Amid renewed tensions in between the U.S. and Russia around Ukraine and Kazakhstan, American cybersecurity and intelligence agencies on Tuesday launched a joint advisory on how to detect, reply to, and mitigate cyberattacks orchestrated by Russian condition-sponsored actors.
To that close, the Cybersecurity and Infrastructure Security Agency (CISA), Federal Bureau of Investigation (FBI), and Nationwide Security Agency (NSA) have laid bare the tactics, tactics, and strategies (TTPs) adopted by the adversaries, such as spear-phishing, brute-pressure, and exploiting recognised vulnerabilities to attain first accessibility to concentrate on networks.


Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
The checklist of flaws exploited by Russian hacking teams to achieve an preliminary foothold, which the companies reported are “prevalent but helpful,” are below —
- CVE-2018-13379 (FortiGate VPNs)
- CVE-2019-1653 (Cisco router)
- CVE-2019-2725 (Oracle WebLogic Server)
- CVE-2019-7609 (Kibana)
- CVE-2019-9670 (Zimbra application)
- CVE-2019-10149 (Exim Straightforward Mail Transfer Protocol)
- CVE-2019-11510 (Pulse Secure)
- CVE-2019-19781 (Citrix)
- CVE-2020-0688 (Microsoft Trade)
- CVE-2020-4006 (VMWare)
- CVE-2020-5902 (F5 Huge-IP)
- CVE-2020-14882 (Oracle WebLogic)
- CVE-2021-26855 (Microsoft Exchange, exploited regularly along with CVE-2021-26857, CVE-2021-26858, and CVE-2021-27065)
“Russian condition-sponsored APT actors have also demonstrated subtle tradecraft and cyber abilities by compromising 3rd-party infrastructure, compromising 3rd-party computer software, or developing and deploying customized malware,” the companies explained.
“The actors have also demonstrated the capacity to maintain persistent, undetected, lengthy-phrase entry in compromised environments — which include cloud environments — by using reputable credentials.”
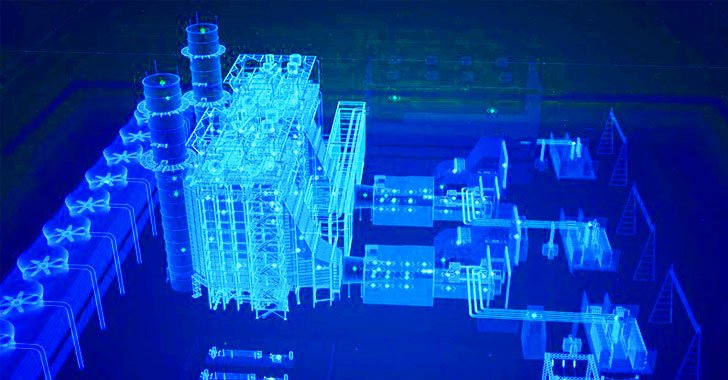
Russian APT groups have been historically observed placing their sights on operational technology (OT) and industrial management units (ICS) with the goal of deploying damaging malware, main among them getting the intrusion campaigns towards Ukraine and the U.S. strength sector as well as attacks exploiting trojanized SolarWinds Orion updates to breach the networks of U.S. government organizations.
To boost cyber resilience in opposition to this danger, the businesses advocate mandating multi-factor authentication for all buyers, searching out for indicators of irregular activity implying lateral motion, implementing network segmentation, and keeping working techniques, applications, and firmware up to date.
“Take into account working with a centralized patch management process,” the advisory reads. “For OT networks, use a risk-centered assessment technique to figure out the OT network property and zones that ought to participate in the patch administration method.”
Other mitigation methods involve —
- Employ sturdy log assortment and retention
- Involve accounts to have potent passwords
- Allow powerful spam filters to protect against phishing email messages from reaching stop-consumers
- Put into action rigorous configuration administration systems
- Disable all avoidable ports and protocols
- Guarantee OT components is in examine-only mode
Discovered this post intriguing? Stick to THN on Facebook, Twitter and LinkedIn to browse much more unique articles we submit.
Some areas of this post are sourced from:
thehackernews.com


 First Patch Tuesday of 2022 Brings Fix for a Critical ‘Wormable’ Windows Vulnerability
First Patch Tuesday of 2022 Brings Fix for a Critical ‘Wormable’ Windows Vulnerability