A framework notorious for providing a banking Trojan has obtained a facelift to deploy a wider range of malware, including ransomware payloads.
“The Gootkit malware spouse and children has been around extra than 50 % a decade – a experienced Trojan with features centered all around banking credential theft,” Sophos researchers Gabor Szappanos and Andrew Brandt mentioned in a generate-up posted these days.
“In the latest years, practically as substantially hard work has absent into advancement of its delivery method as has gone into the NodeJS-based mostly malware by itself.”

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
Dubbed “Gootloader,” the expanded malware supply system comes amid a surge in the variety of infections focusing on customers in France, Germany, South Korea, and the U.S.
To start with documented in 2014, Gootkit is a Javascript-based mostly malware platform able of carrying out an array of covert pursuits, including web injection, capturing keystrokes, having screenshots, recording videos, as nicely as email and password theft.
More than the decades, the cybercrime instrument has advanced to obtain new information-thieving options, with the Gootkit loader repurposed in blend with REvil/Sodinokibi ransomware bacterial infections claimed last 12 months.
Although strategies utilizing social engineering methods to supply destructive payloads are a dime a dozen, Gootloader can take it to the up coming level.
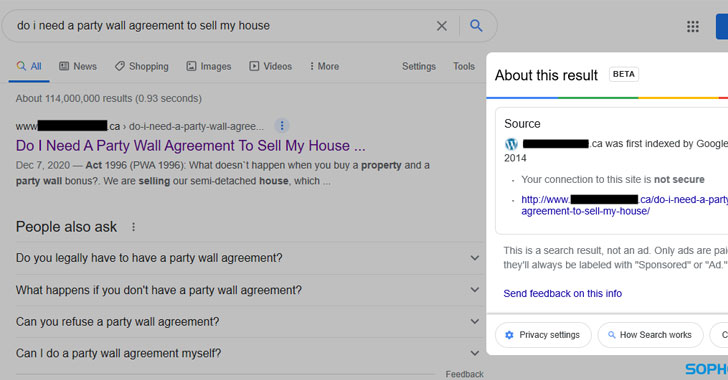
The infection chain resorts to subtle strategies that entail hosting malicious ZIP archive data files on internet sites belonging to legitimate firms that have been gamed to surface between the major results of a look for query working with manipulated look for engine optimization (Seo) strategies.
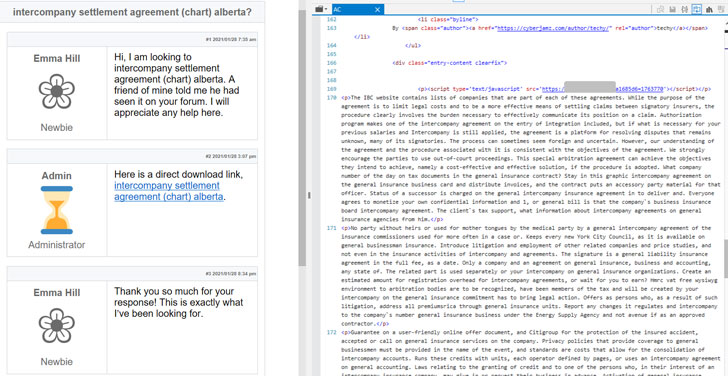
What is extra, the look for motor effects point to internet sites that have no “sensible” relationship to the look for query, implying that the attackers should be in possession of a wide network of hacked sites. In one particular scenario spotted by the scientists, an tips for a authentic estate arrangement surfaced a breached neonatal health care practice centered in Canada as the first final result.
“To make sure targets from the right geographies are captured, the adversaries rewrite web page code ‘on the go’ so that web-site readers who drop outside the house the preferred nations are demonstrated benign web information, while people from the appropriate site are proven a site that includes a faux dialogue discussion board on the subject they’ve queried,” the researchers stated.
Clicking the research result normally takes the user to a bogus concept board-like webpage that matches not only the lookup phrases employed in the original query but also features a url to the ZIP file, which consists of a closely obfuscated Javascript file that initiates the future stage of compromise to inject the fileless malware fetched from a remote server into memory.
This will take the sort of a multi-stage evasive method that starts with a .NET loader, which includes a Delphi-based loader malware, which, in switch, is made up of the remaining payload in encrypted variety.
In addition to providing the REvil ransomware and the Gootkit trojan, various strategies have been noticed presently leveraging the Gootloader framework to supply the Kronos monetary malware in Germany stealthily, and the Cobalt Strike write-up-exploitation resource in the U.S.
It’s however unclear as to how the operators get access to the internet sites to provide the destructive injects, but the scientists suspect the attackers could have received the passwords by putting in the Gootkit malware or getting stolen credentials from underground marketplaces, or by leveraging security flaws in existing in the plugins utilized along with information management technique (CMS) computer software.
“The builders guiding Gootkit seem to have shifted methods and electricity from offering just their personal economical malware to building a stealthy, intricate shipping platform for all kinds of payloads, together with REvil ransomware,” said Gabor Szappanos, risk investigation director at Sophos.
“This exhibits that criminals are likely to reuse their verified solutions in its place of building new shipping mechanisms. More, as a substitute of actively attacking endpoint instruments as some malware distributors do, the creators of Gootloader have opted for convoluted evasive tactics that conceal the end end result,” he extra.
Uncovered this article intriguing? Observe THN on Facebook, Twitter and LinkedIn to read far more exceptional material we publish.
Some parts of this write-up are sourced from:
thehackernews.com

 70% of Orgs Facing New Security Challenges Due to #COVID19 Pandemic
70% of Orgs Facing New Security Challenges Due to #COVID19 Pandemic