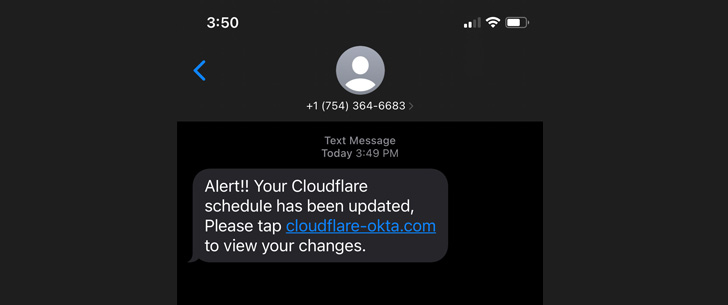
Web infrastructure organization Cloudflare on Tuesday disclosed at the very least 76 staff members and their loved ones members acquired textual content messages on their particular and get the job done phones bearing equivalent attributes as that of the sophisticated phishing attack towards Twilio.
The attack, which transpired close to the same time Twilio was specific, was eventually unsuccessful.


Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
The wave of around 100 smishing messages commenced less than 40 minutes after the rogue area was registered by way of Porkbun, the organization mentioned, incorporating the phishing website page was made to relay the credentials entered by unsuspecting people to the attacker by means of Telegram in authentic-time.
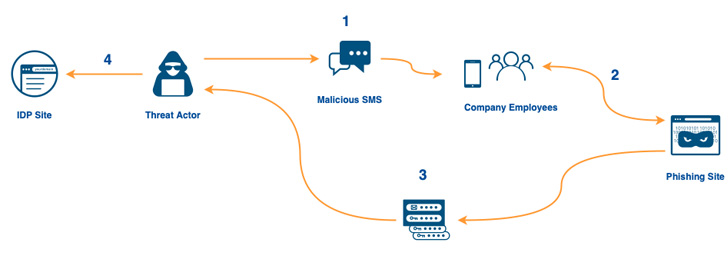
This also meant that the attack could defeat 2FA roadblocks, as the Time-centered A person Time Password (TOTP) codes inputted on the pretend landing webpage have been transmitted in an analogous method, enabling the adversary to sign-in with the stolen passwords and TOTPs.
Cloudflare explained three of its staff members fell for the phishing plan, but pointed out that it was equipped to avoid its internal systems from getting breached by means of the use of FIDO2-compliant physical security keys essential to entry its programs.
“Given that the tricky keys are tied to consumers and implement origin binding, even a advanced, serious-time phishing procedure like this are not able to acquire the data vital to log in to any of our systems,” Cloudflare reported.
“Even though the attacker tried to log in to our methods with the compromised username and password qualifications, they could not get previous the difficult critical prerequisite.”

What is actually more, the attacks didn’t just prevent at thieving the credentials and TOTP codes. Need to an staff get previous the login stage, the phishing website page was engineered to immediately down load AnyDesk’s distant entry software program, which, if mounted, could be employed to commandeer the victim’s program.
Moreover operating with DigitalOcean to shut down the attacker’s server, the company also claimed it reset the qualifications of the impacted staff and that it’s tightening up its obtain implementation to avoid any logins from unfamiliar VPNs, residential proxies, and infrastructure vendors.
The growth arrives times soon after Twilio reported unknown hackers succeeded in phishing the qualifications of an undisclosed number of workforce and acquired unauthorized access to the firm’s inside methods, working with it to get maintain of client accounts.
Discovered this write-up appealing? Adhere to THN on Fb, Twitter and LinkedIn to go through extra exceptional content material we put up.
Some components of this post are sourced from:
thehackernews.com


 Exploit Activity Surges 150% in Q2 Thanks to Log4Shell
Exploit Activity Surges 150% in Q2 Thanks to Log4Shell