3 different point out-sponsored menace actors aligned with China, India, and Russia have been noticed adopting a new method termed RTF (aka Loaded Textual content Structure) template injection as section of their phishing strategies to deliver malware to targeted techniques.
“RTF template injection is a novel strategy that is suitable for malicious phishing attachments simply because it is straightforward and enables danger actors to retrieve destructive articles from a remote URL using an RTF file,” Proofpoint scientists reported in a new report shared with The Hacker News.


Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
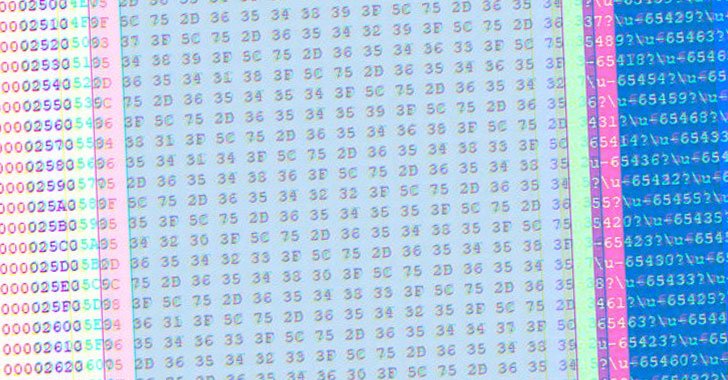
At the coronary heart of the attack is an RTF file containing decoy content material that can be manipulated to empower the retrieval of content, such as destructive payloads, hosted at an external URL upon opening an RTF file. Specifically, it leverages the RTF template features to alter a document’s formatting attributes working with a hex editor by specifying a URL source as an alternative of an available file source vacation spot from which a remote payload may be retrieved.
Put in different ways, the idea is that attackers can send out malicious Microsoft Word documents to targeted victims that surface fully innocuous but are designed to load destructive code by way of the template function remotely.
So when an altered RTF file is opened by means of Microsoft Word, the software will commence to down load the source from the specified URL prior to exhibiting the lure information of the file. It really is consequently not stunning that the procedure is being more and more weaponized by threat actors to distribute malware.
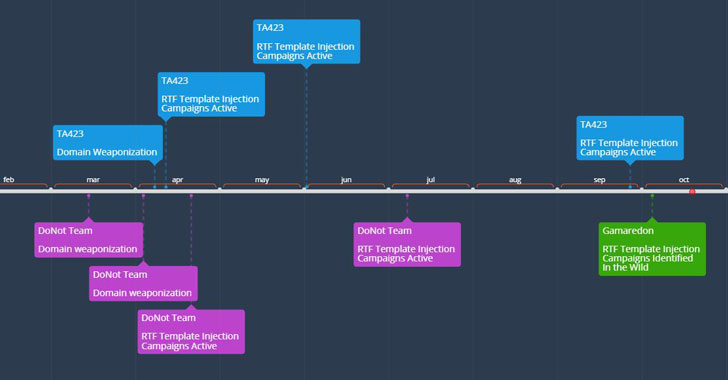
Proofpoint explained it noticed Template injection RTF documents linked to the APT groups DoNot Team, Gamaredon, and a Chinese-relevant APT actor dubbed TA423 as early as February 2021, with the adversaries employing the data files to goal entities in Pakistan, Sri Lanka, Ukraine, and those running in the deep water electrical power exploration sector in Malaysia by means of defense-themed and other country-particular lures.

Although the DoNot Crew has been suspected of carrying out cyber attacks that are aligned with Indian-state passions, Gamaredon was just lately outed by Ukrainian legislation enforcement as associates of Russia’s Federal Security Assistance (FSB) with a propensity for placing the public and non-public sector in the state for harvesting categorised information from compromised Windows programs for geopolitical gains.
“The innovation by risk actors to convey this approach to a new file type in RTFs represents an increasing area spot of risk for organizations around the globe,” the researchers said. “Whilst this technique at this time is applied by a confined quantity of APT actors with a array of sophistication, the technique’s usefulness put together with its simplicity of use is most likely to travel its adoption further more across the menace landscape.”
Located this write-up interesting? Abide by THN on Fb, Twitter and LinkedIn to study additional exclusive articles we article.
Some sections of this write-up are sourced from:
thehackernews.com

 Access brokers are making it easier for ransomware operators to attack businesses
Access brokers are making it easier for ransomware operators to attack businesses