Shutterstock
The Federal Bureau of Investigation (FBI) confirmed on Saturday that a hacker exploited its programs to mail fake e-mails to regulation enforcement companions alerting them to a intended cyber attack.
The hacker exploited a misconfiguration in its Law Enforcement Company Portal (LEEP) web application to send out genuine-hunting alerts to companions warning them that they had endured a cyber attack and that a risk actor was currently in their method.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
Email messages were despatched to associates from an official FBI email account with an @ic.fbi.gov area, the headers of which also appeared to be legit just after being sanitised.
The hacker falsely knowledgeable recipients they had fallen victim to a “refined chain attack” attributed to Vinny Troia, a respected security researcher and oft issue of memes in the cyber security field.
Troia turned down his involvement in the attack soon right after its discovery.
The FBI confirmed the risk actor was unable to entry or compromise any sensitive data held by the FBI, and claimed the server used to send out the fake emails was utilized only to press notifications for LEEP rather than currently being connected to the FBI’s corporate email service.
“The FBI is knowledgeable of a computer software misconfiguration that quickly allowed an actor to leverage the Legislation Enforcement Business Portal (LEEP) to deliver fake e-mails,” it stated on Saturday. “LEEP is FBI IT infrastructure applied to converse with our state and regional legislation enforcement partners.
“When the illegitimate email originated from an FBI operated server, that server was devoted to pushing notifications for LEEP and was not portion of the FBI’s corporate email service. No actor was equipped to access or compromise any facts or PII on the FBI’s network. After we acquired of the incident, we speedily remediated the computer software vulnerability, warned associates to disregard the fake emails, and confirmed the integrity of our networks.”
Researchers at Spamhaus drew awareness to the early reviews of phony email messages on Saturday, expressing the recipients had been picked indiscriminately and email addresses were being scraped from an ARIN database.
ARIN is a regional internet registry accountable for the management and distribution of internet selection means these types of as internet protocol (IP) addresses and autonomous process numbers (ASNs).
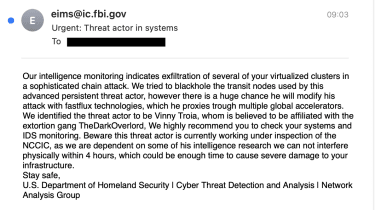
The email sent to recipients appeared as follows:
Spamhaus
Spamhaus mentioned its telemetry indicated two ‘waves’ of spam emails staying sent, one just in advance of 05:00 on Saturday and then a different shortly right after 07:00.
Security researchers claimed having contacted the FBI at the time of the incident stated the team ended up “slammed” with calls from alarmed recipients trying to validate if the correspondence was genuine or not.
A hacker regarded by the alias Pompompurin claimed duty for the attack in an job interview with security researcher Brian Krebs. They explained they desired to draw interest to the security vulnerability in the LEEP web app.
Pompompurin said LEEP allowed any one to use for an account, despite it remaining reserved only for regulation enforcement partners of the FBI. Account authentication was also operate by a a single-time passcode emailed to the applicant – a code which the FBI’s internet site leaked in the HTML code of its web page.
When people requested a confirmation code, they ended up despatched a Post request which involved parameters for the email subject matter and overall body written content. Pompompuring changed the parameters withi his own email issue and body to automate hundreds of email sends.
Some parts of this article are sourced from:
www.itpro.co.uk


 North Korean Hackers Target Cybersecurity Researchers with Trojanized IDA Pro
North Korean Hackers Target Cybersecurity Researchers with Trojanized IDA Pro