Google on Thursday claimed it is really rolling new security attributes to Chrome browser aimed at detecting suspicious downloads and extensions through its Enhanced Protected Searching characteristic, which it released a 12 months back.
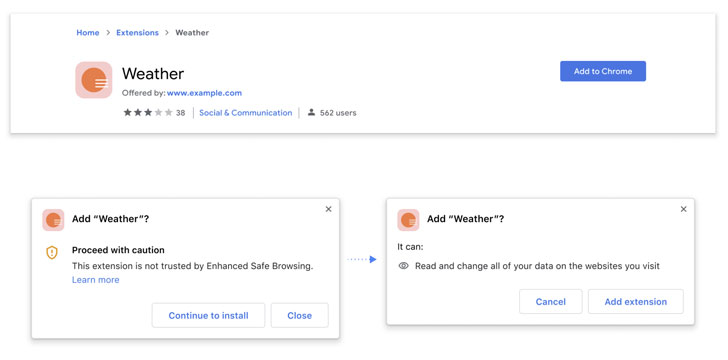
To this finish, the look for big mentioned it will now present extra protections when end users try to install a new extension from the Chrome Web Keep, notifying if it can be thought of “reliable.”
Currently, 75% of all add-ons on the system are compliant, the corporation pointed out, adding “any extensions constructed by a developer who follows the Chrome Web Retail outlet Developer Application Insurance policies, will be thought of trusted by Increased Harmless Browsing.”

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount

Increased Safe Searching involves sharing genuine-time facts with Google Safe and sound Browsing to proactively safeguard end users versus harmful websites. The firm also noted that its integration with Safe Browsing’s blocklist API served boost privacy and security, with the number of malicious extensions disabled by the browser jumping by 81%.
Also coming to Chrome is a new download safety feature that scans downloaded information for malware by applying metadata about the downloaded file, along with offering people the possibility to mail the file to be scanned for a a lot more in depth analysis.
“If you pick to deliver the file, Chrome will add it to Google Protected Browsing, which will scan it employing its static and dynamic assessment classifiers in actual time,” Google mentioned. “After a brief wait around, if Risk-free Searching establishes the file is unsafe, Chrome will show a warning.”
Inspite of the file being labeled as possibly unsafe, customers nevertheless have the option to open up the file with no scanning. Should really people opt to scan the file, the company claimed the uploaded information are deleted from Risk-free Searching a small time after scanning, but did not specify the precise timeframe for removal.
The new functions are offered beginning with Chrome 91, the model of the browser that was introduced on May perhaps 26. Users can flip on Increased Secure Searching by traveling to Options > Privacy and security > Security > Enhanced safety.
Identified this write-up fascinating? Comply with THN on Fb, Twitter and LinkedIn to read through additional special material we submit.
Some areas of this short article are sourced from:
thehackernews.com


 Supreme Court narrows interpretation of CFAA, to the relief of ethical hackers
Supreme Court narrows interpretation of CFAA, to the relief of ethical hackers