Network security options supplier Fortinet verified that a malicious actor experienced unauthorizedly disclosed VPN login names and passwords affiliated with 87,000 FortiGate SSL-VPN gadgets.
“These qualifications have been attained from units that remained unpatched from CVE-2018-13379 at the time of the actor’s scan. Even though they might have because been patched, if the passwords were being not reset, they stay susceptible,” the corporation stated in a assertion on Wednesday.
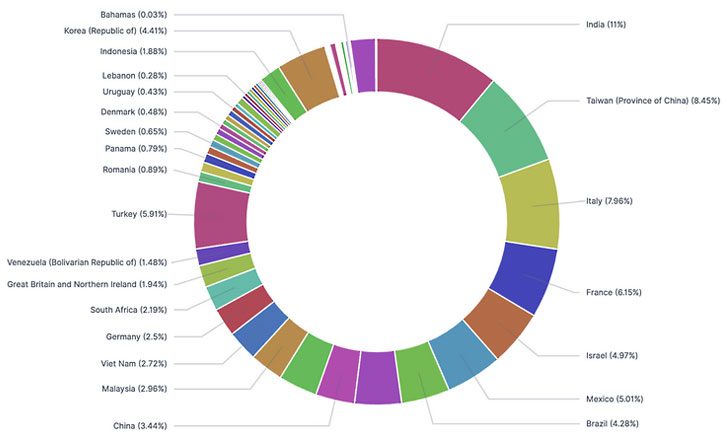
The disclosure will come just after the risk actor leaked a checklist of Fortinet qualifications for no cost on a new Russian-talking forum known as RAMP that released in July 2021 as very well as on Groove ransomware’s facts leak web page, with Advanced Intel noting that the “breach record has uncooked entry to the top rated corporations” spanning throughout 74 nations around the world, like India, Taiwan, Italy, France, and Israel. “2,959 out of 22,500 victims are U.S. entities,” the researchers reported.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
CVE-2018-13379 relates to a path traversal vulnerability in the FortiOS SSL VPN web portal, which lets unauthenticated attackers to read through arbitrary procedure data files, such as the session file, which incorporates usernames and passwords saved in plaintext.
Although the weak point was rectified in May well 2019, the security weak spot has been regularly exploited by a number of adversaries to deploy an array of malicious payloads on unpatched equipment, prompting Fortinet to issue a series of advisories in August 2019, July 2020, April 2021, and again in June 2021, urging consumers to upgrade affected appliances.
CVE-2018-13379 also emerged as 1 of the top most exploited flaws in 2020, according to a checklist compiled by intelligence businesses in Australia, the U.K., and the U.S. before this yr.
In gentle of the leak, Fortinet is recommending providers to right away disable all VPNs, upgrade the units to FortiOS 5.4.13, 5.6.14, 6..11, or 6.2.8 and above followed by initiating an group-extensive password reset, warning that “you may continue to be vulnerable write-up-update if your users’ qualifications had been beforehand compromised.”
Discovered this report appealing? Abide by THN on Facebook, Twitter and LinkedIn to read additional exceptional content we put up.
Some sections of this write-up are sourced from:
thehackernews.com


 CISA Warns of Actively Exploited Zoho ManageEngine ADSelfService Vulnerability
CISA Warns of Actively Exploited Zoho ManageEngine ADSelfService Vulnerability