The recently disclosed critical Spring4Shell vulnerability is staying actively exploited by risk actors to execute the Mirai botnet malware, specifically in the Singapore area given that the start off of April 2022.
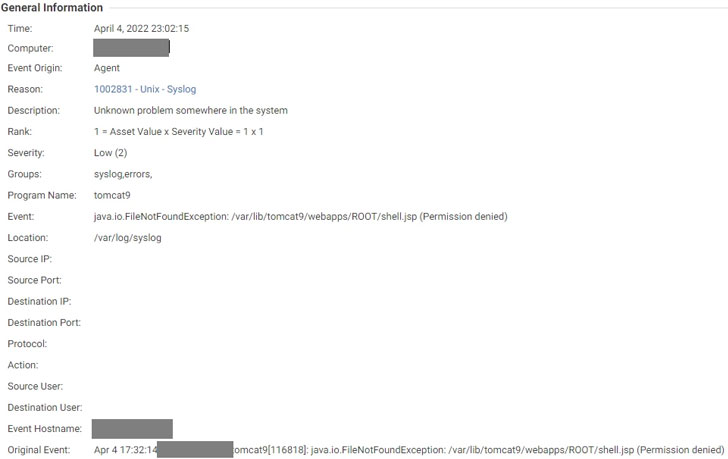
“The exploitation lets menace actors to down load the Mirai sample to the ‘/tmp’ folder and execute them following permission transform making use of ‘chmod,'” Pattern Micro scientists Deep Patel, Nitesh Surana, Ashish Verma mentioned in a report revealed Friday.
Tracked as CVE-2022-22965 (CVSS score: 9.8), the vulnerability could permit destructive actors to achieve distant code execution in Spring Main programs underneath non-default situations, granting the attackers entire control above the compromised devices.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
The improvement will come as the U.S. Cybersecurity and Infrastructure Security Company (CISA) previously this 7 days added the Spring4Shell vulnerability to its Regarded Exploited Vulnerabilities Catalog based mostly on “evidence of lively exploitation.”
This is far from the 1st time the botnet operators have swiftly moved to add newly publicized flaws to their exploit toolset. In December 2021, multiple botnets which include Mirai and Kinsing ended up uncovered leveraging the Log4Shell vulnerability to breach prone servers on the internet.
Mirai, which means “foreseeable future” in Japanese, is the identify specified to a Linux malware that has continued to goal networked intelligent household units these as IP cameras and routers and link them with each other into a network of contaminated equipment regarded as a botnet.
The IoT botnet, using the herd of hijacked components, can be then utilized to dedicate further attacks, such as massive-scale phishing attacks, cryptocurrency mining, simply click fraud, and distributed denial-of-assistance (DDoS) attacks.
To make issues worse, the leak of Mirai’s supply code in October 2016 has presented beginning to numerous variants these kinds of as Okiru, Satori, Masuta, and Reaper, building it an ever-mutating menace.
Before this January, cybersecurity company CrowdStrike observed that malware hitting Linux programs improved by 35% in 2021 in comparison to 2020, with XOR DDoS, Mirai, and Mozi malware family members accounting for additional than 22% of Linux-specific threats noticed in the calendar year.
“The principal function of these malware households is to compromise vulnerable internet-related units, amass them into botnets, and use them to accomplish distributed denial-of-services (DDoS) attacks,” the researchers reported.
Identified this write-up exciting? Follow THN on Fb, Twitter and LinkedIn to go through much more distinctive material we write-up.
Some sections of this short article are sourced from:
thehackernews.com


 Chinese Hacker Groups Continue to Target Indian Power Grid Assets
Chinese Hacker Groups Continue to Target Indian Power Grid Assets