Fb has patched a bug in its broadly mounted Messenger application for Android that could have authorized a remote attacker to simply call unsuspecting targets and listen to them in advance of even they picked up the audio get in touch with.
The flaw was discovered and noted to Fb by Natalie Silvanovich of Google’s Undertaking Zero bug-hunting group previous thirty day period on October 6 with a 90-working day deadline, and impacts model 284…16.119 (and in advance of) of Facebook Messenger for Android.
In a nutshell, the vulnerability could have granted an attacker who is logged into the app to concurrently initiate a simply call and mail a specially crafted information to a goal who is signed in to both equally the application as effectively as a different Messenger consumer these as the web browser.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
“It would then bring about a scenario where, whilst the unit is ringing, the caller would start getting audio both right up until the human being getting identified as solutions or the phone periods out,” Facebook’s Security Engineering Manager Dan Gurfinkel said.
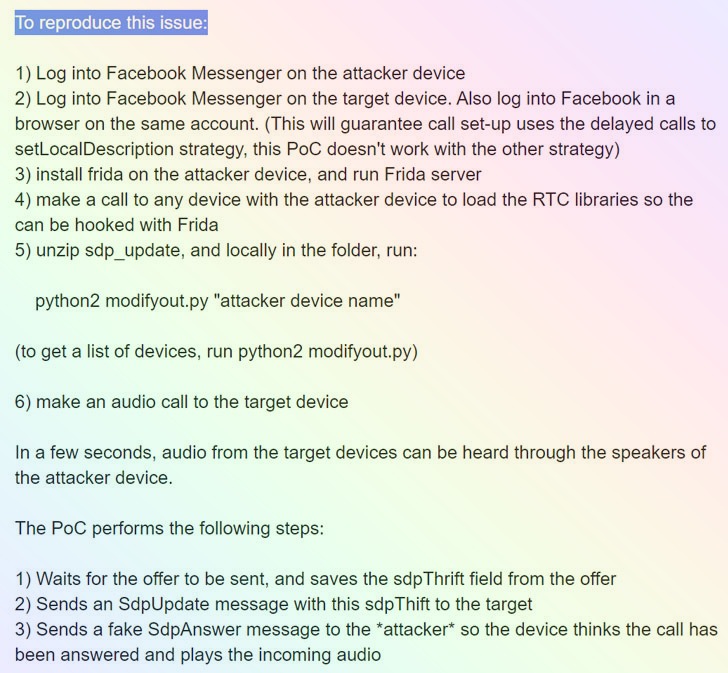
In accordance to a specialized produce-up by Silvanovich, the flaw resides in WebRTC’s Session Description Protocol (SDP) — which defines a standardized structure for the exchange of streaming media among two endpoints — allowing an attacker to send a unique sort of message recognized as “SdpUpdate” that would trigger the call to connect to the callee’s device in advance of staying answered.
Audio and online video calls by means of WebRTC generally does not transmit audio until eventually the recipient has clicked the accept button, but if this “SdpUpdate” message is sent to the other stop machine although it is ringing, “it will induce it to get started transmitting audio straight away, which could allow for an attacker to monitor the callee’s surroundings.”
In some ways, the vulnerability bears similarity to a privacy-eroding flaw that was noted in Apple’s FaceTime group chats characteristic past calendar year that manufactured it attainable for buyers to initiate a FaceTime movie call and eavesdrop on targets by introducing their possess variety as a third man or woman in a team chat even ahead of the person on the other end recognized the incoming simply call.
The gaffe was considered so extreme that Apple pulled the plug on FaceTime group chats completely right before it resolved the issue in a subsequent iOS update.
But in contrast to the FaceTime bug, exploiting the issue isn’t really that effortless. The caller would have to previously have the permissions to call a unique particular person — in other text, the caller and the callee would have to be Facebook close friends to pull this off.
What is much more, the attack also necessitates that the poor actor uses reverse engineering instruments like Frida to manipulate their very own Messenger software to pressure it to ship the custom made “SdpUpdate” message.
Silvanovich was awarded a $60,000 bug bounty for reporting the issue, 1 among the Facebook’s three greatest bug bounties to date, which the Google researcher reported she was donating to a non-financial gain named GiveWell.
This, not the initially time Silvanovich has uncovered critical flaws in messaging apps, who has formerly unearthed a quantity of issues in WhatApp, iMessage, WeChat, Sign, and Reliance JioChat, some of which have located the “callee gadget to ship audio without the need of person interaction.”
Discovered this article intriguing? Adhere to THN on Facebook, Twitter and LinkedIn to read through much more exclusive information we write-up.
Some sections of this report are sourced from:
thehackernews.com


 Before automation can realize promise, companies have ground-level work to do
Before automation can realize promise, companies have ground-level work to do