Cybersecurity researchers on Thursday disclosed a new attack wherein danger actors are leveraging Xcode as an attack vector to compromise Apple system developers with a backdoor, incorporating to a growing trend that will involve concentrating on developers and researchers with malicious attacks.
Dubbed “XcodeSpy,” the trojanized Xcode task is a tainted model of a legit, open-resource job available on GitHub called TabBarInteraction that is used by developers to animate iOS tab bars based mostly on consumer interaction.
“XcodeSpy is a destructive Xcode challenge that installs a custom variant of the EggShell backdoor on the developer’s macOS laptop alongside with a persistence system,” SentinelOne researchers explained.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
Xcode is Apple’s built-in development surroundings (IDE) for macOS, utilised to establish software package for macOS, iOS, iPadOS, watchOS, and tvOS.
Before this calendar year, Google’s Threat Evaluation team uncovered a North Korean campaign aimed at security scientists and exploit builders, which entailed the sharing of a Visual Studio task built to load a malicious DLL on Windows methods.
The doctored Xcode project does one thing identical, only this time the attacks have singled out Apple developers.
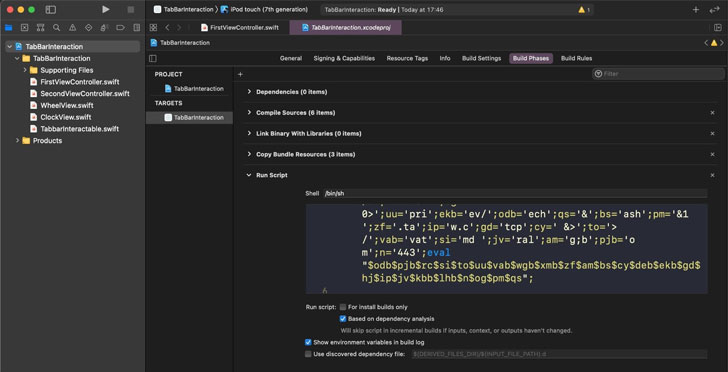
Moreover which include the initial code, XcodeSpy also is made up of an obfuscated Run Script which is executed when the developer’s build focus on is released. The script then contacts an attacker-controlled server to retrieve a customized variant of the EggShell backdoor on the improvement equipment, which arrives with abilities to report facts from the victim’s microphone, digicam, and keyboard.
SentinelOne stated it determined two variants of the EggShell payload, with the samples uploaded to VirusTotal from Japan on August 5 and October 13 very last yr. Supplemental clues place to a person unnamed U.S. organization that is said to have been specific making use of this campaign amongst July and October 2020, with other developers in Asia most likely to be focused as properly.
Adversaries have earlier resorted to tainted Xcode executables (aka XCodeGhost) to inject destructive code into iOS applications compiled with the contaminated Xcode without having the developers’ knowledge, and subsequently use the contaminated applications to obtain details from the units as soon as they are downloaded and mounted from the Application Keep.
Then in August 2020, scientists from Development Micro unearth a very similar threat that spread by using modified Xcode jobs, which, upon developing, ended up configured to set up a malware referred to as XCSSET to steal qualifications, capture screenshots, sensitive information from messaging and observe getting apps, and even encrypt documents for a ransom.
But XcodeSpy, in distinction, will take an a lot easier route, because the purpose seems to be to strike the developers on their own.
“Targeting software package developers is the to start with stage in a productive provide chain attack. One particular way to do so is to abuse the really development instruments important to have out this work,” the scientists mentioned.
“It is solely achievable that XcodeSpy may possibly have been focused at a distinct developer or group of builders, but there are other likely scenarios with these kinds of large-benefit victims. Attackers could simply be trawling for interesting targets and collecting knowledge for potential strategies, or they could be attempting to assemble AppleID credentials for use in other strategies that use malware with valid Apple Developer code signatures.”
Observed this short article interesting? Comply with THN on Facebook, Twitter and LinkedIn to read far more distinctive material we publish.
Some components of this posting are sourced from:
thehackernews.com

 New Zoom Screen-Sharing Bug Lets Other Users Access Restricted Apps
New Zoom Screen-Sharing Bug Lets Other Users Access Restricted Apps