Risk actors regarded for trying to keep a reduced profile do so by ceasing operations for prolonged periods in amongst to evade attracting any consideration as very well as continuously refining their toolsets to fly under the radar of numerous detection technologies.
1 these types of team is FIN8, a financially inspired danger actor which is again in action right after a yr-and-a-fifty percent hiatus with a effective model of a backdoor with upgraded capabilities together with monitor capturing, proxy tunneling, credential theft, and fileless execution.
1st documented in 2016 by FireEye, FIN8 is recognised for its attacks against the retail, hospitality, and enjoyment industries though producing use of a wide array of tactics these as spear-phishing and destructive equipment like PUNCHTRACK and BADHATCH to steal payment card details from issue-of-sale (POS) units.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
“The FIN8 team is identified for taking prolonged breaks to improve TTPs and improve their rate of accomplishment,” Bitdefender researchers explained in a report released today. “The BADHATCH malware is a experienced, really superior backdoor that works by using several evasion and defense strategies. The new backdoor also tries to evade security monitoring by applying TLS encryption to conceal Powershell instructions.”
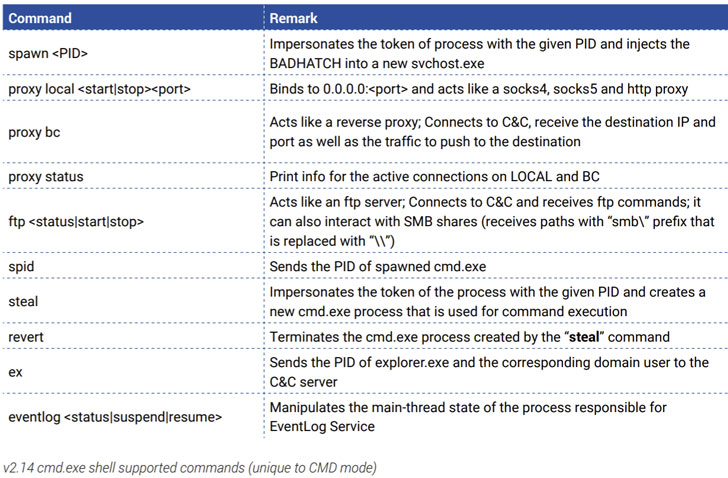
BADHATCH, given that its discovery in 2019, has been deployed as an implant capable of working attacker-supplied commands retrieved from a distant server, in addition to injecting destructive DLLs in a current process, gathering program details, and exfiltrating facts to the server.
Noting that at least three various variants of the backdoor (v2.12 to 2.14) have been noticed considering the fact that April 2020, the researchers stated the most recent version of BADHATCH abuses a respectable services named sslp.io to thwart detection all through the deployment approach, making use of it to down load a PowerShell script, which in convert executes the shellcode made up of the BADHATCH DLL.
The PowerShell script, other than using obligation for accomplishing persistence, also requires treatment of privilege escalation to guarantee that all commands post the script’s execution are run as the System user.
Also, a 2nd evasion strategy adopted by FIN8 includes passing off communications with the command-and-handle (C2) server that masquerade as respectable HTTP requests.
According to Bitdefender, the new wave of attacks is reported to have taken place around the earlier calendar year and directed from insurance policy, retail, technology, and chemical industries in the U.S., Canada, South Africa, Puerto Rico, Panama, and Italy.
“Like most persistent and experienced cyber-crime actors, FIN8 operators are regularly refining their applications and techniques to stay clear of detection,” the researchers concluded, urging organizations to “separate the POS network from the ones made use of by workers or company” and filter out emails made up of malicious or suspicious attachments.
Identified this write-up appealing? Comply with THN on Fb, Twitter and LinkedIn to go through much more exclusive content material we write-up.
Some components of this write-up are sourced from:
thehackernews.com


 The future of CIAM
The future of CIAM