Cybersecurity researchers have disclosed a novel procedure adopted by threat actors to deliberately evade detection with the assistance of malformed digital signatures of its malware payloads.
“Attackers developed malformed code signatures that are treated as legitimate by Windows but are not ready to be decoded or checked by OpenSSL code — which is utilised in a number of security scanning solutions,” Google Danger Investigation Group’s Neel Mehta reported in a publish-up published on Thursday.
The new mechanism was noticed to be exploited by a notorious household of unwanted application identified as OpenSUpdater which is utilised to obtain and set up other suspicious programs on compromised systems. Most targets of the marketing campaign are consumers situated in the U.S. who are prone to downloading cracked versions of games and other gray-spot software package.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
The findings come from a set of OpenSUpdater samples uploaded to VirusTotal at least since mid-August.
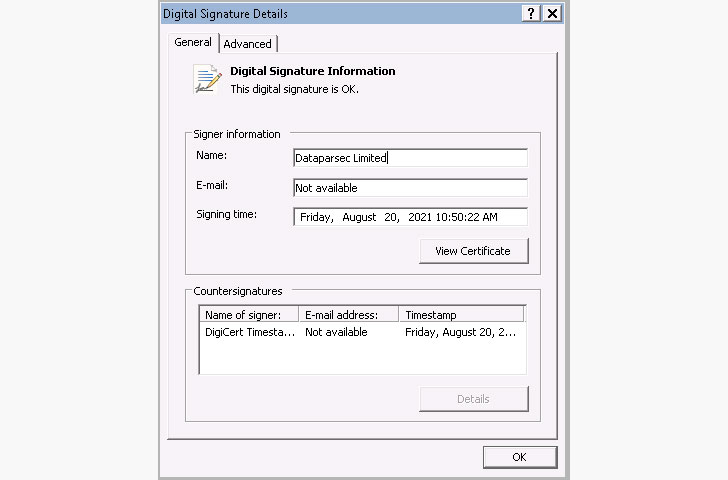
Not only are the artifacts signed with an invalid leaf X.509 certification that’s edited in these kinds of a fashion that the ‘parameters’ factor of the SignatureAlgorithm area incorporated an Close-of-Written content (EOC) marker rather of a NULL tag. While this sort of encodings are rejected as invalid by-products using OpenSSL to retrieve signature info, checks on Windows techniques would allow the file to be run without the need of any security warnings.

“This is the to start with time TAG has noticed actors making use of this method to evade detection even though preserving a legitimate electronic signature on PE documents,” Mehta stated.
“Code signatures on Windows executables offer assures about the integrity of a signed executable, as nicely as info about the id of the signer. Attackers who are ready to obscure their identity in signatures devoid of influencing the integrity of the signature can prevent detection more time and prolong the life time of their code-signing certificates to infect much more programs.”
Identified this short article fascinating? Adhere to THN on Fb, Twitter and LinkedIn to go through extra exceptional articles we write-up.
Some pieces of this posting are sourced from:
thehackernews.com


 HP Wolf Security: Threat insights report
HP Wolf Security: Threat insights report