NuGet, PyPi, and npm ecosystems are the concentrate on of a new campaign that has resulted in more than 144,000 packages becoming released by unfamiliar danger actors.
“The packages were being section of a new attack vector, with attackers spamming the open-resource ecosystem with offers that contains inbound links to phishing campaigns,” scientists from Checkmarx and Illustria explained in a report printed Wednesday.
Of the 144,294 phishing-connected deals that were detected, 136,258 have been released on NuGet, 7,824 on PyPi, and 212 on npm. The offending libraries have considering that been unlisted or taken down.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount

Even more evaluation has uncovered that the total approach was automated and that the offers were being pushed more than a small span of time, with a the greater part of the usernames adhering to the conference “
The bogus offers themselves claimed to offer hacks, cheats, and no cost means in an endeavor to trick users into downloading them. The URLs to the rogue phishing webpages ended up embedded in the bundle description.
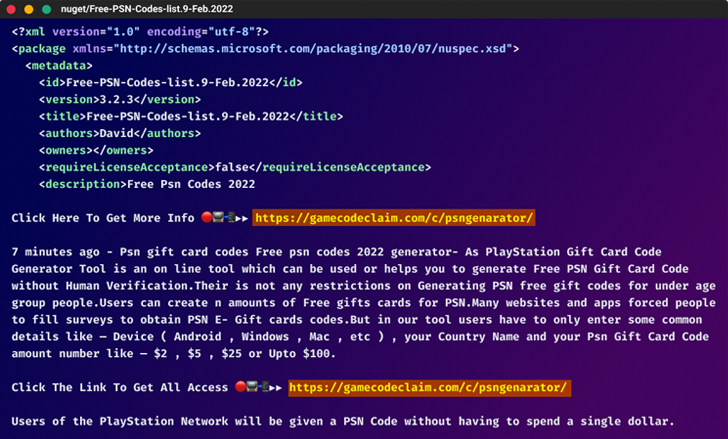
In all, the large campaign encompassed far more than 65,000 exclusive URLs on 90 domains.
“The risk actors powering this marketing campaign probably preferred to boost the research engine optimization (Search engine optimisation) of their phishing web sites by linking them to legit web sites like NuGet,” the researchers claimed. “This highlights the require to be careful when downloading deals and only to use trusted resources.”
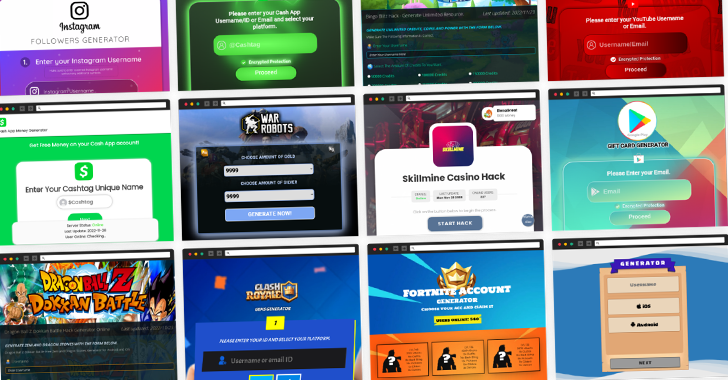
These deceptive and effectively-built internet pages advertised game hacks, “cost-free money” for Income App accounts, present cards, and enhanced followers on social media platforms like YouTube, TikTok, and Instagram.
The web pages, as is generally the circumstance, you should not offer the promised benefits, instead prompting buyers to enter email addresses and entire surveys, just before redirecting them to reputable e-commerce web-sites by means of an affiliate website link to deliver illicit referral revenues.
The poisoning of NuGet, PyPi, and npm with fabricated packages after all over again illustrates the evolving solutions menace actors use to attack the program offer chain.
“Automating the course of action also allowed the attackers to develop a large number of consumer accounts, making it difficult to trace the supply of the attack,” the scientists claimed. “This exhibits the sophistication and willpower of these attackers, who were being eager to make investments sizeable means in buy to carry out this campaign.”
Uncovered this posting fascinating? Stick to us on Twitter and LinkedIn to read more exceptional content we submit.
Some sections of this short article are sourced from:
thehackernews.com

 FBI Charges 6, Seizes 48 Domains Linked to DDoS-for-Hire Service Platforms
FBI Charges 6, Seizes 48 Domains Linked to DDoS-for-Hire Service Platforms