Google Venture Zero on Thursday disclosed aspects of a new security system that Apple quietly additional to iOS 14 as a countermeasure to protect against attacks that ended up not long ago uncovered to leverage zero-days in its messaging app.
Dubbed “BlastDoor,” the enhanced sandbox technique for iMessage info was disclosed by Samuel Groß, a security researcher with Undertaking Zero, a crew of security scientists at Google tasked with finding out zero-working day vulnerabilities in hardware and computer software devices.
“1 of the key variations in iOS 14 is the introduction of a new, tightly sandboxed ‘BlastDoor’ service which is now accountable for virtually all parsing of untrusted knowledge in iMessages,” Groß explained. “Additionally, this service is written in Swift, a (mainly) memory harmless language which tends to make it drastically more challenging to introduce classic memory corruption vulnerabilities into the code base.”

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount

The advancement is a consequence of a zero-click exploit that leveraged an Apple iMessage flaw in iOS 13.5.1 to get all-around security protections as portion of a cyberespionage campaign targeting Al Jazeera journalists previous 12 months.
“We do not think that [the exploit] operates versus iOS 14 and over, which involves new security protections,” Citizen Lab scientists who exposed the attack very last month.
BlastDoor kinds the core of individuals new security protections, for each Groß, who analyzed the applied alterations more than the system of a week-long reverse engineering challenge making use of an M1 Mac Mini functioning macOS 11.1 and an iPhone XS jogging iOS 14.3.
When an incoming iMessage arrives, the message passes by a quantity of solutions, main amongst them currently being the Apple Force Notification Services daemon (apsd) and a track record procedure named imagent, which is not only accountable for decoding the message contents but also for downloading attachments (via a different support referred to as IMTransferAgent) and handling one-way links to web sites, ahead of alerting the SpringBoard to show the notification.
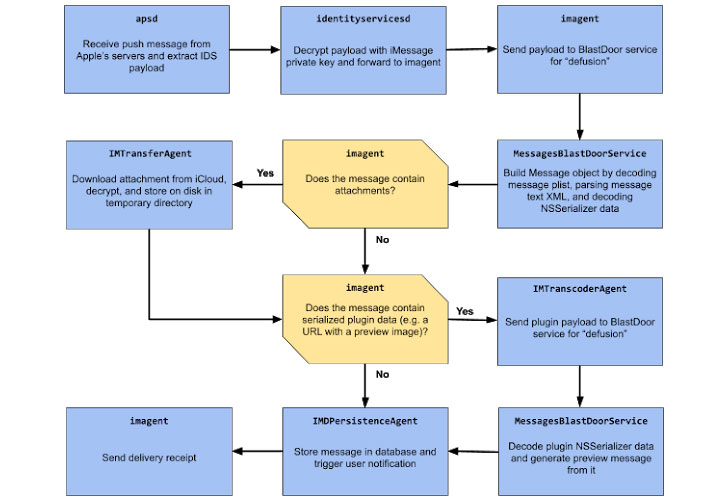
What BlastDoor does is examine all this sort of inbound messages in a safe, sandboxed ecosystem, which stops any destructive code within of a information from interacting with the relaxation of the working process or accessing user info.
Set in a different way, by moving a the greater part of the processing duties — i.e., decoding the message property listing and building link previews — from imagent to this new BlastDoor part, a specially-crafted concept despatched to a target can no for a longer time interact with the file procedure or perform network operations.
“The sandbox profile is fairly restricted,” Groß pointed out. “Only a handful of nearby IPC providers can be arrived at, pretty much all file system interaction is blocked, any interaction with IOKit drivers is forbidden, [and] outbound network access is denied.”
What is additional, in a bid to delay subsequent restarts of a crashing assistance, Apple has also launched a new throttling aspect in the iOS “launchd” approach to limit the variety of tries an attacker will get when trying to get to exploit a flaw by exponentially escalating the time amongst two successive brute-pressure attempts.
“With this adjust, an exploit that relied on frequently crashing the attacked service would now possible demand in the get of various hours to around half a day to complete as a substitute of a handful of minutes,” Groß reported.
“All round, these improvements are likely quite close to the greatest that could’ve been performed provided the have to have for backwards compatibility, and they really should have a major affect on the security of iMessage and the system as a full.”
Found this short article appealing? Comply with THN on Fb, Twitter and LinkedIn to read through more unique content material we post.
Some elements of this article are sourced from:
thehackernews.com


 #DataPrivacyDay: Organizations Must Increase Focus on Data Privacy in 2021
#DataPrivacyDay: Organizations Must Increase Focus on Data Privacy in 2021