An unknown threat actor has been exploiting a now-patched zero-day flaw in Internet Explorer browser to produce a totally-showcased VBA-based mostly remote access trojan (RAT) able of accessing information saved in compromised Windows methods, and downloading and executing malicious payloads as component of an “unusual” campaign.
The backdoor is dispersed by means of a decoy document named “Manifest.docx” that loads the exploit code for the vulnerability from an embedded template, which, in switch, executes shellcode to deploy the RAT, in accordance to cybersecurity business Malwarebytes, which noticed the suspicious Term file on July 21, 2021.
The malware-laced doc claims to be a “Manifesto of the inhabitants of Crimea” calling on the citizens to oppose Russian President Vladimir Putin and “develop a unified platform referred to as ‘People’s Resistance.'”

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code

The Internet Explorer flaw, tracked as CVE-2021-26411, is noteworthy for the reality that it was abused by the North Korea-backed Lazarus Team to target security researchers functioning on vulnerability investigate and advancement.
Before this February, South Korean cybersecurity business ENKI uncovered the point out-aligned hacking collective had manufactured an unsuccessful attempt at focusing on its security scientists with malicious MHTML data files that, when opened, downloaded two payloads from a remote server, one particular of which contained a zero-working day against Internet Explorer. Microsoft addressed the issue as portion of its Patch Tuesday updates for March.
The Internet Explorer exploit is one of the two strategies which is used to deploy the RAT, with the other technique relying on a social engineering component that includes downloading and executing a remote macro-weaponized template that contains the implant. Irrespective of the an infection chain, the use of double attack vectors is likely an try to enhance the chance of finding a route into the focused devices.
“Even though the two approaches depend on template injection to fall a total-featured distant access trojan, the IE exploit (CVE-2021-26411) previously made use of by the Lazarus APT is an unconventional discovery,” Malwarebytes researcher Hossein Jazi stated in a report shared with The Hacker News. “The attackers may have desired to blend social engineering and exploit to improve their odds of infecting targets.”

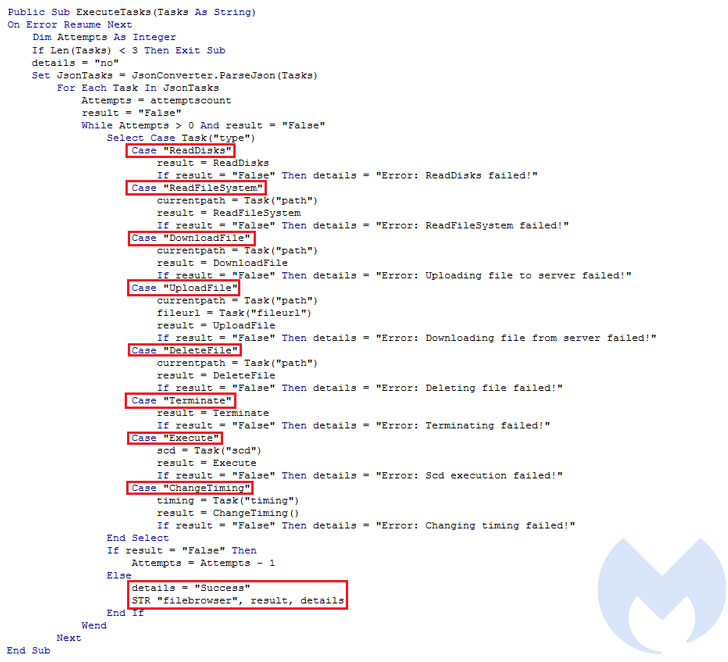
Aside from collecting procedure metadata, the VBA RAT is orchestrated to discover antivirus products and solutions operating on the infected host and execute instructions it gets from an attacker-controlled server, like reading through, deleting, and downloading arbitrary information, and exfiltrate the benefits of all those commands again to the server.
Also found by Malwarebytes is a PHP-dependent panel nicknamed “Ekipa” that’s made use of by the adversary to observe victims and look at information about the modus operandi that led to the profitable breach, highlighting profitable exploitation utilizing the IE zero-working day and the execution of the RAT.
“As the conflict concerning Russia and Ukraine around Crimea continues, cyber attacks have been growing as properly,” Jazi mentioned. “The decoy document contains a manifesto that demonstrates a possible motive (Crimea) and concentrate on (Russian and pro-Russian people today) guiding this attack. On the other hand, it could also have been used as a phony flag.”
Identified this short article appealing? Comply with THN on Fb, Twitter and LinkedIn to study additional special content material we write-up.
Some sections of this report are sourced from:
thehackernews.com


 Top 30 most exploited vulnerabilities since 2020 revealed
Top 30 most exploited vulnerabilities since 2020 revealed