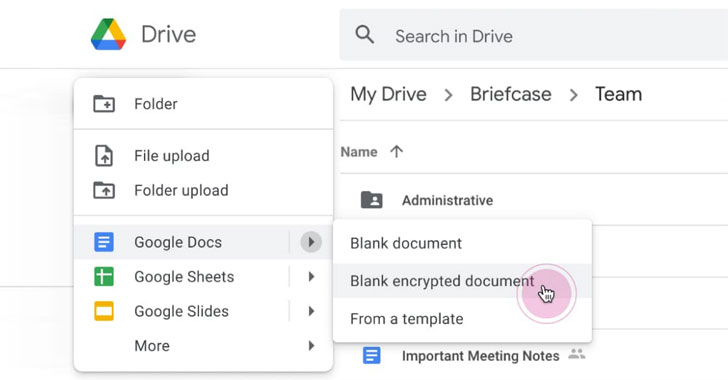
Google on Monday introduced that it is really rolling out consumer-facet encryption to Google Workspace (formerly G Suite), thus offering its organization prospects direct management of encryption keys and the identification provider they select to entry all those keys.
“With consumer-side encryption, buyer details is indecipherable to Google, although customers can carry on to choose advantage of Google’s native web-primarily based collaboration, accessibility material on cellular units, and share encrypted documents externally,” the look for large reported.
“When put together with our other encryption capabilities, buyers can insert new stages of knowledge defense for their Google Workspace info.”

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
The progress coincides with the Google Workspace and Google Chat’s broader availability to all end users with a Google account. Workspace is the company’s company offering consisting of Gmail, Chat, Calendar, Drive, Docs, Sheets, Slides, Fulfill, and other applications.
Companies making use of Google Workspace have the option of storing their encryption keys with 1 of 4 associates — Flowcrypt, Futurex, Thales, or Virtru — which the organization explained give both vital administration and access regulate abilities that are compatible with Google’s specs.
The entry company then retains the important dependable for deciphering encrypted Google Workspace data files, placing them out of access of Google unless of course it will come in possession of the crucial.
The shift is aimed at organizations that deal with delicate or controlled data, like mental residence, healthcare records, or monetary facts, therefore enabling them to meet up with stringent privacy and compliance necessities.
What’s additional, Google intends to publish the vital accessibility services API specifications that can be utilized in conjunction with customer-facet encryption afterwards this 12 months in a bid to let enterprises to construct their very own in-house key remedies and give them full command about the encryption keys.

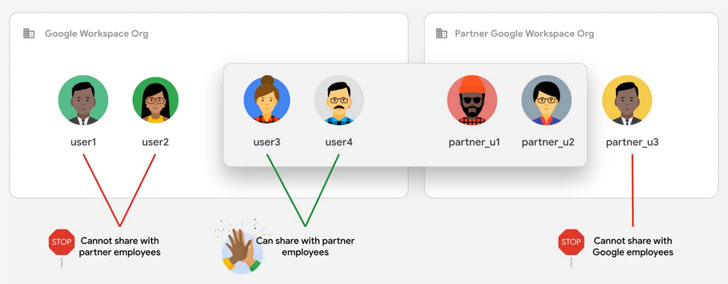
Along with shopper-facet encryption, the company is also setting new “rely on regulations” when it arrives to how data files can be shared, both of those inside and exterior of their organization, permitting directors “implement constraints that limit internal and exterior sharing.”
Furthermore, Google is turning on phishing and malware content defense for Google Travel to block destructive documents from currently being shared in companies.
“If abusive information is found, the related file is flagged and produced noticeable only to admins and the file’s proprietor,” Google stated. “This stops sharing and reduces the number of people probably impacted by the abusive content.”
Observed this short article exciting? Stick to THN on Facebook, Twitter and LinkedIn to study far more distinctive material we put up.
Some components of this write-up are sourced from:
thehackernews.com

 User risk report: Educate your workforce to protect your organisation
User risk report: Educate your workforce to protect your organisation