A workforce of security researchers from Google has shown still one more variant of the Rowhammer attack that bypasses all present-day defenses to tamper with facts stored in memory.
Dubbed “50 percent-Double,” the new hammering method hinges on the weak coupling concerning two memory rows that are not right away adjacent to just about every other but a single row removed.
“Not like TRRespass, which exploits the blind spots of maker-dependent defenses, 50 %-Double is an intrinsic residence of the underlying silicon substrate,” the scientists mentioned.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount

“This is most likely an indicator that the electrical coupling accountable for Rowhammer is a house of distance, proficiently getting to be much better and extended-ranged as cell geometries shrink down. Distances increased than two are conceivable.”
Rowhammer attacks are similar to speculative execution in that both of those crack the essential security assures produced by the underlying hardware. Found in 2014, Rowhammer refers to a course of DRAM vulnerabilities whereby repeated accesses to a memory row (“aggressor”) can induce an electrical disturbance large more than enough to flip bits saved in an adjacent row (“victim”), therefore making it possible for untrusted code to escape its sandbox and consider over control of the process.
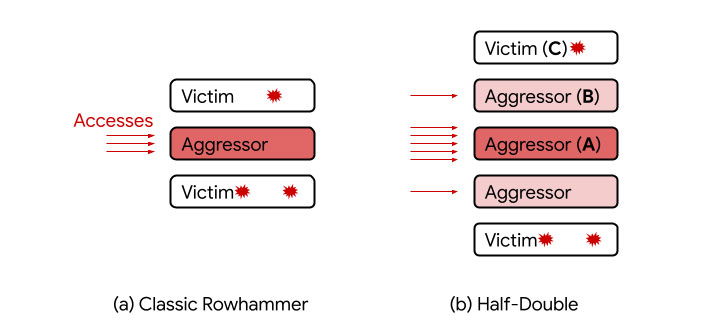
Whilst DRAM companies deployed countermeasures like Target Row Refresh (TRR) to thwart such attacks, the mitigations have been restricted to two speedy neighbors of an aggressor row, hence excluding memory cells at a two-row distance. The imperfect protections intended TRR defenses in DDR4 cards could be circumvented to phase new variants of Rowhammer attacks these kinds of as TRRespass and SMASH.
The distance-two assisted Rowhammer — aka 50 %-Double — now joins that list. “Offered three consecutive rows A, B, and C, we have been ready to attack C by directing a really massive quantity of accesses to A, together with just a handful (~dozens) to B,” the researchers spelled out. In this new setup, A is the “considerably aggressor,” B is the “in the vicinity of aggressor,” and C is the “target.”
Google explained it is at present performing with the Joint Electron Gadget Engineering Council (JEDEC), an impartial standardization entire body and semiconductor engineering trade firm, along with other industry companions, to establish possible remedies for Rowhammer exploits.
“To assess the effectiveness of a [SoC-level] mitigation, a DRAM vendor should check a combine of hammering distances somewhat than only screening at personal distances,” the researchers mentioned. “In other phrases, hammering a single row or a pair of sandwiching rows on the raw medium will not display this result. Instead, pairs of rows on one or equally sides of an meant target have to have to be hammered.”
Uncovered this post exciting? Stick to THN on Facebook, Twitter and LinkedIn to examine extra exceptional written content we write-up.
Some parts of this article are sourced from:
thehackernews.com

 Russian Hydra DarkNet Market Made Over $1.3 Billion in 2020
Russian Hydra DarkNet Market Made Over $1.3 Billion in 2020