Menace intelligence scientists from Google on Wednesday get rid of more light-weight on 4 in-the-wild zero-days in Chrome, Safari, and Internet Explorer browsers that have been exploited by malicious actors in different strategies since the commence of the calendar year.
What’s additional, a few of the 4 zero-times have been engineered by commercial providers and bought to and utilised by federal government-backed actors, contributing to an uptick in real-world attacks. The record of now-patched vulnerabilities is as follows –
- CVE-2021-1879: Use-Soon after-Free in QuickTimePluginReplacement (Apple WebKit)
- CVE-2021-21166: Chrome Item Lifecycle Issue in Audio
- CVE-2021-30551: Chrome Type Confusion in V8
- CVE-2021-33742: Internet Explorer out-of-bounds write in MSHTML
Both of those Chrome zero-times — CVE-2021-21166 and CVE-2021-30551 — are believed to have been utilized by the very same actor, and were shipped as one particular-time inbound links despatched by way of email to targets located in Armenia, with the hyperlinks redirecting unsuspecting buyers to attacker-managed domains that masqueraded as authentic web-sites of desire to the recipients.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code

The destructive internet sites took cost of fingerprinting the units, including collecting technique information and facts about the shoppers, before offering a 2nd-stage payload.
When Google rolled out a patch for CVE-2021-30551, Shane Huntley, Director of Google’s Danger Assessment Group (TAG), discovered that the vulnerability was leveraged by the similar actor that abused CVE-2021-33742, an actively exploited remote code execution flaw in Windows MSHTML system that was tackled by Microsoft as part of its Patch Tuesday update on June 8.
The two zero-days ended up offered by a business exploit broker to a country-state adversary, which utilised them in confined attacks in opposition to targets in Japanese Europe and the Middle East, Huntley formerly included.
Now according to a specialized report posted by the crew, all the three zero-times were being “developed by the very same commercial surveillance organization that sold these abilities to two various government-backed actors,” including the Internet Explorer flaw was utilized in a marketing campaign concentrating on Armenian users with destructive Office environment paperwork that loaded web content inside the web browser.
Google did not disclose the identities of the exploit broker or the two menace actors that employed the vulnerabilities as aspect of their attacks.
The Safari zero-day, in contrast, concerned a WebKit flaw that could allow adversaries to course of action maliciously crafted web content material that may possibly outcome in universal cross-web-site scripting attacks. The issue was tackled by Apple on March 26, 2021.
SolarWinds Hackers Exploited iOS Zero-Day
Attacks leveraging CVE-2021-1879, which Google attributed to a “likely Russian govt-backed actor,” were executed by means of sending destructive backlinks to govt officers over LinkedIn that, when clicked from an iOS unit, redirected the consumer to a rogue domain that served the up coming-phase payloads.

It is really truly worth noting that the offensive also mirrors a wave of targeted attacks unleashed by Russian hackers tracked as Nobelium, which was observed abusing the vulnerability to strike authorities businesses, believe tanks, consultants, and non-governmental corporations as element of an email phishing campaign.
Nobelium, a risk actor connected to the Russian International Intelligence Assistance (SVR), is also suspected of orchestrating the SolarWinds offer chain attack late very last year. It’s acknowledged by other aliases such as APT29, UNC2452 (FireEye), SolarStorm (Unit 42), StellarParticle (Crowdstrike), Dark Halo (Volexity), and Iron Ritual (Secureworks).
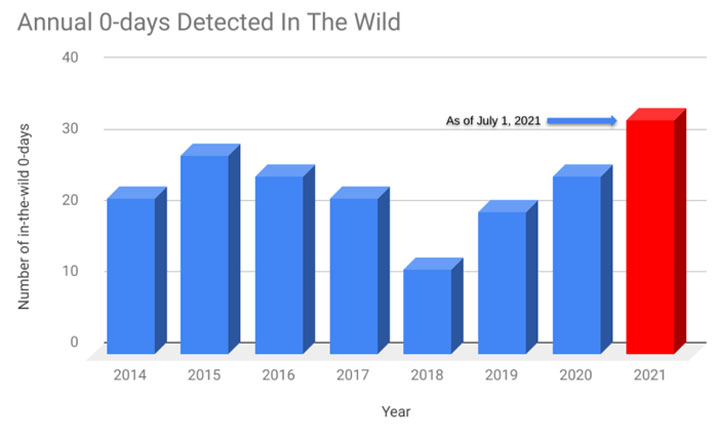
“Midway into 2021, there have been 33 zero-day exploits utilised in attacks that have been publicly disclosed this calendar year — 11 far more than the full range from 2020,” TAG researchers Maddie Stone and Clement Lecigne famous. “While there is an enhance in the range of zero-working day exploits remaining utilized, we consider higher detection and disclosure endeavours are also contributing to the upward development.”
Discovered this posting attention-grabbing? Comply with THN on Facebook, Twitter and LinkedIn to study a lot more exclusive content material we article.
Some areas of this article are sourced from:
thehackernews.com


 What is island hopping?
What is island hopping?