Unidentified menace actors are actively exploiting a critical authentication bypass vulnerability to hijack household routers as element of an exertion to co-decide them to a Mirai-variant botnet utilized for carrying out DDoS attacks, just two times following its general public disclosure.
Tracked as CVE-2021-20090 (CVSS score: 9.9), the weakness worries a path traversal vulnerability in the web interfaces of routers with Arcadyan firmware that could permit unauthenticated remote attackers to bypass authentication.


Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
Disclosed by Tenable on August 3, the issue is thought to have existed for at minimum 10 decades, affecting at minimum 20 versions across 17 various suppliers, like Asus, Beeline, British Telecom, Buffalo, Deutsche Telekom, Orange, Telstra, Telus, Verizon, and Vodafone.
Productive exploitation of the could permit an attacker to circumvent authentication barriers and possibly gain obtain to sensitive information and facts, including legitimate request tokens, which could be used to make requests to alter router configurations.
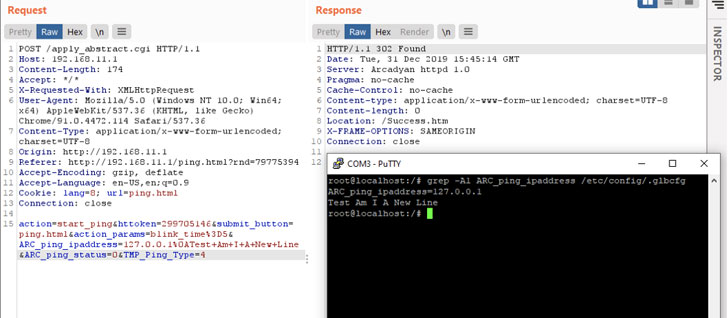
Juniper Risk Labs last week explained it “determined some attack designs that try to exploit this vulnerability in the wild coming from an IP address situated in Wuhan, Hubei province, China” commencing on August 5, with the attacker leveraging it to deploy a Mirai variant on the affected routers, mirroring related tactics discovered by Palo Alto Networks’ Unit 42 earlier this March.
“The similarity could show that the very same threat actor is powering this new attack and trying to upgrade their infiltration arsenal with yet an additional freshly disclosed vulnerability,” the researchers explained.

Aside from CVE-2021–20090, the danger actor carried out attacks leveraging a quantity of other vulnerabilities, this sort of as –
- CVE-2020-29557 (Pre-authentication distant code execution in D-Backlink DIR-825 R1 gadgets)
- CVE-2021-1497 and CVE-2021-1498 (Command injection vulnerabilities in Cisco HyperFlex HX)
- CVE-2021-31755 (Stack buffer overflow vulnerability in Tenda AC11 leading to arbitrary code execution)
- CVE-2021-22502 (Remote code execution flaw in Micro Concentrate Procedure Bridge Reporter)
- CVE-2021-22506 (Facts Leakage vulnerability in Micro Focus Access Supervisor)
Device 42’s report had beforehand uncovered as lots of as 6 recognised and three unidentified security flaws that have been exploited in the attacks, counting these focused at SonicWall SSL-VPNs, D-Website link DNS-320 firewalls, Netis WF2419 wi-fi routers, and Netgear ProSAFE Plus switches.
To keep away from any opportunity compromise, consumers are encouraged to update their router firmware to the most current model.
“It is crystal clear that danger actors keep an eye on all disclosed vulnerabilities. Each time an exploit PoC is printed, it frequently can take them really tiny time to combine it into their system and start attacks,” the researchers explained.
Discovered this article exciting? Abide by THN on Facebook, Twitter and LinkedIn to study far more exceptional written content we publish.
Some pieces of this write-up are sourced from:
thehackernews.com


 ‘Glowworm’ Attack Turns Power Light Flickers into Audio
‘Glowworm’ Attack Turns Power Light Flickers into Audio