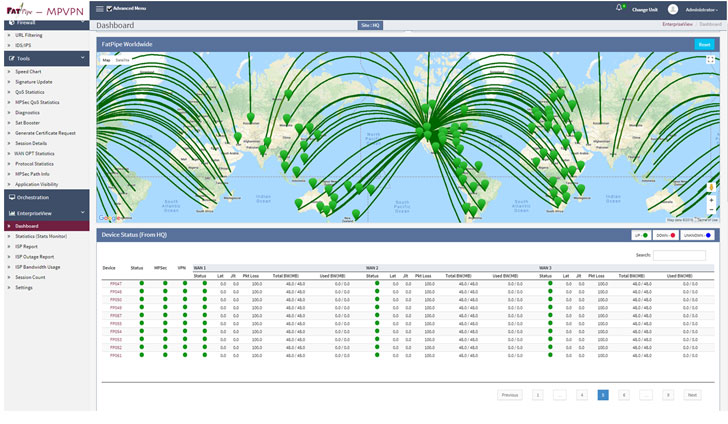
The U.S. Federal Bureau of Investigation (FBI) has disclosed that an unknown risk actor has been exploiting a previously unidentified weak point in the FatPipe MPVPN networking units at minimum since May perhaps 2021 to acquire an preliminary foothold and preserve persistent obtain into vulnerable networks, making it the most current firm to join the likes of Cisco, Fortinet, Citrix, Pulse Safe that have experienced their methods exploited in the wild.
“The vulnerability permitted APT actors to obtain obtain to an unrestricted file add purpose to drop a web shell for exploitation action with root access, primary to elevated privileges and possible follow-on exercise,” the agency said in an notify released this 7 days. “Exploitation of this vulnerability then served as a jumping off position into other infrastructure for the APT actors.”


Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
In other words and phrases, the zero-day vulnerability enables a remote attacker to add a file to any spot on the filesystem on an affected system. The security flaw impacts the web administration interface of FatPipe WARP, MPVPN, and IPVPN router clustering and VPN load-balancing gadgets jogging software package prior to the most recent model releases 10.1.2r60p93 and 10.2.2r44p1.
The FBI, in its flash warn, pointed out that the threat actor leveraged the web shell to shift laterally and strike more U.S. infrastructure by location up a destructive SSH support, subsequent it up with a range of actions designed to hide the intrusions and protect their exploit right up until it can be required again.

In an impartial bulletin (FPSA006), FatPipe reported that the bug stems from a absence of input validation system for precise HTTP requests, therefore enabling an attacker to exploit the issue by sending a specially crafted HTTP ask for to the influenced unit. Though there are no workarounds that handle the flaw, the enterprise mentioned it can be mitigated by disabling UI and SSH access on the WAN interface or configuring Access Lists to allow accessibility only from reliable sources.
Uncovered this posting exciting? Stick to THN on Fb, Twitter and LinkedIn to read a lot more distinctive content material we write-up.
Some parts of this write-up are sourced from:
thehackernews.com

 A Simple 5-Step Framework to Minimize the Risk of a Data Breach
A Simple 5-Step Framework to Minimize the Risk of a Data Breach