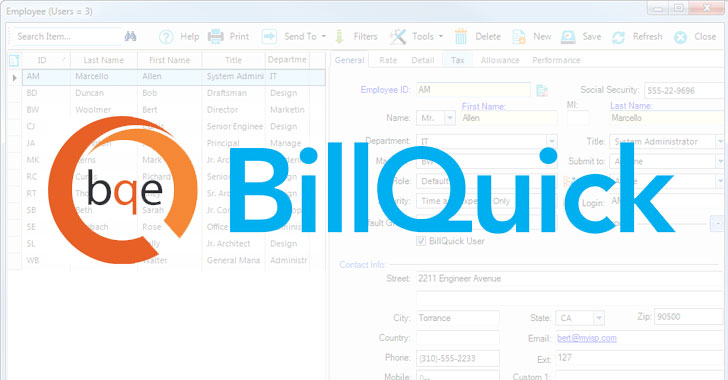
Cybersecurity researchers on Friday disclosed a now-patched critical vulnerability in a number of variations of a time and billing technique termed BillQuick that’s being actively exploited by danger actors to deploy ransomware on susceptible devices.
CVE-2021-42258, as the flaw is getting tracked as, fears an SQL-primarily based injection attack that allows for remote code execution and was effectively leveraged to obtain first access to an unnamed U.S. engineering enterprise and mount a ransomware attack, American cybersecurity business Huntress Labs explained.


Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
When the issue has been tackled by BQE Program, 8 other undisclosed security issues that have been recognized as element of the investigation are but to be patched. According to its website, BQE Software’s products and solutions are utilised by 400,000 people worldwide.
“Hackers can use this to accessibility customers’ BillQuick info and operate destructive instructions on their on-premises Windows servers,” Huntress Labs threat researcher Caleb Stewart stated in a write-up. “This incident highlights a repeating sample plaguing SMB software program: well-proven distributors are accomplishing really minor to proactively secure their programs and matter their unwitting consumers to sizeable legal responsibility when delicate info is inevitably leaked and/or ransomed.”
Essentially, the vulnerability stems from how BillQuick Web Suite 2020 constructs SQL database queries, enabling attackers to inject a specially-crafted SQL by using the application’s login sort that could be made use of to remotely spawn a command shell on the fundamental Windows operating procedure and obtain code execution, which, in turn, is produced doable by the fact that the computer software operates as the “System Administrator” user.
“Hackers are continually hunting for lower-hanging fruit and vulnerabilities that can be exploited—and they’re not usually poking around in ‘big’ mainstream apps like Office,” Stewart said. “Occasionally, a productiveness instrument or even an add-on can be the doorway that hackers action via to obtain obtain to an ecosystem and have out their upcoming go.”
Uncovered this write-up exciting? Stick to THN on Facebook, Twitter and LinkedIn to browse much more unique articles we put up.
Some sections of this posting are sourced from:
thehackernews.com

 NYT Journalist Repeatedly Hacked with Pegasus after Reporting on Saudi Arabia
NYT Journalist Repeatedly Hacked with Pegasus after Reporting on Saudi Arabia