A new wave of spear-phishing campaigns leveraged weaponized Windows 11 Alpha-themed Word files with Visual Essential macros to drop destructive payloads, together with a JavaScript implant, versus a issue-of-sale (PoS) service service provider positioned in the U.S.
The attacks, which are considered to have taken location involving late June to late July 2021, have been attributed with “moderate self-confidence” to a financially inspired threat actor dubbed FIN7, according to researchers from cybersecurity business Anomali.
“The specified targeting of the Clearmind domain matches very well with FIN7’s most popular modus operandi,” Anomali Threat Research explained in a technical analysis revealed on September 2. “The group’s purpose seems to have been to deliver a variation of a JavaScript backdoor applied by FIN7 since at minimum 2018.”

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
An Jap European team lively due to the fact at the very least mid-2015, FIN7 has a checkered record of targeting cafe, gambling, and hospitality industries in the U.S. to plunder financial details these types of as credit rating and debit card numbers that were then applied or bought for financial gain on underground marketplaces.

Even though a number of users of the collective have been imprisoned for their roles in various strategies considering the fact that the start off of the yr, FIN7’s routines have also been tied to a further team named Carbanak, given its identical TTPs, with the key difference currently being that whilst FIN7 focuses on hospitality and retail sectors, Carbanak has singled out banking institutions.
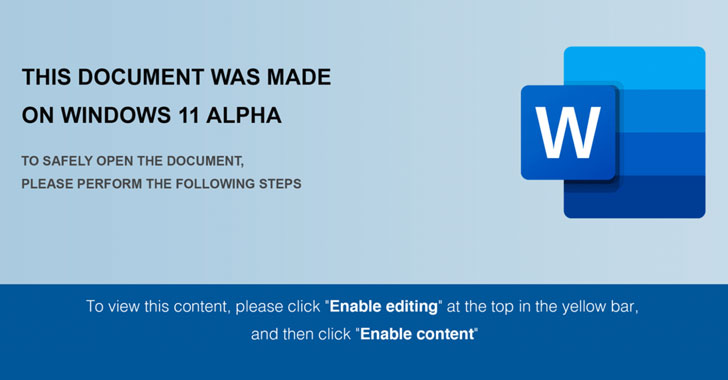
In the newest attack observed by Anomali, the an infection commences with a Microsoft Term maldoc containing a decoy graphic that is purported to have been “produced on Windows 11 Alpha,” urging the receiver to help macros to cause the future phase of action, which includes executing a greatly-obfuscated VBA macro to retrieve a JavaScript payload, which has been identified to share similar features with other backdoors made use of by FIN7.
In addition to having a number of actions to try out to impede assessment by populating the code with junk knowledge, the VB script also checks if it is managing underneath a virtualized natural environment such as VirtualBox and VMWare, and if so, terminates itself, in addition to stopping the an infection chain upon detecting Russian, Ukrainian, or quite a few other Japanese European languages.
The backdoor’s attribution to FIN7 stems from overlaps in the victimology and methods adopted by the risk actor, together with the use of a JavaScript-dependent payload to plunder important information.
“FIN7 is a single of the most notorious fiscally enthusiastic groups because of to the substantial amounts of delicate facts they have stolen as a result of various strategies and attack surfaces,” the researchers reported. “Items have been turbulent for the risk team in excess of the previous few decades as with results and notoriety will come the ever-watchful eye of the authorities. In spite of large-profile arrests and sentencing, which include alleged higher-rating customers, the team carries on to be as lively as at any time.”
Found this report intriguing? Stick to THN on Fb, Twitter and LinkedIn to browse extra exclusive information we submit.
Some parts of this posting are sourced from:
thehackernews.com

 FBI Warns Food and Agriculture Firms of Ransomware Threat
FBI Warns Food and Agriculture Firms of Ransomware Threat