Techniques hosting articles pertaining to the Countrywide Video games of China have been correctly breached last 12 months by an unnamed Chinese-language-speaking hacking team.
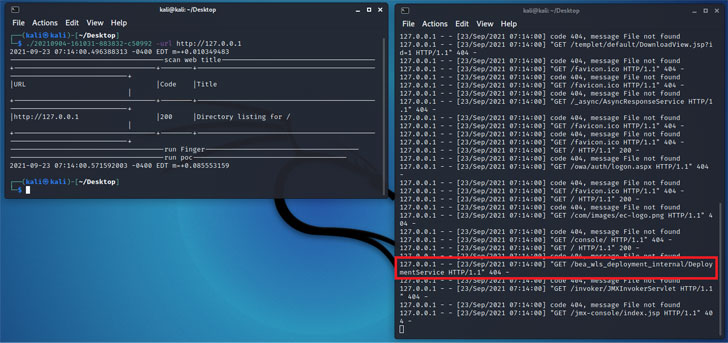
Cybersecurity organization Avast, which dissected the intrusion, mentioned that the attackers acquired accessibility to a web server 12 times prior to the commence of the event on September 3 to drop multiple reverse web shells for remote entry and attain long term foothold in the network.
The National Game titles of China, a multi-sport party held each four years, took position in the Shaanxi Province concerning September 15 and 27, 2021.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
The Czech business claimed it was unable to figure out the mother nature of the details stolen by the hackers, including it has “cause to believe [the attackers] are either native Chinese-language speakers or exhibit substantial fluency in Chinese.” The breach is said to have been solved ahead of the begin of the games.
The preliminary accessibility was facilitated by exploiting a vulnerability in the webserver. But in advance of dropping the web shells, the adversary also experimented with the style of information that they have been equipped to add to the server, only to adhere to it up with submitting executable code that masqueraded as seemingly harmless photos files.
Furthermore, makes an attempt had been designed to reconfigure the server to execute the Behinder web shell, failing which the operators “uploaded and ran an overall Tomcat server thoroughly configured and weaponized” with the write-up-exploitation tool.
“Just after attaining accessibility, the attackers experimented with to move via the network working with exploits and bruteforcing solutions in an automatic way,” Avast researchers David Álvarez Pérez and Jan Neduchal mentioned.
Amid other instruments uploaded to the server incorporated a network scanner and a customized a single-click on exploitation framework prepared in Go that enabled the risk actor to have out lateral motion and autonomously break into other units within the very same network.
“Go is a programming language turning out to be additional and much more well-liked which can be compiled for several functioning units and architectures, in a one binary self-that contains all dependencies,” the researchers mentioned, contacting out the expanding use of Go-primarily based malware to carry out cyber attacks.
“So we be expecting to see malware and grey tools composed in this language in foreseeable future attacks, specifically in [Internet of things] attacks where by a wide wide range of devices leveraging distinctive sorts of processor architectures are concerned.”
Uncovered this report exciting? Comply with THN on Facebook, Twitter and LinkedIn to examine additional exclusive articles we write-up.
Some sections of this post are sourced from:
thehackernews.com



 IoT/connected Device Discovery and Security Auditing in Corporate Networks
IoT/connected Device Discovery and Security Auditing in Corporate Networks