Applications on Android have been ready to infer the existence of precise applications, or even accumulate the complete listing of installed apps on the system. What is more, an app can also set to be notified when a new app is mounted.
Apart from all the standard concerns about misuse of this sort of a knowledge grab, the information and facts can be abused by a most likely damaging application to fingerprint other installed apps, check out for the existence of antivirus, affiliate fraud, and even for focused adverts.
In 2014, Twitter began tracking the listing of applications installed on users’ units as part of its “app graph” initiative with an purpose to supply tailor-made content. Digital wallet organization MobiKwik was also caught gathering details about installed applications in the wake of a data breach that came to light before this 7 days.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
In fact, a study undertaken by a team of Swiss researchers in 2019 observed that “cost-free apps are far more possible to query for these facts and that 3rd-party libraries (libs) are the principal requesters of the checklist of put in applications.”
“As buyers have on common 80 apps installed on their telephones, most of them being no cost, there is a superior chance of untrusted third-events getting the list of mounted applications,” the scientists additional.
A further tutorial analyze posted in March 2020 also located that 4,214 Google Enjoy apps stealthily amassed a record of all other mounted apps, therefore allowing builders and advertisers to build comprehensive profiles of users. Applications that do so typically realize this by creating use of what is actually named set up application methods — getInstalledPackages() and getInstalledApplications() — with the researchers uncovering that applications in online games, comics, personalization, autos and cars, and loved ones classes topped the list of applications collecting this data.
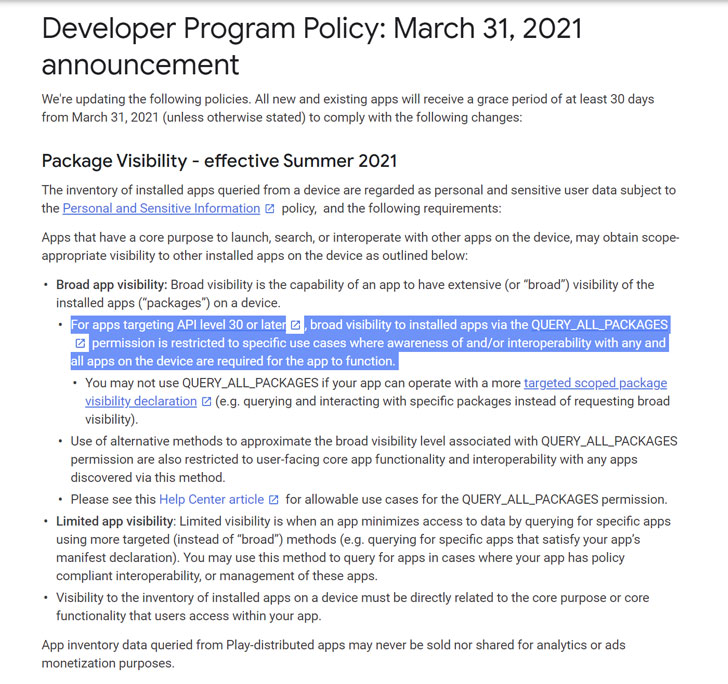
Previous calendar year, Google tried to rein in this actions by avoiding apps from accessing this info by default setting up Android 11, although also introducing new permission called “Query_ALL_Deals” for apps that need to have access to the record of other installed applications.
“This filtering actions aids minimize the volume of probably sensitive facts that your application will not want in purchase to satisfy its use instances, but that your application can still entry,” Google claimed.
Now in an try to step up its initiatives to limit the misuse of the Question_ALL_Packages permission, Google has reported it treats the inventory of installed applications as personal and delicate user information.
Productive May perhaps 5, 2021, the permission will be restricted to only all those apps that are made use of for unit look for, as well as antivirus apps, file administrators, and browsers. Other applications these types of as a devoted banking app or a electronic wallet app can qualify for this permission exclusively for security-centered uses.
Google also mentioned it wouldn’t permit applications to ask for the Query_ALL_Offers permission when the “information is obtained for the objective of sale” or the required endeavor can be realized by an substitute system.
“Applications that are unsuccessful to satisfy policy necessities or do not post a Declaration Sort could be removed from Google Participate in,” the enterprise noted. “If you modify how your app utilizes these restricted permissions, you ought to revise your declaration with updated and exact data. Deceptive and non-declared uses of these permissions may perhaps end result in a suspension of your application and/or termination of your developer account.”
Observed this post exciting? Observe THN on Fb, Twitter and LinkedIn to go through extra exclusive written content we submit.
Some sections of this article are sourced from:
thehackernews.com


 Conti ransomware gang hits Broward County Schools with $40M demand
Conti ransomware gang hits Broward County Schools with $40M demand