disrupt the adversary operations, Facebook explained it took down their accounts, blocked domains associated with their action, and alerted end users it suspects ended up singled out by these groups to support them protected their accounts.
Android Adware in Benign-On the lookout Chat Apps
PSS is claimed to have applied custom made-designed Android malware that was disguised as safe chat applications to stealthily capture system metadata, seize keystrokes, and upload the facts to Firebase. In addition, the group deployed yet another Android malware identified as SpyNote that came with the means to monitor calls and distant access the compromised telephones.
This team utilized faux and compromised accounts to develop fictitious personas, often posing as younger gals, and also as supporters of Hamas, Fatah, several military groups, journalists, and activists with an aim to create associations with the targets and tutorial them towards phishing pages and other malicious sites.
“This persistent danger actor focused on a huge array of targets, including journalists, individuals opposing the Fatah-led govt, human legal rights activists and armed forces teams like the Syrian opposition and Iraqi armed forces,” Fb researchers main the cyber espionage investigations said.
A Sophisticated Espionage Campaign
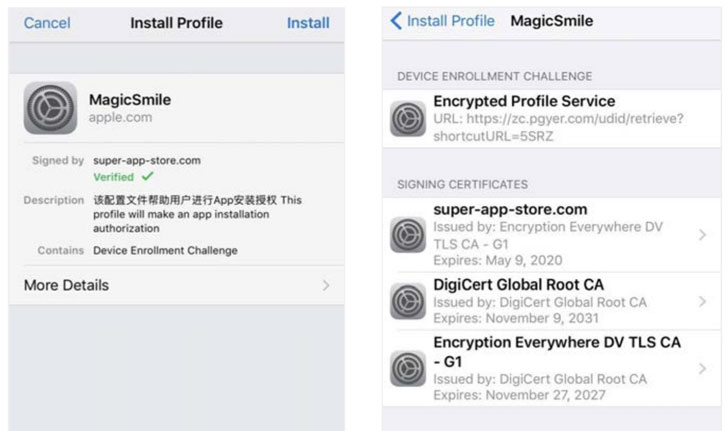
Arid Viper, on the other hand, was observed incorporating a new custom iOS surveillanceware dubbed “Phenakite” in their specific strategies, which Facebook mentioned was able of stealing sensitive user knowledge from iPhones with no jailbreaking the gadgets prior to the compromise. Phenakite was shipped to consumers in the form of a thoroughly useful but trojanized chat software named MagicSmile hosted on a 3rd-party Chinese application growth website that would surreptitiously run in the qualifications and seize facts saved on the phone devoid of the user’s understanding.
The team also managed a large infrastructure comprising 179 domains that had been utilised to host malware or acted as command-and-regulate (C2) servers.

“Entice material and acknowledged victims advise the focus on demographic is individuals related with pro-Fatah teams, Palestinian government businesses, army and security personnel, and pupil teams inside of Palestine,” the researchers included.
Facebook suspects Arid Viper made use of the iOS malware only in a handful of situations, suggesting a extremely-specific procedure, with the Hamas-joined hackers as a substitute focusing on an evolving set of Android-based spy ware applications that claimed to aid courting, networking, and regional banking in the Center East, with the adversary masking the malware as faux application updates for respectable applications like WhatsApp.
At the time set up, the malware urged victims to disable Google Enjoy Guard and give the app gadget admin permissions, employing the permissions to record calls, seize photos, audio, online video, or screenshots, intercept messages, track device spot, retrieve contacts, call logs, and calendar details, and even notification info from messaging applications these kinds of as WhatsApp, Instagram, Imo, Viber, and Skype.
In an attempt to add an further layer of obfuscation, the malware was then identified to call a variety of attacker-controlled web-sites, which in switch delivered the implant with the C2 server for facts exfiltration.
“Arid Viper just lately expanded their offensive toolkit to contain iOS malware that we consider is remaining deployed in specific attacks towards pro-Fatah groups and folks,” Fb researchers stated. “As the technological sophistication of Arid Viper can be deemed to be reduced to medium, this enlargement in capability must sign to defenders that other reduced-tier adversaries may well presently have, or can speedily build, identical tooling.”
Uncovered this write-up appealing? Abide by THN on Fb, Twitter and LinkedIn to read extra special content material we post.
Some elements of this posting are sourced from:
thehackernews.com


 When unicorns trot too fast: Lessons from one startup’s bug bounty missteps
When unicorns trot too fast: Lessons from one startup’s bug bounty missteps