A common misunderstanding among startup founders is that cybercriminals will never waste time on them, because they are not large or effectively recognized enough nonetheless.
But just simply because you are compact will not necessarily mean you are not in the firing line. The measurement of a startup does not exempt it from cyber-attacks – which is simply because hackers constantly scan the internet seeking for flaws that they can exploit a person slip up, and your small business can become entrance-web page news, for the completely wrong motives.
Thankfully, customers are also starting to be significantly conscious of the great importance of cybersecurity and are typically asking startups about the procedures they use to secure their info – meaning cybersecurity is now turning into an crucial enterprise enabler.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
So if you are a CTO considering about ramping up your web or cell apps’ cybersecurity posture, then you are currently on the ideal track, but with so quite a few possibilities, exactly where ought to you begin?
To enable you get going, we produced this information that addresses the subsequent critical points:
- Answering the question, “What is security screening?”
- Knowing the motives to execute security testing
- Defining the scope of cybersecurity testing
- Figuring out when to perform penetration testing
What Is Security Screening?
Security tests is a broad time period that refers to the method of checking a method, network, or piece of program for vulnerabilities that hackers and other risk actors can choose edge of. It can arrive in many varieties, so in this article, we will explore two of its main parts:
Penetration screening is a terrific way to locate the most total of weaknesses doable at a certain place in time, but you should contemplate how speedily you get alerted to new vulnerabilities right after the pen testers have long gone household (idea: not immediately plenty of, you may want a vulnerability scanner for that).
Vulnerability scanners also empower companies to master much more about their security status in advance of committing to far more in-depth and normally more highly-priced handbook assessments. This is a no-brainer in lots of circumstances, as penetration testers will typically start out their exams by operating the similar automated instruments. And you wouldn’t want to make it way too quick for them, would you! )
Why Carry out Security Testing?
Veracode’s State of Software package Security Report unveiled that 83% of the study sample, comprising 85,000 program apps used by 2,300 providers throughout the world, experienced at the very least just one security vulnerability learned throughout an initial security examination. Without the need of the check, these flaws would have been introduced into creation, producing the software program susceptible to cyber attacks.
If, for this cause, you have resolved to commence security tests only to uncover your weaknesses right before the hackers do, then terrific. You’ve got received the flexibility to make your mind up your individual requirements skip ahead to the up coming portion. Normally, other widespread motives to conduct security testing are:
- Third-party or purchaser requests. If companions or prospects have specifically asked for that you accomplish security tests to guarantee that their purchaser facts continues to be secure from cyber attackers – you may possibly have additional stringent necessities. Nevertheless, there can continue to be area for interpretation. It truly is pretty widespread that prospects will have to have a “penetration check,” – but they not often specify what that suggests precisely.
- Compliance certifications and industry polices. Several sector polices or compliance certifications also have to have organizations to bear frequent security screening. Typical examples include ISO 27001, PCI DSS, and SOC2. These expectations specify the tests demanded in several stages of depth, but even the most distinct will not specify just how or what to test, as it is dependent on the situation at hand. For this explanation, it truly is typically accepted that the enterprise being tested is finest positioned to establish what degree of security tests will make sense in their circumstance. So you may well uncover the steerage below is nonetheless practical in deciding what and how to take a look at.
 Your shopper or auditor will constantly have the very last phone, but you know your company very best, so by proposing a sensible testing approach, typically both of those sides can come across an agreement.
Your shopper or auditor will constantly have the very last phone, but you know your company very best, so by proposing a sensible testing approach, typically both of those sides can come across an agreement.
Consider about Tactic prior to Person Security Checks
Risk Assessment: How a lot of a concentrate on are you?
Just about every enterprise is special, and for that cause, your risk will be exceptional to you. Having said that, it can be really hard to know what is the proper amount of testing. You can use the pursuing as a rough manual to what we see in the sector:
1. If you really don’t store significantly sensitive knowledge
For example, you could present a web page uptime checking instrument and don’t retail store specially delicate facts. Until finally you grow significant plenty of to be specific especially, you most likely only want to be concerned about indiscriminate hacks by those people hunting for easy pickings. If so, you happen to be more probable only to need automatic vulnerability scans.
Concentrating on any internet-exposed (or potentially exposed) devices like any distant access (VPNs, remote admin logins), firewalls, internet sites or programs, APIs, as effectively as units that could discover them selves online by accident (nearly anything inside a cloud platform can much too conveniently be set on the internet by accident).
2. If you retail store client information
Maybe you happen to be a advertising and marketing details examination platform, so you might facial area fewer threats from insiders and prison gangs, but you certainly have to have to fret about customers accessing every single other’s data or a standard facts breach. Or, for illustration, you have an application, but anyone can sign up for an account on the internet, you will want to look at an “authenticated” penetration exam from the point of view of a typical consumer – but perhaps not from the viewpoint of an personnel with restricted back-close obtain. You’ll also want to make guaranteed employee laptops are fully patched with the latest security updates.
3. If you happen to be providing a economic assistance
If you are aFinTech startup shifting funds all around, you will will need to get worried about destructive clients and even destructive employees – as very well as cybercriminal gangs focusing on you.
If so, you will want to look at constant vulnerability evaluation and frequent full guide penetration checks from all these scenarios on top rated.
4. If you really don’t have anything at all exposed to the internet
Probably you you should not have nearly anything uncovered to the internet at all or will not create shopper-facing apps – so your major attack floor is employee laptops and cloud solutions. In this situation, automatic vulnerability scanning of your have laptops would make the most sense, and you could take into consideration a far more aggressive type of penetration testing “recognised as red teaming” if you will need further assurance.
 Every single company is unique, and there is no one cybersecurity system that will perform for every single startup. This is why you will need to start out with an comprehension of in which your very own threats reside.
Every single company is unique, and there is no one cybersecurity system that will perform for every single startup. This is why you will need to start out with an comprehension of in which your very own threats reside.
What do you require to safeguard?
Preferably, prior to organizing the security screening alone, you should contemplate what assets you have, both technological and informational, a course of action regarded as “asset administration.”
A incredibly basic instance could be: “We have 70 worker laptops, use mainly cloud companies, and have our customer details saved and backed up in Google Cloud System, and an app that permits both of those admin and consumer access.
Our most vital data is the facts we retail store on behalf of shoppers, and our staff details in our HR methods.”. Contemplating this through then allows you start to type the basis for scoping a test. For example:
- Our HR system is a cloud assistance, so we simply just inquire them for their proof of security testing (and so will not need to have to check them ourselves).
- What IP addresses do we have in Google Cloud, what domains are registered (there are resources that can enable with this).
- Our engineers don’t down load the output database, but do have accessibility to our cloud units, so their laptops and cloud & email accounts are also component of our attack surface.
 Executing asset administration will assistance you keep track of systems belonging to your organization as very well as figure out which IP addresses and domain names require to be examined.
Executing asset administration will assistance you keep track of systems belonging to your organization as very well as figure out which IP addresses and domain names require to be examined.
How Often Must a Startup Perform Security Screening?
It depends on the type of exam! Clearly, the profit of automatic tests is they can be operate as consistently as you want. Although penetration checks are much more high priced to operate often.
Carrying out plan vulnerability scanning at the very least when a thirty day period can assist reinforce your IT infrastructure and is suggested by the Countrywide Cyber Security Centre (NCSC). This observe helps businesses maintain an eye on the in no way ending checklist of new threats over 10,000 new vulnerabilities are documented every yr. Apart from frequent vulnerability scanning, it is also sensible to operate scans just about every time program alterations are produced.
Styles of Vulnerability Scanner
You can select from a number of kinds of vulnerability scanners— network-centered, agent-based, web application, and infrastructure. The alternative relies upon on what assets you aim to secure.
Some typical illustrations of network scanners are Nessus and Qualys. Both are marketplace leaders and give a robust stage of security and vulnerability protection. A fashionable option that you could look at if you want a instrument that is uncomplicated to get commenced with is Intruder.
This on the web vulnerability scanner has been specifically produced to be usable by non-security specialists, though furnishing superior-high-quality checks, as properly as automatic scans for rising threats.
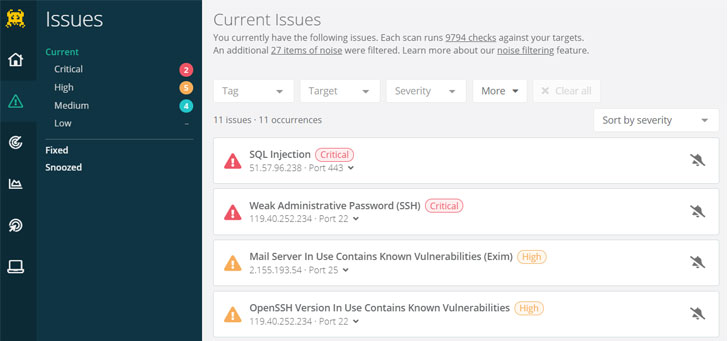 Intruder employs a distinctive algorithm to prioritize issues that go away your devices exposed, producing it especially quick to uncover out what offers the greatest risk.
Intruder employs a distinctive algorithm to prioritize issues that go away your devices exposed, producing it especially quick to uncover out what offers the greatest risk.
What are the Positive aspects of Vulnerability Assessment?
Vulnerability assessment aims to mechanically uncover as a lot of security flaws as doable so these can be mitigated right before menace actors can get to them. It also allows make penetration screening, which, in distinction, is a manual system, far more effective. In truth, as stated by the NCSC, “By using care of the ‘low hanging fruit’ by normal vulnerability scanning, penetration testing engagements can a lot more proficiently aim on intricate security issues that are better suited to a human.”
When to operate a penetration check?
Pen testers mimic serious-everyday living cyber attackers, but compared with menace actors, they comply with a predefined scope and do not abuse the organization’s assets and data. As opposed to vulnerability scanning, they are a great deal far more probably to uncover complicated or significant-influence enterprise-layer weaknesses, these as manipulating product pricing, utilizing a consumer account to obtain a different customer’s knowledge, or pivoting from a person first weak point into comprehensive technique command. The downside is that in comparison, it can be expensive, so when is the proper time to run one particular?
Consider alongside the essential timelines of the risk assessment earlier mentioned, for case in point, immediately after your merchandise is developed but prior to you get started using on true shopper knowledge. Or soon after you maintain some non-delicate consumer info, but ahead of you commence holding salary or well being-associated information and facts.
When you’re up and operating, penetration screening really should be performed following significant adjustments, this sort of as altering your authentication technique, releasing a significant new element or following 6-12 months of modest variations (as each individual a person, in theory, could unintentionally introduce a weakness).
Again this depends on your risk amount if you happen to be relocating dollars about even as typically as every 3 months would be highly recommended (or a lot more!), but if you happen to be on the lower stop of the risk spectrum, at the time just about every 12 months is a generally acknowledged routine.
 Penetration screening ought to be carried out before applying major procedure variations or in regular intervals of 6-12 months.
Penetration screening ought to be carried out before applying major procedure variations or in regular intervals of 6-12 months.
Numerous forms of penetration screening exist. Penetration testing can seem for security flaws in technology, such as in your external and internal networks as effectively as web programs. On the other hand, it can also come across vulnerabilities in an organization’s human resources, these kinds of as in the case of social engineering.
The pen testing business you select would rely on the type of property you want to check, but other factors, these types of as certifications, price, and practical experience, should be regarded as effectively.
Conclusion
Security tests is a critical cybersecurity system that aims to detect vulnerabilities in units, computer software, networks, and apps. Its most typical sorts are vulnerability evaluation and penetration tests, but the aim is generally to tackle security flaws right before malicious actors can exploit them.
Preserve in brain that menace actors also conduct regimen security tests to glance for any vulnerability they can abuse. One particular security flaw could be ample for them to start large-scale cyber attacks. While this could be horrifying, your firm can remain far better guarded by undertaking cybersecurity exams often.
Utilizing this method can be hard, as there is no 1-size-fits-all security tests answer. Smaller companies may possibly also wait to invest in an intangible product or service, in particular 1 they could not thoroughly recognize mainly because of all the complex jargon. Today, numerous instruments offer free trials, which existing a fantastic prospect for compact companies to locate the correct solution before committing to a bigger financial investment.
If you are in want of a modern, effortless-to-use security testing resolution, Intruder presents a 30-day absolutely free trial of their vulnerability assessment platform. Stop by their web-site now to acquire it for a spin!
Identified this posting fascinating? Follow THN on Facebook, Twitter and LinkedIn to browse additional unique information we publish.
Some parts of this short article are sourced from:
thehackernews.com


 Ransomware Defense: Top 5 Things to Do Right Now
Ransomware Defense: Top 5 Things to Do Right Now