The U.S. Department of Justice (DoJ) introduced that it neutralized Cyclops Blink, a modular botnet controlled by a danger actor known as Sandworm, which has been attributed to the Key Intelligence Directorate of the General Staff members of the Armed Forces of the Russian Federation (GRU).
“The procedure copied and removed malware from vulnerable internet-linked firewall gadgets that Sandworm applied for command-and-manage (C2) of the underlying botnet,” the DoJ reported in a statement Wednesday.
In addition to disrupting its C2 infrastructure, the procedure also shut the external management ports that the menace actor employed to build connections with the firewall appliances, proficiently severing the connections and blocking the hacking team from making use of the infected units to commandeer the botnet.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
The March 22 court docket-licensed disruption of Cyclops Blink comes a very little about a thirty day period immediately after intelligence companies in the U.K. and the U.S. explained the botnet as a replacement framework for the VPNFilter malware that was exposed and sinkholed in May possibly 2018.
Cyclops Blink, which is thought to have emerged as early as June 2019, mostly qualified WatchGuard firewall appliances and ASUS routers, with the Sandworm team leveraging a earlier discovered security vulnerability in WatchGuard’s Firebox firmware as an first entry vector.
A comply with-up investigation by cybersecurity business Craze Micro last month recommended the likelihood that the botnet is an attempt to “create an infrastructure for further attacks on significant-price targets.”
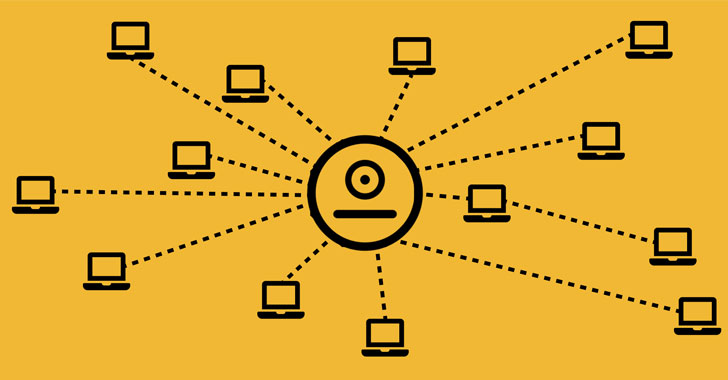
“These network equipment are frequently positioned on the perimeter of a victim’s computer network, therefore delivering Sandworm with the possible means to perform malicious things to do against all computer systems inside of all those networks,” the DoJ extra.
Facts of the security flaw ended up under no circumstances manufactured public beyond the point that the organization resolved the issue as element of program updates issued in Might 2021, with WatchGuard noting to the opposite that the issues have been internally detected and that they have been not “actively identified in the wild.”
The company has since revised its Cyclops Blink FAQs to spell out that the vulnerability in problem is CVE-2022-23176 (CVSS rating: 8.8), which could “allow an unprivileged user with accessibility to Firebox administration to authenticate to the procedure as an administrator” and obtain unauthorized remote obtain.
ASUS, for its aspect, has launched firmware patches as of April 1, 2022, to block the risk, recommending consumers to update to the hottest variation.
Found this report fascinating? Abide by THN on Fb, Twitter and LinkedIn to read far more exclusive written content we put up.
Some parts of this report are sourced from:
thehackernews.com


 Should your business worry about Russian cyber attacks?
Should your business worry about Russian cyber attacks?