Meta Platforms on Friday disclosed that it experienced discovered above 400 malicious apps on Android and iOS that it stated targeted on the web people with the intention of thieving their Facebook login facts.
“These applications have been detailed on the Google Enjoy Retailer and Apple’s Application Shop and disguised as image editors, online games, VPN products and services, business enterprise apps, and other utilities to trick folks into downloading them,” the social media behemoth stated in a report shared with The Hacker News.


Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
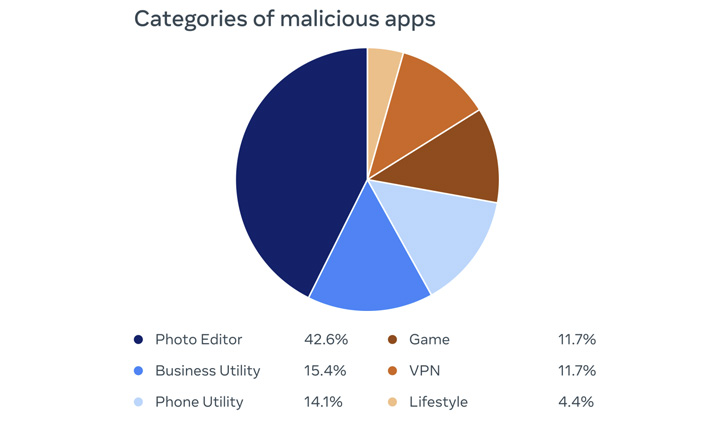
42.6% of the rogue applications were being picture editors, adopted by organization utilities (15.4%), phone utilities (14.1%), online games (11.7%), VPNs (11.7%), and lifestyle applications (4.4%). Interestingly, a majority of the iOS apps posed as adverts supervisor equipment for Meta and its Fb subsidiary.
Aside from concealing its malicious mother nature as a established of seemingly harmless apps, the operators of the plan also posted faux testimonials that have been made to offset the adverse reviews still left by consumers who could have formerly downloaded the applications.
The applications in the long run functioned as a means to steal the qualifications entered by buyers by exhibiting a “Login With Fb” prompt.
“If the login information and facts is stolen, attackers could likely get total entry to a person’s account and do matters like information their close friends or accessibility non-public data,” the organization explained.

All the apps in query have been taken down from each app retailers. The listing of 403 apps (356 Android and 47 iOS applications) can be accessed listed here.
As generally with applications like these, it is really essential to training caution just before downloading applications and granting entry to Facebook to access the promised features. This contains scrutinizing app permissions and opinions, and also verifying the authenticity of the app developers.
The disclosure also comes as Meta-owned WhatsApp filed a lawsuit against a few firms centered in China and Taiwan for allegedly misleading above a million end users into compromising their have accounts by distributing bogus variations of the messaging app.
Discovered this posting intriguing? Follow THN on Fb, Twitter and LinkedIn to study more distinctive content material we write-up.
Some elements of this short article are sourced from:
thehackernews.com

 The essentials of GRC and cybersecurity — How they empower each other
The essentials of GRC and cybersecurity — How they empower each other