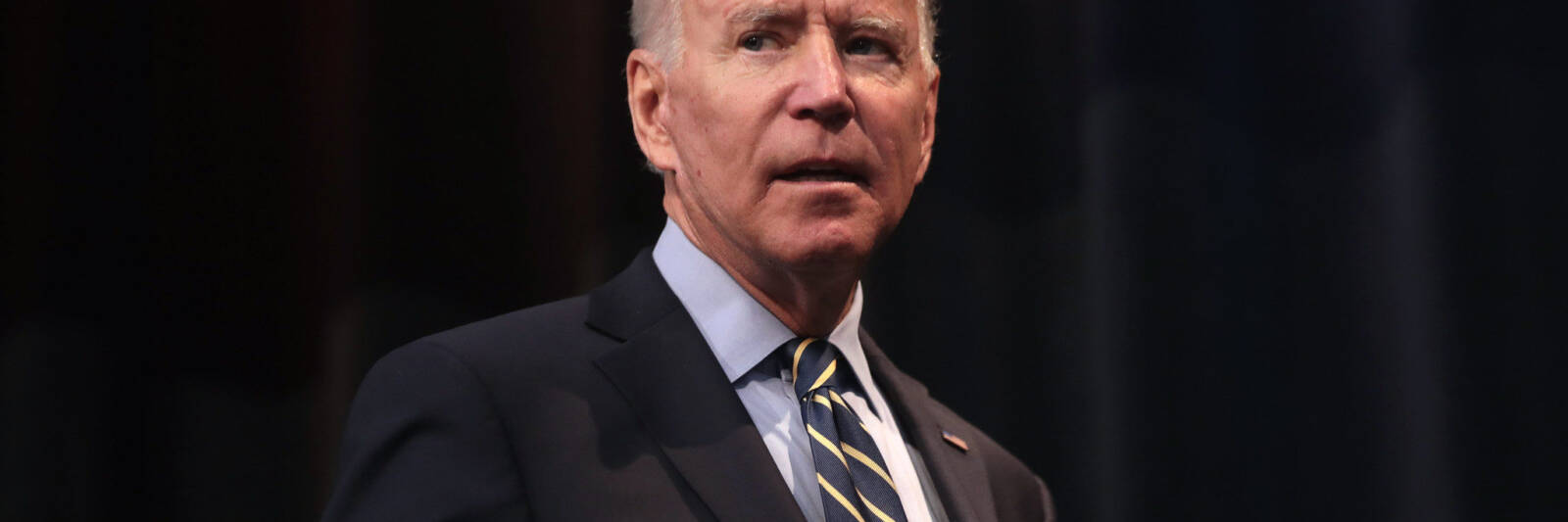
Alleged leaks connecting Democratic presidential prospect Joe Biden to his son’s dealings in Ukraine right away elevated alarm bells to forensic analysts. The race to establish what is serious and what is doctored mirrors issues faced by security teams needing to validate business files.
Specially, just one of the most explosive email messages unveiled by the New York Submit was posted in these types of a way to disguise Domain Keys Recognized Mail information and facts, or DKIM, which is made use of to detect solid sender addresses. It also exhibited metadata that named into problem regardless of whether the email supplied to the Article was the authentic file. Regardless of whether the email is legit or not is continue to below discussion.
The circumstance points to a popular obstacle for political strategies and firms alike: Validating with any certainty that a distinct file is phony or manipulated is challenging, and necessitates a mix of forensic tactics that most chief info security officers struggle to put into practice networkwide.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
“You’re seeking to verify a negative,” claimed Mike Weber, vice president of innovation at Coalfire. “It’s tough to demonstrate knowledge was never ever on your network.”
Just like political strategies, organizations throughout a variety of sectors have suffered knowledge leaks that resulted in the launch of usually sensitive email messages and documents – from defense and aerospace contractors to money institutions and film studios. Ensuring none of the information were being falsified elements into these situations, but networkwide devices made for non-repudiation are not especially suited for broad enterprise operations. A Department of Defense-type PKE network is expensive and cumbersome, Weber reported, and not likely to “span all industries and all measurement businesses.”
Even in diligently designed units, hackers could use obtain to a network to plant a document to meet up with the non-repudiation checks, cryptographic keys may drop out of a company’s manage, and hackers could assert harmful leaked documents came from a vendor exterior the PKE technique.
And which is all assuming the most high-priced, greatest carried out program of signatures and back-ups and evidence making is in place. Most companies, he reported, are nowhere close to that point.
“Even in businesses we operate for, some massive types with mergers and acquisitions that would blow your brain, communications are not handled with integrity and security,” he stated. “Ease of use is a really hard thing to battle.”
Developing a forensic path for email is a a bit distinctive tale. In the situation of the alleged Biden leak, the New York Write-up did not make it achievable for scientists to look at DKIM on the e-mails. But that solution is indeed one tactic to authenticate whether or not an email was genuinely despatched from a server. WikiLeaks relied on DKIM to validate e-mail in the 2016 leaks of emails from the Democratic Countrywide Committee – a leak that also bundled a number falsified paperwork.
Certainly, DKIM is not best. There are a couple of tricks to create a false DKIM match, furthermore e-mail that go by way of many arms can produce untrue negatives (a little something a new protocol named ARC is designed to combat). And, said Seth Blank, vice president of Standards and New Technology at Valimail, it would ideally be paired with DMARC, a conventional to make positive the email handle in the “from” line is not remaining spoofed.
A validated signature can be faked, Blank extra, “but the bar to do that is a good deal increased.”
A further problem, however, is that non-repudiation attributes of DKIM were developed to be used in the moment a email was despatched, not weeks or months afterwards when a leak would in principle would consider put. A company could cycle by cryptographic keys, leaving aged email messages unverifiable.
Nevertheless, Blank claimed, is that DKIM is a somewhat uncomplicated add to email security that could potentially eradicate some bad actors.
“Without it, email is a ideal impersonation approach, because, when it was designed, no one envisioned it getting made use of for state secrets or enterprise,” he said.
Some parts of this posting are sourced from:
www.scmagazine.com

 Senator Questions US Healthcare Giant Over Cyber-Attack
Senator Questions US Healthcare Giant Over Cyber-Attack