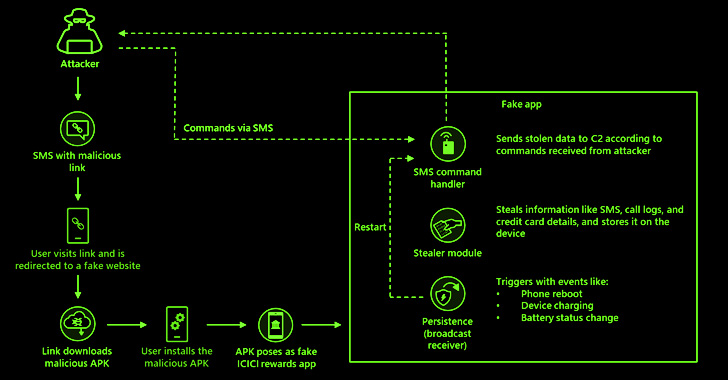
An SMS-based phishing marketing campaign is targeting prospects of Indian banking institutions with info-stealing malware that masquerades as a benefits application.
The Microsoft 365 Defender Study Team mentioned that the messages have inbound links that redirect people to a sketchy internet site that triggers the obtain of the pretend banking benefits app for ICICI Bank.
“The malware’s RAT capabilities allow the attacker to intercept important product notifications these as incoming messages, an apparent effort to catch two-factor authentication (2FA) messages often made use of by banking and economical establishments,” scientists Shivang Desai, Abhishek Pustakala, and Harshita Tripathi said.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code

Also, the malware is equipped with the potential to steal SMSes, probably enabling the attacker to swipe 2FA codes sent as text messages and attain unauthorized entry to victim accounts.
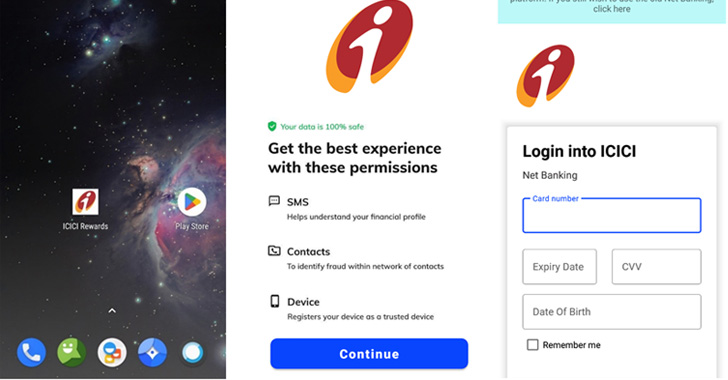
Like other social engineering attacks, familiar brand logos and names are applied in the smishing information as effectively as the rogue application in a bid to give an illusion of legitimacy and trick the end users into putting in the applications.
The attacks are also a continuation of an ongoing marketing campaign that has dispersed comparable rewards-themed applications for other Indian banking institutions these kinds of as the Point out Lender of India (SBI) and Axis Bank in the earlier.
After put in, the fraudulent app not only asks for intensive permissions, but also requests customers to enter their credit score/debit card information as element of a meant indication-in procedure, while the trojan waits for even further directions from the attacker.

These instructions allow for the malware to harvest method metadata, connect with logs, intercept phone calls, as properly as steal credentials for email accounts this sort of as Gmail, Outlook, and Yahoo.
“This malware’s continuing evolution highlights the need to protect mobile equipment,” the scientists stated. “Its broader SMS thieving capabilities could allow attackers to the stolen data to even further steal from a user’s other banking apps.”
Found this short article intriguing? Stick to THN on Facebook, Twitter and LinkedIn to study a lot more special written content we post.
Some pieces of this post are sourced from:
thehackernews.com

 Podcast transcript: Meet the cyborg hacker
Podcast transcript: Meet the cyborg hacker