A formerly unknown hacking group has been connected to targeted attacks in opposition to human legal rights activists, human rights defenders, academics, and lawyers throughout India in an endeavor to plant “incriminating electronic proof.”
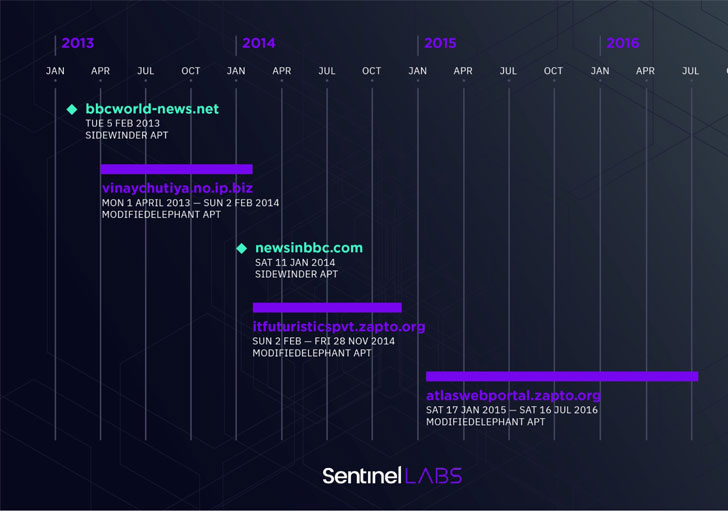
Cybersecurity company SentinelOne attributed the intrusions to a group it tracks as “ModifiedElephant,” an elusive risk actor that is been operational due to the fact at minimum 2012, whose exercise aligns sharply with Indian point out passions.
“ModifiedElephant operates through the use of commercially out there distant entry trojans (RATs) and has prospective ties to the business surveillance marketplace,” the researchers claimed. “The risk actor employs spear-phishing with malicious files to deliver malware, such as NetWire, DarkComet, and basic keyloggers.”

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount

The primary intention of ModifiedElephant is to aid lengthy-phrase surveillance of focused individuals, finally foremost to the supply of “proof” on the victims’ compromised techniques with the objective of framing and incarcerating susceptible opponents.
Noteworthy targets involve persons affiliated with the 2018 Bhima Koregaon violence in the Indian point out of Maharashtra, SentinelOne researchers Tom Hegel and Juan Andres Guerrero-Saade mentioned in a report.
The attack chains include infecting the targets — some of them numerous instances in a single working day — applying spear-phishing emails themed all-around matters similar to activism, weather transform, and politics, and that contains malicious Microsoft Office document attachments or back links to data files hosted externally that are weaponized with malware capable of getting command of victim machines.
“The phishing email messages just take many techniques to gain the appearance of legitimacy,” the scientists stated. “This consists of pretend human body written content with a forwarding history that contains very long lists of recipients, authentic email receiver lists with several seemingly faux accounts, or simply just resending their malware a number of occasions employing new e-mails or lure files.”
Also distributed making use of phishing e-mail is an unknown commodity trojan concentrating on Android that enables the attackers to intercept and control SMS and contact data, wipe or unlock the system, conduct network requests, and remotely administer the contaminated equipment. SentinelOne characterised it as an “best reduced-cost cell surveillance toolkit.”
“This actor has operated for decades, evading research awareness and detection thanks to their constrained scope of functions, the mundane nature of their applications, and their regionally- specific targeting,” the scientists mentioned.
Found this posting intriguing? Follow THN on Fb, Twitter and LinkedIn to read through much more special written content we put up.
Some parts of this short article are sourced from:
thehackernews.com



 Half of Global Emails Were Spam in 2021
Half of Global Emails Were Spam in 2021