Cybersecurity scientists on Monday tied a string of attacks targeting Accellion File Transfer Equipment (FTA) servers over the previous two months to information theft and extortion campaign orchestrated by a cybercrime team named UNC2546.
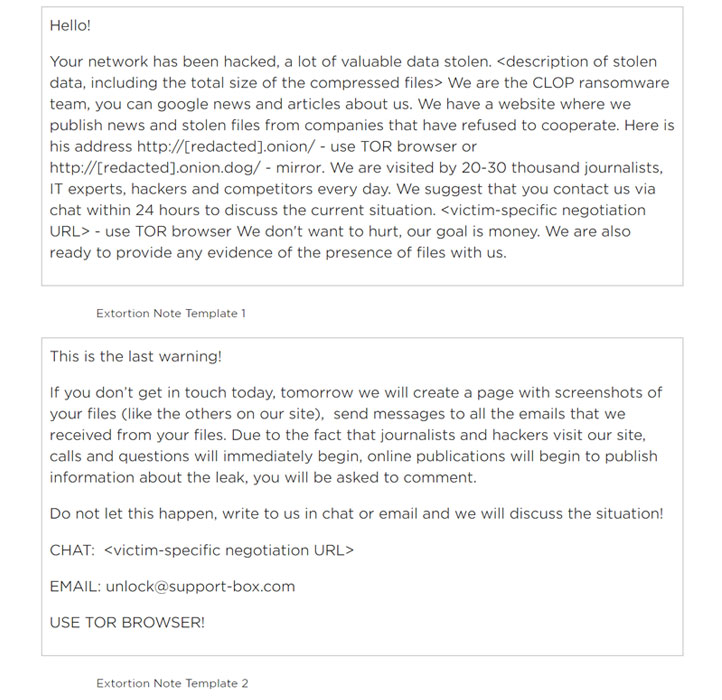
The attacks, which commenced in mid-December 2020, included exploiting a number of zero-working day vulnerabilities in the legacy FTA software program to put in a new web shell named DEWMODE on target networks and exfiltrating delicate information, which was then printed on a information leak web site operated by the CLOP ransomware gang.
But in a twist, no ransomware was actually deployed in any of the recent incidents that hit corporations in the U.S., Singapore, Canada, and the Netherlands, with the actors rather resorting to extortion e-mails to threaten victims into spending bitcoin ransoms.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount

In accordance to Risky Company, some of the providers that have experienced their information shown on the internet site include things like Singapore’s telecom service provider SingTel, the American Bureau of Shipping, legislation business Jones Working day, the Netherlands-dependent Fugro, and everyday living sciences organization Danaher.
Next the slew of attacks, Accellion has patched 4 FTA vulnerabilities that ended up recognized to be exploited by the menace actors, in addition to incorporating new monitoring and alerting capabilities to flag any suspicious conduct. The flaws are as follows –
- CVE-2021-27101 – SQL injection by means of a crafted Host header
- CVE-2021-27102 – OS command execution via a local web service contact
- CVE-2021-27103 – SSRF by way of a crafted Write-up request
- CVE-2021-27104 – OS command execution through a crafted Article request
FireEye’s Mandiant risk intelligence crew, which is leading the incident reaction initiatives, is tracking the abide by-on extortion scheme beneath a independent menace cluster it calls UNC2582 regardless of “compelling” overlaps discovered in between the two sets of destructive activities and preceding attacks carried out by a fiscally inspired hacking team dubbed FIN11.
“Lots of of the businesses compromised by UNC2546 were previously targeted by FIN11,” FireEye reported. “Some UNC2582 extortion emails observed in January 2021 ended up sent from IP addresses and/or email accounts utilised by FIN11 in several phishing strategies among August and December 2020.”
Once put in, the DEWMODE web shell was leveraged to down load data files from compromised FTA cases, main to the victims obtaining extortion emails professing to be from the “CLOP ransomware group” various weeks later on.
Lack of reply in a well timed fashion would result in further email messages despatched to a broader team of recipients in the target firm as well as its companions that contains inbound links to the stolen details, the researchers thorough.
Apart from urging its FTA prospects to migrate to kiteworks, Accellion said fewer than 100 out of 300 overall FTA purchasers had been victims of the attack and that much less than 25 seem to have endured “significant” details theft.
The growth will come immediately after grocery chain Kroger disclosed very last 7 days that HR info, pharmacy documents, and funds services data belonging to some clients could have been compromised as a final result of the Accellion incident.
Identified this posting interesting? Follow THN on Fb, Twitter and LinkedIn to go through more exclusive articles we submit.
Some parts of this write-up are sourced from:
thehackernews.com

 Google Alerts used to launch fake Adobe Flash Player updater
Google Alerts used to launch fake Adobe Flash Player updater