Cybersecurity researchers on Thursday disclosed information of a beforehand undiscovered in-memory Windows backdoor made by a hacker-for-use procedure that can execute remotely malicious code and steal delicate details from its targets in Asia, Europe, and the US.
Dubbed “PowerPepper” by Kaspersky researchers, the malware has been attributed to the DeathStalker team (previously termed Deceptikons), a risk actor that has been located to strike regulation firms and companies in the money sector located in Europe and the Middle East at minimum since 2012.
The hacking resource is so-known as simply because of its reliance on steganographic trickery to provide the backdoor payload in the kind of an graphic of ferns or peppers.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
The espionage team to start with came to light earlier this July, with most of their attacks commencing with a spear-phishing email containing a malicious modified LNK (shortcut) file that, when clicked, downloads and runs a PowerShell-centered implant named Powersing.
Even though their objectives you should not surface to be fiscally inspired, their continued fascination in collecting essential company facts led Kaspersky to the conclusion that “DeathStalker is a group of mercenaries supplying hacking-for-seek the services of solutions, or acting as some type of data broker in financial circles.”
PowerPepper now joins the group’s checklist of growing and evolving toolsets.
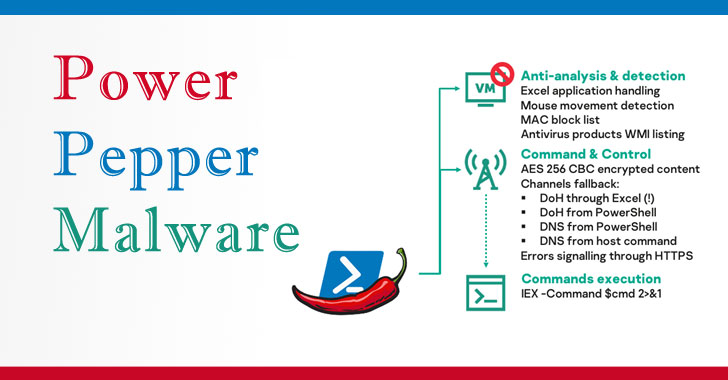
Spotted in the wild in mid-July 2020, this new strain of malware receives dropped from a decoy Term doc and leverages DNS over HTTPS (DoH) as a communications channel to transmit encrypted destructive shell instructions from an attacker-managed server.
The spear-phishing emails arrive with themes as diversified as carbon emission laws, journey booking, and the ongoing coronavirus pandemic, with the Word files obtaining social engineering banners urging people to allow macros in a bid to lure an unsuspecting user into downloading the backdoor.
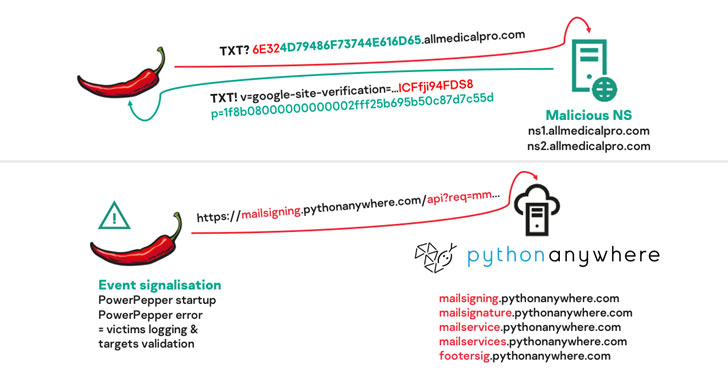
To obtain its objectives, the implant sends DNS requests to name servers — servers that retail outlet the DNS data — related with a malicious C2 area, which then sends back the command to be run in the kind of an embedded response. On execution, the final results are beamed to the server by a batch of DNS requests.
Moreover leveraging macro-primarily based and LNK-primarily based shipping chains to deploy the malware, DeathStalker used “obfuscation, execution and masquerading methods to hinder detection, or deceive targets that are curious about what is taking place on their personal computers,” Kaspersky’s Pierre Delcher pointed out.
Main among them are the capabilities to conceal destructive execution workflow in Word embedded form and object homes and use Windows Compiled HTML Enable (CHM) data files as archives for malicious data files.
Multiple mercenary teams have been found in the wild ahead of, like BellTroX (aka Dark Basin), Bahamut, and CostaRicto, all of whom have deployed tailor made malware to breach devices belonging to financial institutions and govt officials.
“It only would seem fair to create that DeathStalker experimented with really hard to establish evasive, imaginative and intricate instruments with this PowerPepper implant and related delivery chains,” Delcher concluded.
“There is very little especially refined about the methods and tricks that are leveraged, nonetheless the whole toolset has proved to be successful, is really very well put jointly, and demonstrates decided initiatives to compromise several targets all around the globe.”
To safeguard towards PowerPepper supply and execution, it is encouraged that companies and customers update their CMS backends as nicely as involved plugins, restrict PowerShell use on stop-user computer systems with enforced execution policies, and refrain from opening Windows shortcuts attached to emails, or click hyperlinks in emails from unfamiliar senders.
Uncovered this article attention-grabbing? Abide by THN on Facebook, Twitter and LinkedIn to read through far more distinctive written content we article.
Some components of this posting are sourced from:
thehackernews.com

 Eli Lily CISO on COVID vaccine suppliers: ‘My biggest concern is their being aware they are a target’
Eli Lily CISO on COVID vaccine suppliers: ‘My biggest concern is their being aware they are a target’