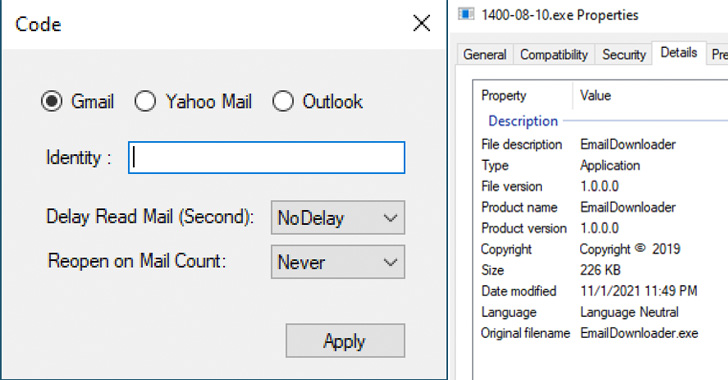
The Iranian govt-backed actor regarded as Charming Kitten has extra a new tool to its malware arsenal that allows it to retrieve user facts from Gmail, Yahoo!, and Microsoft Outlook accounts.
Dubbed HYPERSCRAPE by Google Danger Analysis Team (TAG), the actively in-development malicious program is mentioned to have been utilized in opposition to less than two dozen accounts in Iran, with the oldest acknowledged sample relationship back to 2020. The software was 1st discovered in December 2021.
Charming Kitten, a prolific highly developed persistent threat (APT), is considered to be associated with Iran’s Islamic Innovative Guard Corps (IRGC) and has a history of conducting espionage aligned with the passions of the government.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount

Tracked as APT35, Cobalt Illusion, ITG18, Phosphorus, TA453, and Yellow Garuda, factors of the team have also carried out ransomware attacks, suggesting that the menace actor’s motives are both espionage and monetarily driven.
“HYPERSCRAPE demands the victim’s account qualifications to operate making use of a legitimate, authenticated person session the attacker has hijacked, or qualifications the attacker has currently obtained,” Google TAG researcher Ajax Bash reported.
Composed in .NET and developed to operate on the attacker’s Windows device, the tool will come with features to obtain and exfiltrate the contents of a victim’s email inbox, in addition to deleting security e-mails sent from Google to inform the concentrate on of any suspicious logins.
Must a information be initially unread, the resource marks it as unread after opening and downloading the email as a “.eml” file. What’s a lot more, earlier variations of HYPERSCRAPE are explained to have integrated an selection to ask for knowledge from Google Takeout, a attribute that allows consumers to export their data to a downloadable archive file.

The findings observe the latest discovery of a C++-dependent Telegram “grabber” software by PwC made use of against domestic targets to get hold of accessibility to Telegram messages and contacts from unique accounts.
Previously, the group was spotted deploying a custom made Android surveillanceware termed LittleLooter, a feature-prosperous implant able of collecting sensitive info stored in the compromised devices as very well as recording audio, online video, and calls.
“Like a great deal of their tooling, HYPERSCRAPE is not noteworthy for its specialized sophistication, but fairly its success in accomplishing Charming Kitten’s targets,” Bash reported. The impacted accounts have considering the fact that been re-secured and the victims notified.
Uncovered this short article intriguing? Abide by THN on Facebook, Twitter and LinkedIn to examine extra exceptional content we post.
Some pieces of this posting are sourced from:
thehackernews.com

 NEC and Fortinet partner to deliver high-performance security for 5G networks
NEC and Fortinet partner to deliver high-performance security for 5G networks