In January 2019, a critical flaw was documented in Apple’s FaceTime team chats attribute that designed it achievable for buyers to initiate a FaceTime video clip simply call and eavesdrop on targets by including their personal quantity as a 3rd individual in a group chat even right before the human being on the other stop recognized the incoming phone.
The vulnerability was considered so critical that the iPhone maker removed the FaceTime team chats aspect altogether ahead of the issue was resolved in a subsequent iOS update.
Since then, a amount of similar shortcomings have been found out in multiple video clip chat applications these types of as Sign, JioChat, Mocha, Google Duo, and Fb Messenger — all thanks to the get the job done of Google Undertaking Zero researcher Natalie Silvanovich.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
“Though [the Group FaceTime] bug was before long mounted, the reality that these types of a really serious and straightforward to reach vulnerability experienced happened owing to a logic bug in a calling condition equipment — an attack situation I experienced in no way noticed regarded as on any platform — manufactured me wonder irrespective of whether other condition machines experienced very similar vulnerabilities as nicely,” Silvanovich wrote in a Tuesday deep-dive of her function.
How Signaling in WebRTC Operates?
Although a bulk of the messaging apps these days count on WebRTC for interaction, the connections themselves are made by exchanging connect with set-up data utilizing Session Description Protocol (SDP) concerning friends in what is actually known as signaling, which usually functions by sending an SDP provide from the caller’s conclude, to which the callee responds with an SDP respond to.
Set in different ways, when a person starts off a WebRTC connect with to one more consumer, a session description referred to as an “present” is made made up of all the details required environment up a connection — the form of media being despatched, its structure, the transfer protocol utilized, and the endpoint’s IP handle and port, between others. The recipient then responds with an “solution,” like a description of its endpoint.
The full course of action is a condition device, which signifies “the place in the method of signaling the exchange of present and respond to the link at this time is.”
Also bundled optionally as component of the present/respond to trade is the potential of the two friends to trade SDP candidates to each individual other so as to negotiate the actual connection in between them. It facts the techniques that can be used to converse, irrespective of the network topology — a WebRTC framework known as Interactive Connectivity Establishment (ICE).
Once the two friends concur upon a mutually-compatible applicant, that candidate’s SDP is applied by each peer to build and open a connection, by means of which media then commences to flow.
In this way, the two gadgets share with one a further the data wanted in buy to exchange audio or video around the peer-to-peer link. But before this relay can materialize, the captured media information has to be attached to the link making use of a feature named tracks.
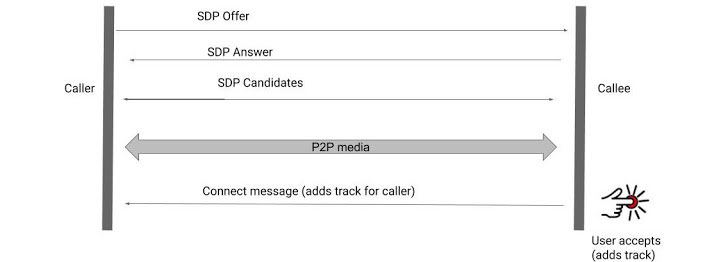
Although it’s anticipated that callee consent is ensured forward of audio or video transmission and that no details is shared right up until the receiver has interacted with the software to solution the call (i.e., before introducing any tracks to the link), Silvanovich noticed actions to the contrary.
Several Messaging Apps Influenced
Not only did the flaws in the applications let calls to be linked without having interaction from the callee, but they also potentially permitted the caller to power a callee device to transmit audio or video clip facts.
- Signal (mounted in September 2019) – A audio connect with flaw in Signal’s Android application designed it possible for the caller to hear the callee’s environment owing to the truth that the app failed to look at if the gadget obtaining the link message from the callee was the caller unit.
- JioChat (fastened in July 2020) and Mocha (set in August 2020) – Introducing candidates to the provides established by Reliance JioChat and Viettel’s Mocha Android apps that authorized a caller to pressure the goal gadget to deliver audio (and movie) with out a user’s consent. The flaws stemmed from the simple fact that the peer-to-peer link experienced been established up even ahead of the callee answered the call, therefore raising the “remote attack surface of WebRTC.”
- Facebook Messenger (set in November 2020) – A vulnerability that could have granted an attacker who is logged into the application to concurrently initiate a connect with and deliver a specifically crafted information to a target who is signed in to equally the application as effectively as yet another Messenger customer this sort of as the web browser, and get started acquiring audio from the callee unit.
- Google Duo (fastened in December 2020) – A race problem amongst disabling the movie and setting up the link that, in some circumstances, could result in the callee to leak video clip packets from unanswered phone calls.
Other messaging apps like Telegram and Viber were being identified to have none of the over flaws, whilst Silvanovich famous that major reverse engineering difficulties when analyzing Viber designed the investigation “significantly less rigorous” than the other individuals.
“The majority of contacting state machines I investigated had logic vulnerabilities that allowed audio or video content material to be transmitted from the callee to the caller without the need of the callee’s consent,” Silvanovich concluded. “This is evidently an spot that is generally neglected when securing WebRTC applications.”
“The majority of the bugs did not show up to be owing to developer misunderstanding of WebRTC capabilities. Rather, they were due to errors in how the point out equipment are applied. That explained, a absence of recognition of these varieties of issues was probable a factor,” she extra.
“It is also about to note that I did not look at any team calling options of these applications, and all the vulnerabilities described ended up located in peer-to-peer phone calls. This is an spot for long term operate that could reveal supplemental challenges.”
Found this short article attention-grabbing? Abide by THN on Facebook, Twitter and LinkedIn to read through more special content material we post.
Some parts of this report are sourced from:
thehackernews.com

 SolarWinds hackers hit Malwarebytes through Microsoft exploit
SolarWinds hackers hit Malwarebytes through Microsoft exploit