Risk actors are progressively banking on the system of HTML smuggling in phishing strategies as a usually means to get preliminary access and deploy an array of threats, which includes banking malware, remote administration trojans (RATs), and ransomware payloads.
Microsoft 365 Defender Risk Intelligence Crew, in a new report revealed Thursday, disclosed that it determined infiltrations distributing the Mekotio banking Trojan, backdoors these as AsyncRAT and NjRAT, and the notorious TrickBot malware. The multi-staged attacks — dubbed ISOMorph — had been also publicly documented by Menlo Security in July 2021.


Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
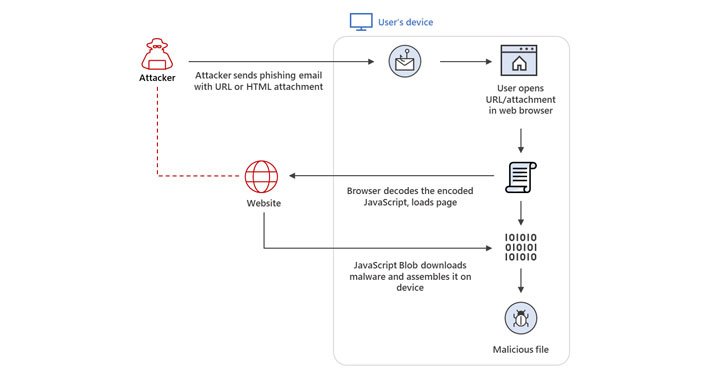
HTML smuggling is an approach that allows an attacker to “smuggle” 1st-stage droppers, generally encoded destructive scripts embedded inside specially-crafted HTML attachment or web web pages, on a victim device by using edge of simple features in HTML5 and JavaScript alternatively than exploiting a vulnerability or a design flaw in present day web browsers.
By performing so, it allows the danger actor to assemble the payloads programmatically on the HTML page applying JavaScript, alternatively of having to make an HTTP ask for to fetch a useful resource on a web server, although also at the same time evading perimeter security alternatives. The HTML droppers are then applied to fetch the main malware to be executed on the compromised endpoints.
“When a target person opens the HTML in their web browser, the browser decodes the malicious script, which, in convert, assembles the payload on the host gadget,” the researchers stated. “As a result, alternatively of having a malicious executable go directly through a network, the attacker builds the malware domestically at the rear of a firewall.”
HTTP Smuggling’s potential to bypass web proxies and email gateways have manufactured it a lucrative system among the point out-sponsored actors and cybercriminal teams to produce malware in serious-planet attacks, Microsoft pointed out.
Nobelium, the menace team driving the SolarWinds offer chain hack, was observed leveraging this pretty tactic to provide a Cobalt Strike Beacon as portion of a refined email-dependent attack aimed at government agencies, feel tanks, consultants, and non-governmental corporations positioned throughout 24 nations around the world, which include the U.S., earlier this May.

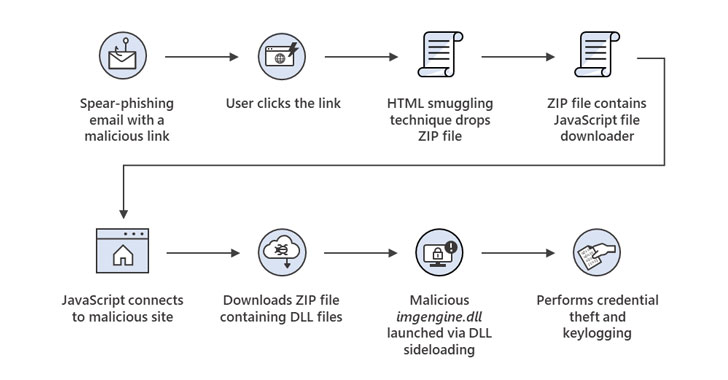
Over and above espionage operations, HTML smuggling has also been embraced for banking malware attacks involving the Mekotio trojan, what with the adversaries sending spam email messages made up of a destructive link that, when clicked, triggers the obtain of a ZIP file, which, in turn, has a JavaScript file downloader to retrieve binaries able of credential theft and keylogging.
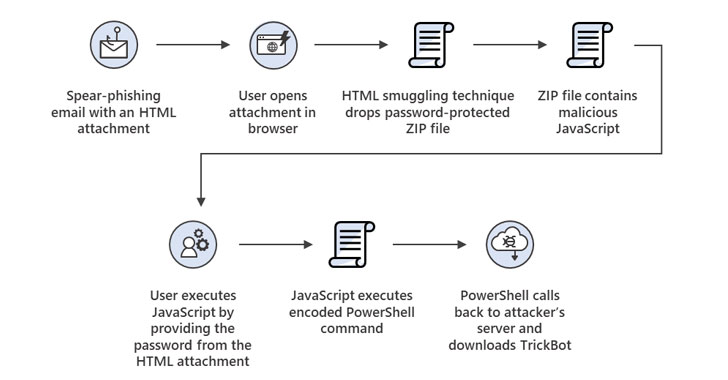
But in a sign that other actors are having observe and incorporating HTML smuggling in their arsenal, a September email marketing campaign carried out by DEV-0193 was uncovered, abusing the similar technique to provide TrickBot. The attacks entail a destructive HTML attachment, which, when opened on a web browser, generates a password-secured JavaScript file on the recipient’s system, prompting the sufferer to provide the password from the unique HTML attachment.
Performing so initiates the execution of the JavaScript code, which subsequently launches a Foundation64-encoded PowerShell command to make contact with an attacker-controlled server to download the TrickBot malware, in the end paving the way for stick to-on ransomware attacks.
“The surge in the use of HTML smuggling in email campaigns is an additional instance of how attackers preserve refining distinct components of their attacks by integrating remarkably evasive tactics,” Microsoft pointed out. “Such adoption displays how tactics, techniques, and strategies (TTPs) trickle down from cybercrime gangs to destructive risk actors and vice versa. It also reinforces the present state of the underground economic system, in which this sort of TTPs get commoditized when deemed effective.”
Identified this write-up attention-grabbing? Abide by THN on Fb, Twitter and LinkedIn to read through more special information we article.
Some parts of this posting are sourced from:
thehackernews.com

 Europol: Ransomware Gangs Focusing on High Profile Targets
Europol: Ransomware Gangs Focusing on High Profile Targets